Executive Summary
Since August 2025, Unit 42 has tracked a series of sophisticated phishing campaigns where attackers impersonate Palo Alto Networks talent acquisition staff. These attacks specifically target senior-level professionals by leveraging scraped LinkedIn data to craft highly personalized lures.
The specific attack vector uses social engineering to manufacture a bureaucratic barrier regarding the candidate’s curriculum vitae (CV) and push the candidate toward taking actions such as reformatting their resumes for a fee.
Aspects of this social engineering consist of:
- Initial outreach: Attackers pose as company representatives, sending emails that appear legitimate to establish rapport with senior candidates.
- The lure: The attacker's technique involves falsely claiming that a candidate's resume failed to meet the applicant tracking system (ATS) requirements. The ATS is an online tool designed to analyze resumes for proper formatting, structure and keyword optimization, ensuring they pass automated filters before reaching human recruiters.
- The scam: The attackers offer to bridge this manufactured barrier to assist the candidate in acquiring a position for a fee.
Unit 42 recently published information on the psychology of phishing.
Palo Alto Networks also offers interim guidance to help protect your professional identity and finances, as well as recommendations for what to do if you believe you’ve been targeted.
The Unit 42 Incident Response team can also be engaged to help with a compromise or to provide a proactive assessment to lower your risk.
| Related Unit 42 Topics | Phishing, Spear Phishing, Scams |
Current Scope of the Attack
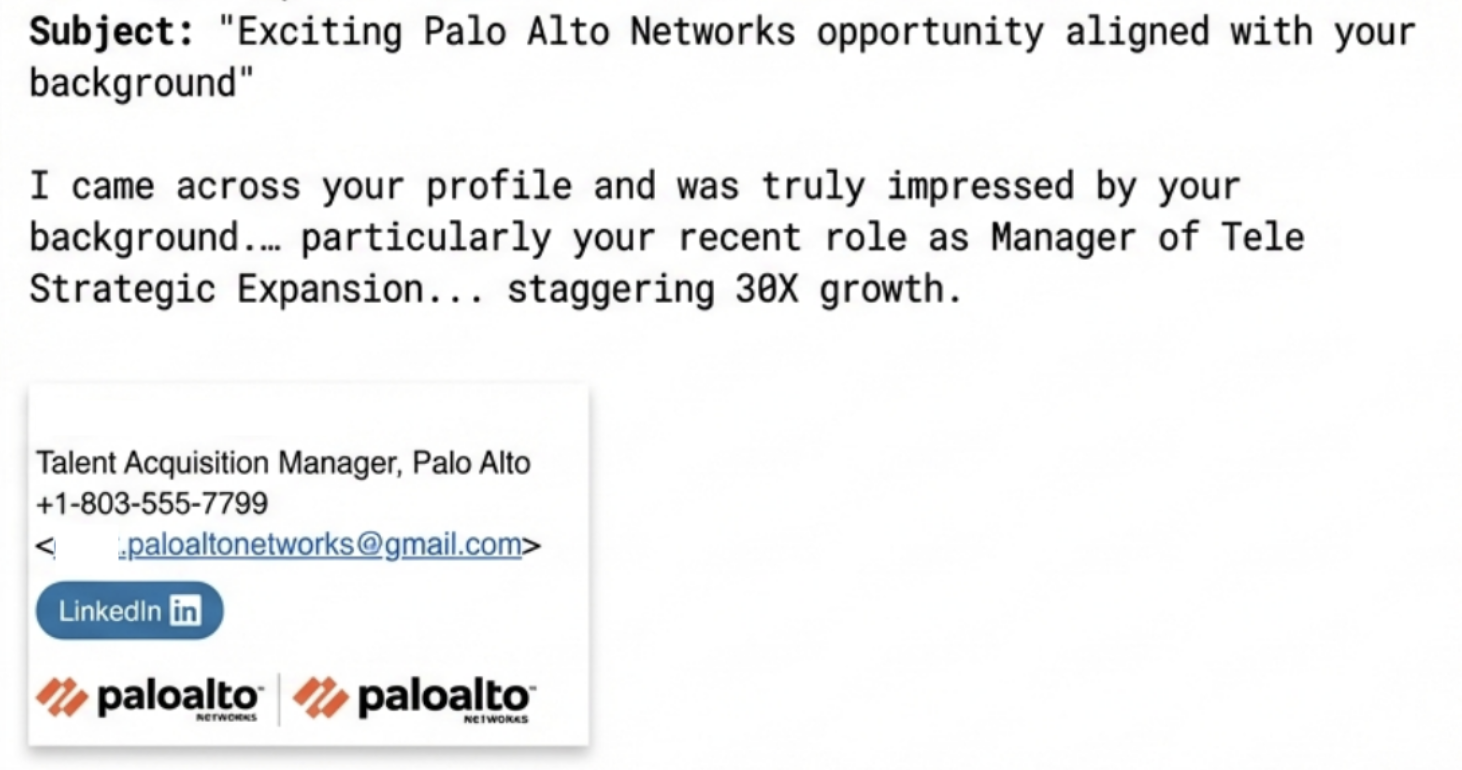
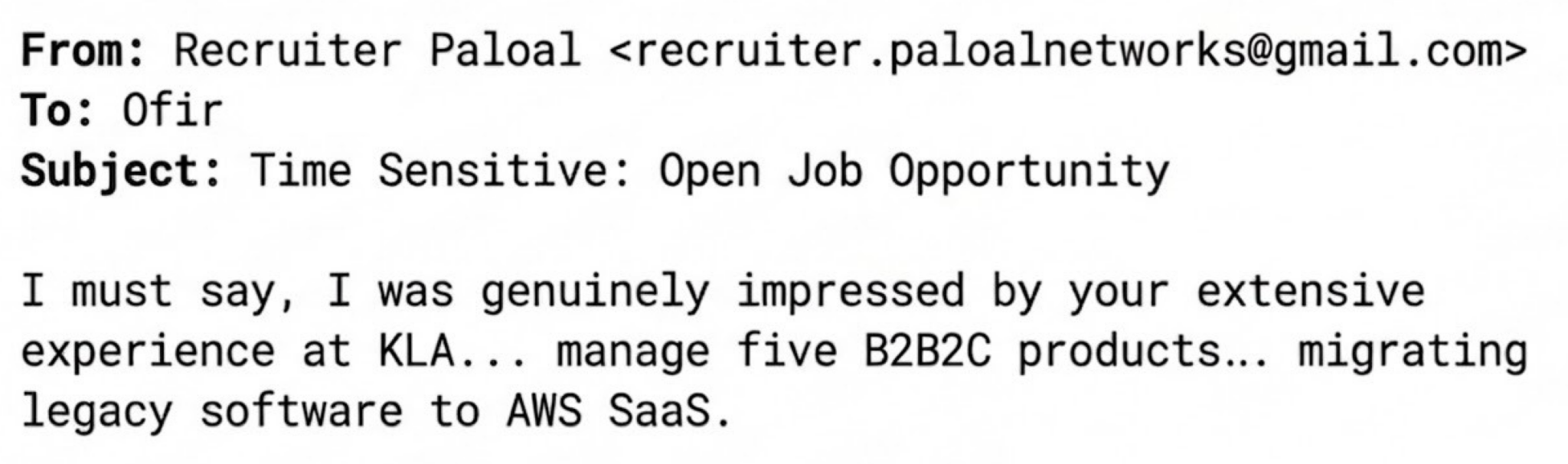
Multiple reported incidents have included phishing emails offering employment opportunities at Palo Alto Networks while masquerading as talent acquisition managers from the company. Examples are shown in Figures 1 and 2. The attacker uses:
- Flattering language
- Highly specific details from the victim's LinkedIn profile
- Legitimate company image logos in the email signature block
At this point in the interaction, the attackers manufacture a crisis, creating a bureaucratic barrier to the recruitment process. This psychological tactic increases the urgency and willingness of the victim to comply with the attacker’s offer of “executive ATS alignment” as shown below in Figure 3. The “recruiter” then hands off the exchange to the purported expert, who provides a structured offer at the following price points:
- Executive ATS alignment: $400
- Leadership positioning package: $600
- End-to-end executive rewrite: $800
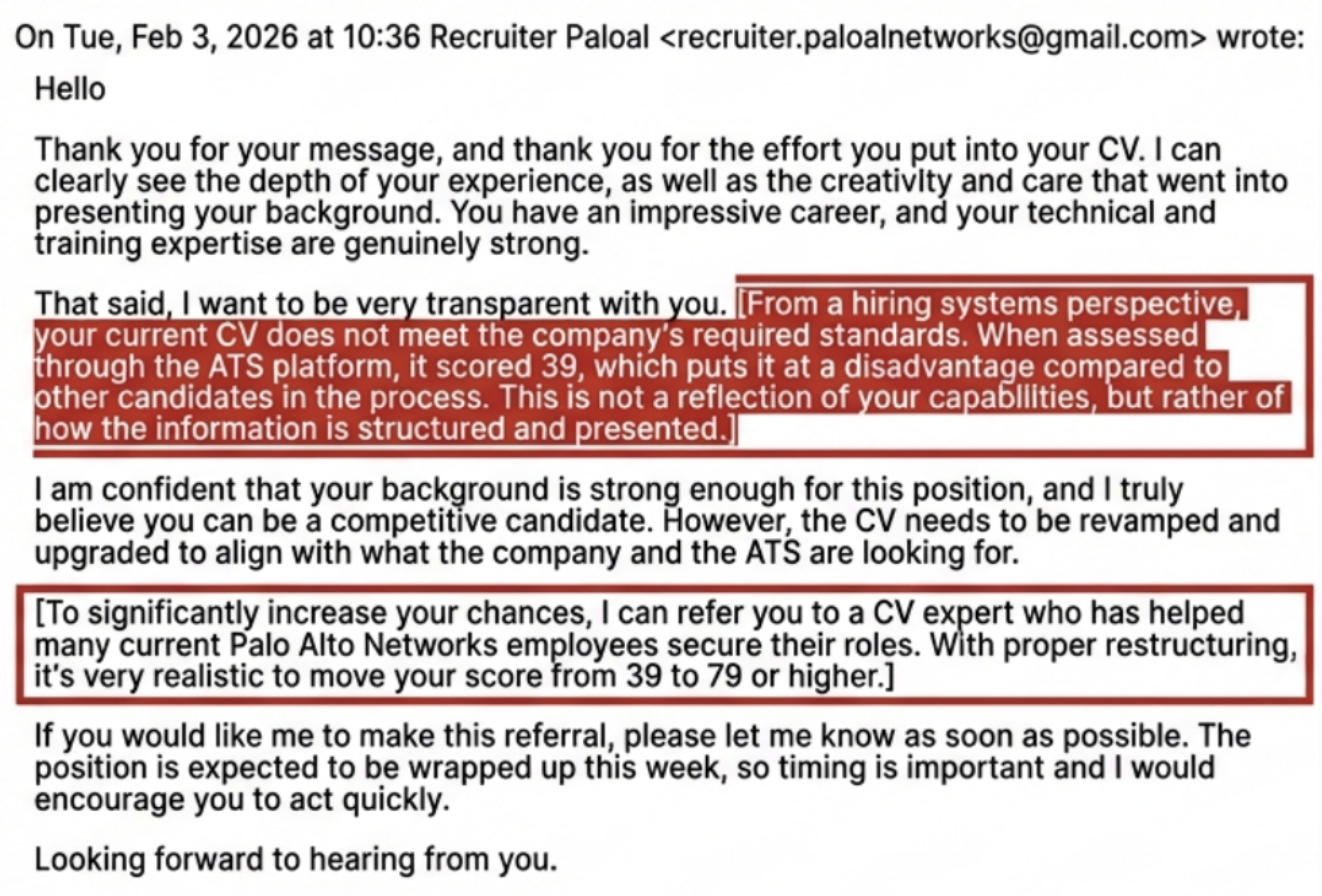
In reported incidents, the “recruiter” then implies that the “review panel” has already begun, and that the candidate needs to update their CV within a set timeframe. The “expert” then communicates that they can deliver the CV within only a matter of hours, which is within the ostensible review window.
Interim Guidance
We recommend that people who receive these phishing emails follow these security protocols to protect their professional identity and finances:
- Verify the sender's domain: Always check the suffix of the sender's email address. Scammers often use look-alike domains (e.g., @paloaltonetworks-careers[.]com instead of @paloaltonetworks.com).
- Request an official platform: If a recruiter contacts you on LinkedIn, ask to continue the conversation via an official corporate email or the company’s internal applicant portal.
- Zero-payment policy: Treat any request for payment during the recruitment process as an immediate red flag. Legitimate employers invest in talent, they don't charge them.
- Cross-reference the recruiter: Search for the individual on the official company website or LinkedIn. If their profile seems new, has very few connections or lacks a history at the company, proceed with extreme caution.
- Avoid suspicious attachments: Never download or open files with names like ATS diagnostic reports or Resume templates from an unverified source, as these often contain malware designed to compromise your device.
What to Do If You’ve Been Targeted
- Stop communication: Cease all contact with the individual immediately. Do not test them or engage further.
- Report the incident: Forward the phishing email to infosec at paloaltonetworks dot com.
- Flag on LinkedIn: Report the scammer’s profile to LinkedIn to help protect other professionals in your network.
- Secure your accounts: If you clicked any links, change your passwords and enable multi-factor authentication (MFA) on your email and professional accounts
Conclusion
At Palo Alto Networks, we are committed to a transparent and ethical hiring process. Please be advised that our talent acquisition team will never request payment for resume optimization, “executive ATS alignment” or any other “positioning packages” as a condition of employment.
These sophisticated scams weaponize the complexity of modern hiring by manufacturing artificial bureaucratic barriers and high-pressure review windows to solicit fees. If you receive an outreach that creates a sense of financial urgency or directs you to a third-party “expert” for a paid service, it is a fraudulent attempt to exploit your professional ambitions.
We encourage all candidates to verify the legitimacy of any communication by cross-referencing our official careers portal and to report suspicious activity immediately to our security team.
Palo Alto Networks customers are better protected by our products, as listed below. We will update this threat brief as more relevant information becomes available.
Palo Alto Networks Product Protections for This Activity
Palo Alto Networks customers can leverage a variety of product protections and updates to identify and defend against this threat.
If you think you might have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America: Toll Free: +1 (866) 486-4842 (866.4.UNIT42)
- UK: +44.20.3743.3660
- Europe and Middle East: +31.20.299.3130
- Asia: +65.6983.8730
- Japan: +81.50.1790.0200
- Australia: +61.2.4062.7950
- India: 000 800 050 45107
- South Korea: +82.080.467.8774
Indicators of Compromise
Emails associated with this activity:
- paloaltonetworks@gmail[.]com
- recruiter.paloalnetworks@gmail[.]com
- phillipwalters006@gmail[.]com
- posunrayi994@gmail[.]com
Handles associated with this activity:
- pelmaxx
- pellmax
- pelll_max
Phone number associated with this activity:
- +2349131397140 (Nigeria)
- +972 541234567 (Fake Placeholder)











 Get updates from Unit 42
Get updates from Unit 42