Introduction
To understand the full scope of the current IoT threat landscape, we analyzed 1.2 million IoT devices in thousands of physical locations across enterprise IT and healthcare organizations in the United States in 2018 and 2019. Using the Palo Alto Networks’ IoT security product, Zingbox, we created the 2020 Unit 42 IoT Threat Report to identify the top IoT threats and provide recommendations that organizations can take to immediately reduce IoT risk in their environments.
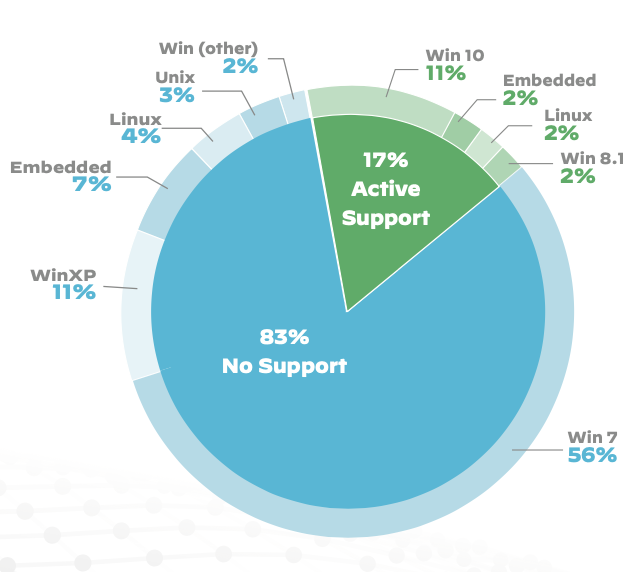
Most notably, the report reveals that 83% of medical imaging devices are running on unsupported operating systems. This reflects a 56% jump from 2018 due to the Windows 7 operating system reaching its end of life, leaving hospital organizations vulnerable to attacks that can disrupt care or expose sensitive medical information.
Key Findings
Emerging Trends
High-profile, IoT-focused cyberattacks are forcing industries to recognize and manage the risks associated with deploying IoT devices to protect their core business operations. Industries, such as healthcare, are exposed to an incredibly unexpected amount of risk. Unfortunately, some IoT vulnerabilities can be life-threatening, while some attack critical enterprise functions or exfiltrate confidential data. While conducting this research, these are some of the emerging trends we discovered that organizations need to be aware of.
-
- 98% of all IoT device traffic is unencrypted, exposing personal and confidential data on the network and allowing attackers the ability to listen to unencrypted network traffic, collect personal or confidential information, then exploit that data for profit on the dark web.
- 51% of threats for healthcare organizations involve imaging devices, disrupting the quality of care and allowing attackers to exfiltrate patient data stored on these devices.
- 72% of healthcare VLANs mix IoT and IT assets, allowing malware to spread from users’ computers to vulnerable IoT devices on the same network.
Top IoT Threats
Threats continue to evolve to target IoT devices using new sophisticated and evasive techniques, such as peer-to-peer command and control communications and worm-like features for self-propagation. Coupled with a weak device and network security posture, attackers have ample opportunity to compromise IoT systems.
-
- 57% of IoT devices are vulnerable to medium- or high-severity attacks, making IoT the low-hanging fruit for attackers.
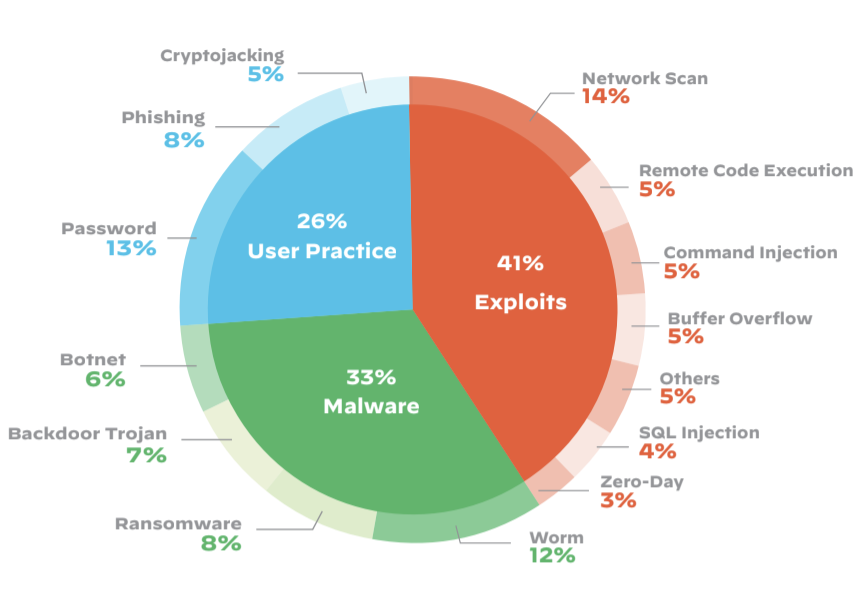
- 41% of attacks exploit device vulnerabilities, as IT-borne attacks scan through network-connected devices in an attempt to exploit known weaknesses.
We found that, while the vulnerability of IoT devices make them easy targets, they are most often used as a stepping stone for lateral movement to attack other systems on the network. Furthermore, we found password-related attacks continue to be prevalent on IoT devices due to weak manufacturer-set passwords and poor password security practices. However, with California’s SB-327 IoT law taking effect on January 1, 2020, prohibiting the use of default credentials, we expect this trend to change direction.
We’re also witnessing a shift away from attackers’ primary motivation of running botnets to conduct DDoS attacks via IoT devices to malware spreading across the network via worm-like features, enabling attackers to run malicious code to conduct a large variety of new attacks.
Steps to Reduce IoT Exposure
According to a 2019 report by Gartner, “By the end of 2019, 4.8 billion [IoT] endpoints are expected to be in use, up 21.5% from 2018.” With such a significant increase in adoption that shows no signs of slowing down, organizations need to be prepared with a strong IoT security strategy. Our report shows there are a myriad of ways enterprises are being left vulnerable to security threats, which can easily lead to some very dire circumstances if exploited.
There are steps that can be taken immediately, however, to reduce exposure to IoT threats:
-
- Know your risk. Discover IoT devices on the network.
- Patch printers and other easily patchable devices.
- Segment IoT devices across VLANs.
- Enable active monitoring.
Get the full 2020 Unit 42 IoT Threat Report for more research and best practices to implement in your organization.












 Get updates from Unit 42
Get updates from Unit 42