After Brian Krebs reported the September arrests of alleged key figures in the cyber crime gang that developed and operated Dridex, Unit 42 observed a marked decrease in activity related to this banking Trojan – at least until today. Dridex re-entered the threat landscape with a major e-mail phishing campaign. Leveraging the Palo Alto Networks AutoFocus platform, we identified samples associated with this resurgence.
Malware
True to form, the Dridex crew continues to utilize Microsoft Word Doc files with embedded macros, just as they did at the start of 2015. The Bartalex kit, a favorite for various cybercriminals, constructs these macros to deliver their malicious payload. When a user opens the malicious document, the macro code reaches out to a URL and downloads the Dridex executable. We identified the following associated Microsoft Word Doc files and URLs from today’s campaign:
SHA256: 2a12822134b4c3f1396212e04bc462fdf23082a55fdbc15e91722d07d54fd4b2
Payload: www.norlabs[.]de/123/1111.exe
SHA256: c1e8fce5b72da6f2ce43920ca9e6574750f7e994c51f6084e90c115fe9d2b804
Payload: www.ifdcsanluis.edu[.]ar/123/1111.exe
SHA256: 6cfcf501aeaa319b576af713fef10e227775e59e82224d1182d309be5dc80bd
Payload: hobby-hangar[.]net/123/1111.exe
SHA256: 761b17c4f926c403813b5c2c4c79f3d64c3b5d5a96e841e454fd5791e56f67db
Payload: zahnrad-ruger[.]de/123/1111.exe
SHA256: 436c99c88ea0a7312f3d60b127d0735e4698599b2f83b4df3a1dc67764235256
Payload: miastolomza[.]pl/123/1111.exe
The 1111.exe payload for each of these DOC files corresponds to the following file:
SHA256: a497de7f2488f093aa74562695a2ce705cbddbd2c4a357f5c785f23ea7450f43
As of today, only 17 out of the 56 VirusTotal Anti-Virus (AV) scanners recognize the Doc files associated with this resurgence as malicious, and only two recognize the associated implant. The Palo Alto Networks AutoFocus platform correctly identifies all components of this threat under the Unit 42 Dridex tag.
Targeting and Delivery
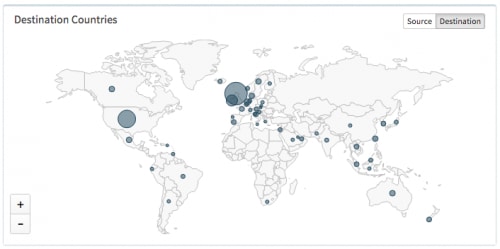
Our analysis revealed that this return of Dridex is heavily targeted at the United Kingdom (UK).
AutoFocus map of today's Dridex targets
Dynamoo’s Blog (Conrad Longmore) posted an example of one of this latest series of Dridex phishing messages. The malicious Doc files that we identified all employ a similar order theme in their naming convention (e.g., “Order-SO00653333-1.doc”), requesting that the recipient print out the attachment. While this phishing lure is not particularly sophisticated, it remains surprisingly effective for fulfilling the malicious actor’s objective.
Conclusion
Cybercriminals – especially those that have established prosperity and longevity – will continue to present threats to enterprises and home users alike, despite any setbacks as a result of arrests or other operational challenges. Even though key players in the Dridex crew may have been removed from the equation for the time being, the organization that they leave behind could very well remain viable; alternatively, other criminal groups are always waiting in the wing to assume control of certain endeavors should a vacuum or opportunity present itself. The October 2015 resurgence of Dridex is an example of how these threats continue to adapt and evolve.
Indicators
| Category | Type | Value |
| Delivery | SHA256 | 2a12822134b4c3f1396212e04bc462fdf23082a55fdbc15e91722d07d54fd4b2 |
| Delivery | SHA256 | c1e8fce5b72da6f2ce43920ca9e6574750f7e994c51f6084e90c115fe9d2b804 |
| Delivery | SHA256 | a6cfcf501aeaa319b576af713fef10e227775e59e82224d1182d309be5dc80bd |
| Delivery | SHA256 | 761b17c4f926c403813b5c2c4c79f3d64c3b5d5a96e841e454fd5791e56f67db |
| Delivery | SHA256 | 436c99c88ea0a7312f3d60b127d0735e4698599b2f83b4df3a1dc67764235256 |
| Implant | SHA256 | a497de7f2488f093aa74562695a2ce705cbddbd2c4a357f5c785f23ea7450f43 |
| Download | URL | www.norlabs[.]de/123/1111.exe |
| Download | URL | www.ifdcsanluis.edu[.]ar/123/1111.exe |
| Download | URL | hobby-hangar[.]net/123/1111.exe |
| Download | URL | zahnrad-ruger[.]de/123/1111.exe |
| Download | URL | miastolomza[.]pl/123/1111.exe |
| C2 | IP | 136.243.237.218 |
| C2 | IP | 66.171.247.166 |
| C2 | IP | 88.151.246.80 |
| C2 | IP | 195.251.250.37 |
| C2 | IP | 82.118.24.167 |
| C2 | IP | 92.51.129.33 |
| C2 | IP | 198.61.187.234 |












 Get updates from Unit 42
Get updates from Unit 42