Executive Summary
On Oct. 16, 2023, Cisco published a security advisory detailing an actively exploited privilege escalation zero-day vulnerability impacting Cisco IOS XE devices. The vulnerability (CVE-2023-20198) has a criticality score of 10, according to the National Vulnerability Database, and it would allow an attacker to create an account with the highest privileges possible.
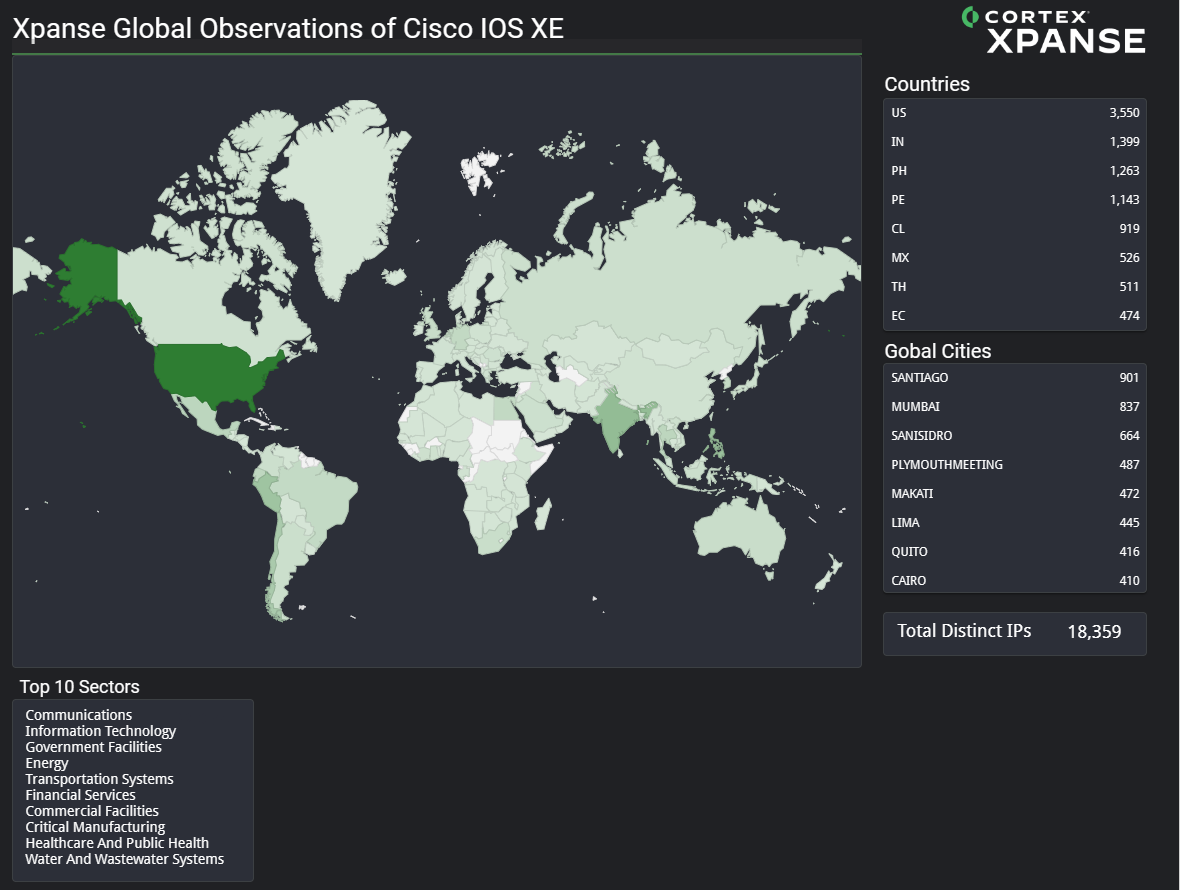
According to our attack surface telemetry from Cortex Xpanse, analysts observed 22,074 implanted IOS XE devices on Oct. 18, 2023. Telemetry as of Oct. 19, 2023 shows 18,359 impacted devices, and we expect the number to continue to decrease as the implant is no longer persistent. (Note: Implant is a term commonly used to describe a backdoor or malware.)
Cisco recommends customers disable the HTTP Server feature on all internet-facing systems or untrusted networks.
Palo Alto Networks customers receive protections from and mitigations for the Cisco IOS XE Web UI Privilege Escalation Vulnerability in the following ways:
- Next-Generation Firewall with Advanced Threat Prevention security subscription should use best practices via the following Threat Prevention signatures:
- Organizations can engage the Unit 42 Incident Response team for specific assistance with this threat and others.
- Cortex Xpanse has the ability to identify exposed Cisco IOS XE devices on the public internet and escalate these findings to defenders. These findings are also available for Cortex XSIAM customers who have purchased the Attack Surface Management (ASM) module.
Palo Alto Networks also recommends following Cisco’s guidelines for all IOS XE devices.
| Vulnerabilities Discussed | CVE-2023-20198 |
Details of the Vulnerability
Cisco disclosed a privilege escalation zero-day vulnerability on Oct. 16, 2023. This vulnerability impacts the Cisco IOS XE web user interface. If this feature is enabled, an attacker can create a new account with the highest privileges (level 15, full administrative access).
A non-persistent implant based on the Lua programming language has been observed in use alongside this vulnerability. The web server must be restarted for the implant to become active, according to Cisco Threat Intelligence.
Current Scope of the Attack
According to attack surface telemetry from Cortex Xpanse, on Oct. 18, 2023, analysts observed at least 22,074 hosts containing the Lua-language implant. As of Oct. 19, that number had decreased to 18,359 affected devices, and we expect this number to continue to decrease as the implant is no longer persistent. Figure 1 below shows a global heatmap displaying the potential global impact based on the unique IPs, as well as the top 10 affected sectors.
Interim Guidance
Cisco recommends customers disable the HTTP Server feature on all internet-facing systems or untrusted networks as the primary workaround solution for this vulnerability. Cisco’s Threat Intelligence team has provided checks and recommendations for this vulnerability.
Conclusion
Based on the amount of publicly available information, along with our own analysis, Palo Alto Networks recommends following Cisco’s recommendations immediately. For all potentially impacted organizations, we also recommend reviewing your systems for signs of a backdoor implant installation and new user account creation.
Palo Alto Networks and Unit 42 will continue to monitor the situation for updated information, release of proof of concept code and evidence of additional exploitation.
Palo Alto Networks has shared our findings, including file samples and indicators of compromise, with our fellow Cyber Threat Alliance (CTA) members. CTA members use this intelligence to rapidly deploy protections to their customers and to systematically disrupt malicious cyber actors. Learn more about the Cyber Threat Alliance.
Palo Alto Networks customers receive protection from our products, as listed below. We will update this threat brief as more relevant information becomes available.
Palo Alto Networks Product Protections for Cisco IOS XE Privilege Escalation Vulnerability
Palo Alto Networks customers can leverage a variety of product protections and updates to identify and defend against this threat.
If you think you might have been compromised or have an urgent matter, get in touch with the Unit 42 Incident Response team or call:
- North America Toll-Free: 866.486.4842 (866.4.UNIT42)
- EMEA: +31.20.299.3130
- APAC: +65.6983.8730
- Japan: +81.50.1790.0200
Next Generation Firewall With Advanced Threat Prevention
Next-Generation Firewall with the Advanced Threat Prevention security subscription can help block the associated attack and implant’s C2 traffic with best practices via the following Threat Prevention signatures: 86807, 94454
Prisma Cloud
The Cisco IOS XE software can be deployed on cloud resources via the Cisco Catalyst 8000V series. The latest version of the Catalyst 8000V (v17.9.4a) addresses CVE-2023-20198, Prisma Cloud recommends that all users of this virtual firewall upgrade immediately.
Prisma Cloud is a SaaS security solution with the capability to detect vulnerabilities and misconfigurations within Cloud Resources. If upgrading to the latest version of Catalyst 8000V is not possible, Prisma Cloud can be used to monitor the cloud instances' cloud service access to ensure secure operation. At a minimum the usage of Prisma Cloud's Anomaly, Config, and Network policies should be employed to alert organizations of suspicious operations.
Cortex Xpanse and XSIAM
Cortex Xpanse has the ability to identify exposed Cisco IOS XE devices on the public internet and escalate these findings to defenders. Customers can enable alerting on this risk by ensuring that the "Cortex IOS XE" Attack Surface Rule is enabled. Identified findings can either be viewed in the Threat Response Center or in the incident view of Expander. These findings are also available for Cortex XSIAM customers who have purchased the ASM module.
Updated October 19, 2023, at 12:25 p.m. PT to update heat map, number of affected devices and telemetry source.
Updated October 24, 2023, at 8:58 a.m. PT to add Cortex Xpanse product protections.
Updated October 24, 2023, at 1:38 p.m. PT to revise Prisma Cloud product protections.












 Get updates from Unit 42
Get updates from Unit 42