The latest development in the ransomware world is CryptoWall 2.0, a new version of this malware family that uses the Tor network for command and control.
F-Secure was the first to spot this new version on October 1, but since then the attacks have ramped up and new variants of the malware are emerging daily. Our WildFire analysis platform has picked up 84 CryptoWall 2.0 variants since September 30, delivered primarily through e-mail attachments but also through malicious PDFs and web exploit kits.
CryptoWall 2.0 is similar to other ransomware attacks that have plagued users and businesses for nearly a decade. Once it is running on a system, CryptoWall 2.0 seeks out document files and encrypts them using the RSA encryption algorithm. The attacker holds the key necessary to decrypt the files unless the victim agrees to pay a $500 ransom.
Unlike previous versions of CryptoWall, 2.0 communicates with its command and control (C2) server through the Tor anonymization network. This allows attackers to hide their communications and avoid having their C2 servers shut down, but also makes it easy for organizations to block the threat. CryptoWall isn’t the only threat that communicates over Tor and if your network doesn’t have an explicit reason to allow anonymization networks, you should consider blocking the application altogether with your firewall.
If your system has already been infected with CryptoWall 2.0, you’ll see a pop-up just like this one shortly after the malware has encrypted your documents.
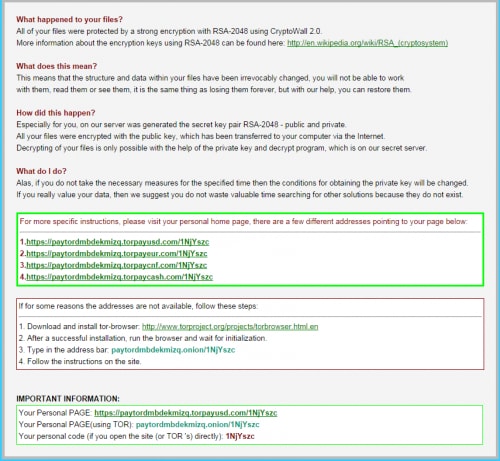
Note that the attacker has given you a few options for how to pay them the ransom. The green box contains four links that will work only for your system. These use four domains registered just today:
- torpaycash.com
- torpaycnf.com
- torpayeur.com
- torpayusd.com
All of the domains currently resolve to 151.248.115.146, a Russian IP address and have WhoIs records associated with the e-mail address “ladomfichisi1987@mail.ru”. This is the same address used to register two other payment domains registered earlier this month:
- tor2pay.com
- tor4pay.com
If these domains are confiscated or otherwise shut down, CryptoWall instructs the user to download the Tor Browser and access a website (paytordmbdekmizq.onion) that is only accessible over the Tor network.
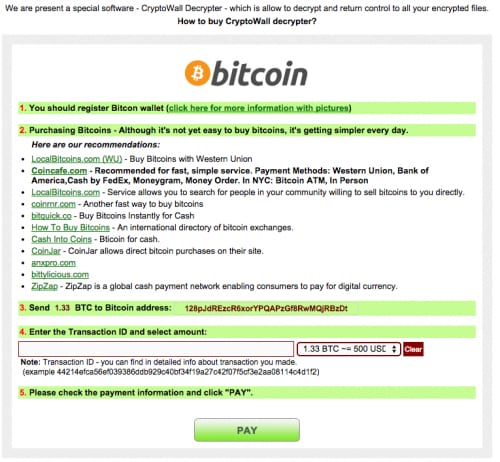
Unlikely some of it’s more flexible competition, CryptoWall only accepts ransom in the form of BitCoin. To pay the ransom the user will need to acquire 1.33 BitCoins and transfer them to a specific BitCoin wallet that is associated with their specific infection.
History has shown that paying the ransom will likely allow you to retrieve your files, but the best defense against ransomware is having up-to-date back-ups or by preventing the infection all-together.
Infection Vectors
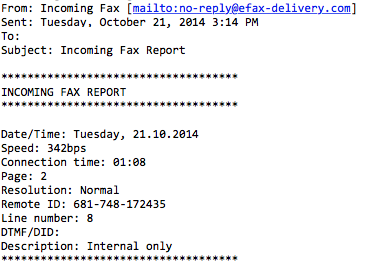
Since we detected the first CryptoWall 2.0 variant with our WildFire engine on September 29, we’ve seen over 85,000 separate attacks attempting to deliver the malware. The majority of these have come through e-mails with executable attachments, sometimes contained in .zip files. Most of the e-mail attacks used fake invoice, fax and voicemail themes with attachments named like the following:
- Complaint_IRS-Id-12839182.scr
- fax00415741732781728.scr
- VOICE387-778-3454.zip
- CH_Import_Information.exe
In the last week we’ve seen the attack vectors evolve to contain exploit kits as well. On October 19, the Kafeine posted a blog discussing the inclusion of CVE-2014-0556 in the Nuclear Pack exploit kit, which was installing CryptoWall 2.0.
Yesterday we picked up an e-mail campaign pretending to be a fax report that carried a .zip attachment with a PDF inside. The PDF exploits CVE-2013-2729 to download a binary which also installed CryptoWall 2.0.
Protecting Yourself
The best way to protect yourself against ransomware is to keep up-to-date backups of your important files. A ransomware infection, which encrypts all of your files, is similar to a drive failure, except that for a small fee you have the chance to get your files back.
To protect against CryptoWall 2.0 we recommend taking the following actions:
- Block downloads of executable files from the web without specific user consent.
- Add a ‘continue’ page for all file downloads that can provide a reminder to users before they automatically install potentially impacting software.
- Employ an advanced detection system (like WildFire) to analyze all incoming executables, PDF files, and Microsoft Office Documents.
- Consider blocking the Tor application completely within your network unless it’s absolutely necessary.
- Ensure that only necessary users have write-access to network shares. CryptoWall will encrypt files in network shares if the share is mounted at the time of infection and accessible to the logged-in user.
- Disconnect or unmounts back-up drives when they aren’t being used, as CryptoWall can also encrypt your backups.
- Consider deploying an end-point protection system (like Traps) that prevents exploitation of known and unknown vulnerabilities.
- Deploy IPS signatures to detect CVE-2014-0556 and CVE-2013-2729 exploitation. For Palo Alto Networks IPS users these include:
| Sig ID | Name | CVE ID |
| 35811 |
Adobe Reader Embedded BMP Parsing Integer Overflow Vulnerability |
CVE-2013-2729 |
| 36762 | Adobe Flash Player Memory Corruption Vulnerability |
CVE-2014-0556 |
| 36763 | Adobe Flash Player Memory Corruption Vulnerability | CVE-2014-0556 |
| 36764 | Adobe Flash Player Memory Corruption Vulnerability | CVE-2014-0556 |
| 36754 | Adobe Flash Player Memory Corruption Vulnerability | CVE-2014-0556 |












 Get updates from Unit 42
Get updates from Unit 42